I’ve written about this before: the design methodology used to produce the F-35 makes it nearly impossible to maintain any kind of secrecy regarding its technology.
The whole design approach for the F-35 program is “distributed pork” including some components of the aircraft that were originally to be made in Turkey back when the US was still trying to lure Turkey into NATO as an ally. Because of the high maintenance requirements for the plane’s engine, there were going to be multiple engine maintenance facilities, worldwide, creating a situation in which Saudi F-35s (if there were ever such a thing) would have to fly to Turkey for maintenance. Obviously, that was an utterly stupid idea; nations that made a large investment in F-35s, such as Israel, have their own domestic engine manufacturing capability, and the US generally pays them to buy F-35s in the first place, in order to make the jet an acceptable deal. [It was hard to construct a sentence that carried forward that concept in its full splendor; that’s why I deliberately made that sentence awkward and stupid-sounding]
So, the idea was that the Turkish aerospace industry was going to get all of the necessary information to build/maintain F-35s. Probably not just the engine; there’s that delightfully peel-able stealth coating, too. This amounts to a great big whacking pile of secret technology, delivered to allies of questionable loyalty. Then, the US complains loudly that China has stolen that information, because their spies are so aggressive. I used to know a few of the guys from the Air Force Warfare Integrating Capability (AFWIC) who did some of the investigation into the F-35 CAD documents’ leak of 2007 [mashable] and they said “terabytes” of documents leaked from a Turkish aerospace firm with a development relationship between Lockheed Martin. The aircraft is designed to be built piece-wise, farmed out to aerospace concerns in multiple nations, and that’s supposed to be kept secret? The US can’t even keep information about the F-35 secret, such as the 2015 leak of Air Force documents about what a lousy combat aircraft the F-35 is [pogo]; are we supposed to believe that Chinese spies are so skilled that they read the internet? What fascinates me about this stuff is the question of the vague line between information being “published”, “leaked”, and “stolen.” I know security practitioners who would say that data in the cloud is not “published” or “leaked” but in my opinion, once information is pushed out of the custodian’s governance, it has been “published”. To me, that is the definition of “publishing” something: you put it out where you no longer control its release. It doesn’t matter if you put it on amazon’s storage cloud, or pastebin – you’ve given up control and, with data, loss of control is irrevocable. There are probably people who would disagree with that last point, but they’re mostly the kind of tech-ignorant DoD-types who’ve caused the problem in the first place. Literally, there were people in the US government that wanted to demand the Chinese return the F-35 data. “Uh, here are your bits. 1tb. Sorry,” said some Chinese intelligence officer.
All of this is context for the latest news about F-35 leakage: [Eurasian times]
Honeywell was found to be indulged in unauthorized “exports and retransfers of ITAR-controlled technical data that contained engineering prints showing dimensions, geometries, and layouts for manufacturing castings and finished parts for multiple aircraft, gas turbine engines, and military electronics to and/or within Canada, Ireland, Mexico, the People’s Republic of China, and Taiwan,” according to the US Government.
In the claimed “settlement”, the company is required to pay $13 million in civil penalties and other things, $5 million of which was immediately suspended on the condition that Honeywell used it towards “remedial compliance measures”.
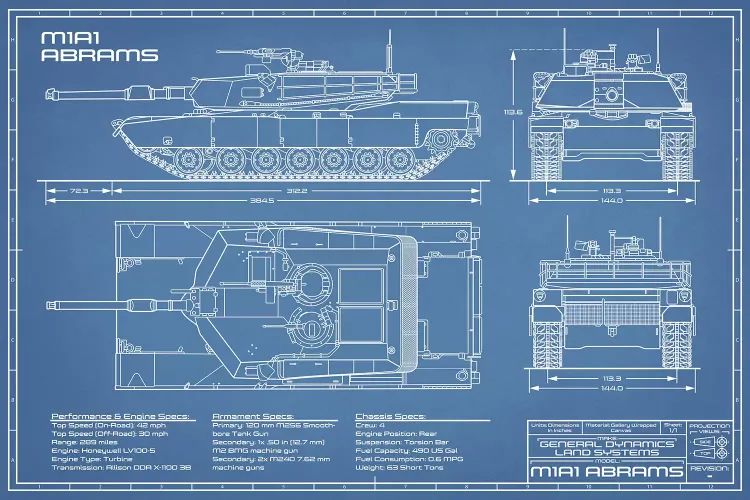
I know, that’s not a real blueprint
In other words, the fine just became “the amount we expect you to spend on improving your computer security”
The US government, however, chose to be a little lenient with the company as it ‘voluntarily’ disclosed the violations to the state department.
