Willie Sutton robbed banks “because that’s where the money is.”
And, the US surveillance state collects information about you where it’s stored – inside whatever defenses the data’s owner may have tried to put in place. With the gigantic and confusing number of providers who pass around information, it just becomes a question of figuring out where the biggest and most up-to-date repository is, then presenting them with a classified “National Security Letter”
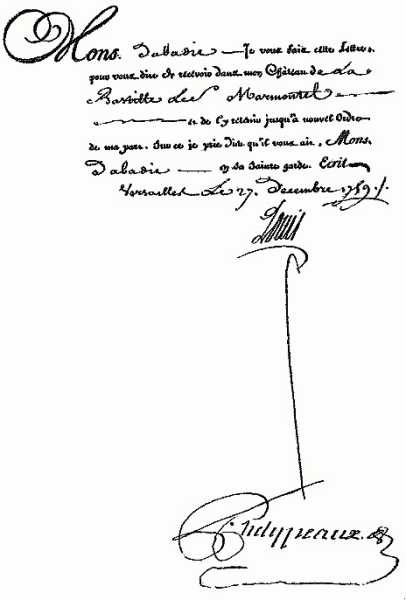
A “lettre de cachet” signed by Louis XV, ordering one of his subjects to be arrested and sent to the Bastille
It’s what Spinoza referred to as “secret diplomacy” – when the government privileges itself to operate in secret, it quickly goes out of control. In fact, I would say that when the government begins to act in secret, that is the very definition of “out of control.”
You probably remember the US 4th amendment, which reads:
The right of the people to be secure in their persons, houses, papers, and effects, against unreasonable searches and seizures, shall not be violated, and no Warrants shall issue, but upon probable cause, supported by Oath or affirmation, and particularly describing the place to be searched, and the persons or things to be seized.
That’s a bit more relevant when you realize that most of the US’ “founding fathers” were smugglers or slavers (slavery being illegal but not enforced in the colonies) – so their concern makes sense: they didn’t want the government knowing what they were up to in the dark.
The 4th has probably been more honored in the avoiding of it, than in its own right. During WWI and WWII the 4th was immediately shitcanned, as the government (“gentlemen don’t read eachother’s mail”) began diverting international mail for analysis, and – basically, they never stopped. It’s just gone high tech.
You should assume that anyplace where you have data stored, the FBI will either be accessing it through National Security Lettres De Cachet, or the NSA will figure out a way of intercepting it or stealing it outright. I have mentioned this before, but: you should ignore all of the vendors’ claims of encryption and security in data stores; that’s all posturing. A vendor that actually provided a service that locked the FBI out, like Lavabit, would come under such pressure as to be either unable to operate, or forced to cave in. [guard] This brings about what I think of as “the crypto catch-22” – if you can use it, that means it’s compromised or they wouldn’t let you use it.
Forbes discloses that the FBI is inside of SABER online reservation system. You know those weird cryptic computer terminals that the gate agents used to use for scheduling and transferring your flight to another carrier when a flight gets canceled? That’s SABER. The airline seating and passenger management component has to be unified or it wouldn’t work because of transaction collisions; the airlines are basically front-end user interfaces for SABER. It’s the natural place to be, since it provides a view of everything:
[forbes]
American border patrol already has significant surveillance powers and collects vast amounts of data on who is flying into and out of the country. But the U.S. has another tool to watch over travellers across the world thanks to a little-known but influential Texan business called Sabre. As the biggest of three companies that store the vast majority of the world’s travel information – from airline seats to hotel bookings – Sabre has been called on to hand over that travellers’ data and, on at least one occasion, do “real-time” tracking of a suspect. And, say former employees, the same powerful trove of information could be used to help monitor the spread of the Covid-19 pandemic.
One thing jumps out at me right away: real-time tracking. That’s something that an airline generally would not need, but it’s a capability that needs to be programmed into the system and provided with a command interface. Someone did not just walk over to a keyboard, like they do in 24 and type it in – a capability like that needs to be designed, embedded into the proper parts of the data path, and outputs need to be defined, etc. This is not a new thing, in other words. The FBI is probably loading big chunks of the anti-terror watch list into the tracking system. Perhaps that’s how they are figuring out who to take aside for “detailed searching.”
Publicly, Sabre’s entanglement with the U.S. government has been apparent for some time. Former CEOs have given testimony to Congressional panels and made it onto presidential committees. Then there’s the secret side of the relationship. Stretching back to at least the 2001 September 11 terror attacks, the government has, on numerous occasions, secretly asked the company to actively spy on suspects’ movements, in both major and minor criminal cases.
Only three tracking orders? That’s literally unbelievable. The FBI is incapable of keeping their hands off of such a valuable tool. I suspect we are looking at how they caught Lev Parnas at the airport when he was trying to leave the country.
The order is one of at least four where Sabre agreed to provide such traveller information. In 2015, the FBI was hunting down Aleksei Yurievich Burkov, whom investigators believed was running Cardplanet, a $20 million bazaar for buying and selling stolen credit card data. To track him down, the U.S. government told not just Sabre, but also the U.K.-based, New York Stock Exchange-listed Travelport to provide records on the Russian. That’s according to a brief note on the court docket (a list of events in the course of a court case) for the Burkov case. Further details are under seal. Burkov was extradited from Israel in November 2019 and pleaded guilty to charges of fraud, identity theft, computer intrusion, wire fraud and money laundering in January.
The latest order on Sabre also notes the company had previously complied with three similar orders to “assist in effectuating arrest warrants”: two in the Western District of Washington in 2017 and 2019, another in the Northern District of California in 2016. Again, the documents