The development assumes significance given that the West, especially the US, has accused China of industrial espionage in the past.
The leaked “engineering drawings” showing technical data pertained to America’s most expensive fighter jet F-35 Lightning II besides the F-22 Raptor, B-1 Lancer Strategic Bomber, C-130 Transport Aircraft, A-7H Corsair, A-10 Warthog, AH-64D Apache Longbow, M1A1 main battle tank, Tomahawk cruise missile, and T55 turboshaft engine used in CH-47 Chinook and its variants are even used in the latest SB-1 Defiant.
The latest data leak to China, even when its spies have been previously apprehended by authorities for stealing confidential data from American companies, raises a serious concern — even though it’s uncovered voluntarily or involuntarily.
“Here, rather than sort all the data out, we’ll just ship you a tarball of everything we’ve got, OK?” That’s, basically, “the entire store.” Jet engine designs are particularly interesting because they are extremely expensive to design and any information that can improve progress will result in gigantic cost-savings. What this illustrates is a complete failure of compartmentalization – instead of maintaining secrets about programs in separate stacks, the whole thing was wadded together and disclosed all at once. “Way to go, guys!”
I used to think of secrecy as an absolute state; once something was disclosed, that’s it, game over. But later I was talking with another information security practitioner who’s also familiar with aerospace engineering and he said it’s much worse than I thought. Consider a set of system design documents as a description of an engineering process at a given point in time. So, if you leak that description in 2007, and again in 2011, an analyst who understands aerospace engineering can see where there have been changes and where the design is being worked on the most. Where are there improvements and fixes? What do the changes mean? We had the exact same problem in software security: every time Microsoft released a patch, it meant that security researchers could pinpoint what function of the code had been fixed by comparing it to the previous version – then it’s a ‘simple’ matter of figuring out what, exactly, got fixed, and why. You could learn not just how a jet engine is made, but also what are the tricky parts and some solutions to those tricky parts that have been applied over time.
There is some interesting stuff in The Yard [wc] regarding the amount of detailed design documents that cover the production of an Arleigh Burke-class destroyer; it was something like 16 freight train cars full if you printed it all out. Those terabytes cover everything including the exact dimensions (and likely CAD files) for the custom-machined toilet seats that cost $65,000 apiece. The book explains that those toilet seats cost that much because they’re for toilets that are shoehorned into weird available spots in the ship, where a normal toilet seat would jam against a wall if it were lifted. So, someone had to design seats that were unique to each toilet, and had to take into account the other features of the room – a process that required weeks of work and updates every time any aspect of that part of the ship was changed. I am not an aerospace engineer but my impression is that a jet fighter has similar design constraints – any change has a ripple effect that changes many other things and the consequences are dire. There’s some great description in The Yard regarding the effect on a ship’s balance of having a little bitty (multi-tonne) missile move from a magazine to a launcher, and what that means if the ship is rolling in rough water; fascinating stuff.
Having access to this sort of information about cutting edge aircraft is useful in many ways, including designing commercial systems. So, it’s a big deal in terms of potential economic impact; for example, Brazilian aircraft maker Embraer would not have started with a completely blank slate; they’d have hired a few designers from Boeing or Lockheed Martin. That’s how, generally, industrial espionage has been done for hundreds of years: you hire the engineers who know the things. I used to joke, “You know how to steal intellectual property from American companies? You ask the board of directors.” Google, Amazon.com, and Microsoft all deal with this issue – governments are constantly demanding access to technology that would otherwise be considered sensitive. I remember back in the day, when Blackberry was under threat from the Indian government, which wanted access to its cryptographic keys. The cryptographic keys for a system like that are its “crown jewels” yet Blackberry shamelessly threw all of its customers under the bus, in order to open India as a market. [RIP Blackberry] Microsoft sent a copy of the complete Windows source code to the Chinese government extremely quickly when China started making rumbles about blocking Microsoft’s ability to sell into their market. All of this information is useful and valuable, but that means it’s subject to negotiation, not that it’s secret.
I have to admit that there have been times I’ve thought, “how hard would it be…?” and considered attempting to score myself a copy of these legendary F-35 CAD files. I used to hang out with people who have been on both the defensive and offensive side of the acquisition and protection of such data – I bet that I could make a few phone calls and have a pretty good roadmap for where to start. And, I have terabytes of storage. Also, I live under metered bandwith, here in Verizon hell, and it’d only cost me about $10,000 [no joke] to download that much data. Thus, Verizon’s predatory pricing helps protect national security.

A $13mn fine for Honeywell isn’t even a slap on the wrist, basically it just ate their profit margin for whatever program it was that leaked the data. That’s surely going to have a huge impact in terms of deterring contractors from having poor security in the future. /sarc

Reading this gave me a terrific idea: design and build custom toilet capabilities into the flight seat of jets like the F35. The uh, detritus could then be stored and flung at an opponent aircraft or missile in action. Poo-flinging meets the jet age! Of course you wouldn’t want to try to bill the USAF for custom toilet seats, or poo-flingers; so you would call it something like “biological counter-measures.”
That reminds me of a story I heard 30 years ago from a fellow who worked at Lawrence Livermore. They were working on some technology which was classified, and then some of the published journals the lab subscribed to wrote cover stories about precisely the technology they were working on. When those editions of the journals were received by the lab, which were generally put in the break room for causal reading, lab security confiscated them because they contained ‘classified’ material. A journal anyone could purchase at a good newstand had material too classified to allow the researchers with security clearances who worked in the subject to read.
Eventually a compromise was made. The covers were removed, but the journals were allowed to be in the break room.
Now I understand that lab security was doing their job. They are not paid to think, but to enforce the rules. But it should have been a simple matter to explain the situation to someone who can think and has the power to adjust the rules to at least make an exception in cases where the classified information has become public.
What fascinates me about this stuff is the question of the vague line between information being “published”, “leaked”, and “stolen.”
Perhaps it is a matter of declension – “I publish”, “you leak”, “they stole”…?
(sarcasm!)
There are some very rare times when I would like to “thumbs-up” a comment.
This was one of them.
Having watched videos of Hillary Clinton, Madelaine Albright and Joe Biden’, I am perfectly willing to assume that US citizens assume the Chinese –or the rest of the world–cannot access the internet.
@1 follow-up: So then when someone says “Our biological counter-measures leaked,” you will not be entirely sure what they mean by it.
I bet I could design a potty seat for half that price (snicker).
IMHO there is a nascent trend for war planners to see weapons as commodities. As products become more developed they start to look the same. You can see this easily on the roads where the requirements for a car are nearly universal (range, performance, cost) and the engineering and physics, applied over narrow developmental paths, tend to create a situation where most cars look the same.
We have seen this, in a big way, with the B-52 and several Russian bomber models where the basic requirement is for a flying dump-truck. The army has long ago given up on thinking only US designs of small-arms has the secret sauce.
Any edge given by weapons development tends to be short-term. Example: The Sidewinder was really innovative and a significant advantage but when one ended up lodged in the tail of an enemy aircraft, the warhead having failed, the secrets were lost. It didn’t take long for Russians to develop their own version.
Further, on mature technologies, like jet engines we spend huge sums of money gaining a few percentage points in performance. And it isn’t really all that creative. Every engineer knows which parts need to be optimized. Yes, it takes thousands of hours of super-computer time and some more time proving the optimization in a wind tunnel but everyone knows where to look, what has to be done, and how to do it. All for a .05% improvement.
The big improvements, ones large enough to be decisive, were made long ago. We are down to apple polishing.
I also suspect that the F-35 program, and a lesser extent the F-22, are technological head-fakes. I think the next transformational technology will be semi-autonomous drones. And drones hunting drones. China builds F-35s and we show up with drones optimized to destroy F-35s.
Cutty Snark @ 3: the original rhetorical trick attributed to Bertrand Russel, but this particular I think is Yes, Prime Minister:
“That’s another of those irregular verbs, isn’t it?
I give confidential press briefings; you leak; he’s being charged under section 2A of the Official Secrets Act.”
(thanks as ever to Wikipedia to help my foggy memory)
@2 I can do you one anecdote better. At one time during my tenure on a contract on-base, the Washington Post published some classified stuff or other. Site security actually demanded that anybody who’d read that article on their home computer had to bring it in for them to “wipe the classified off of it” – Oh, and all your files, too. Needless to say, hardly anybody admitted to reading it at home XD
But I shit you not. True story.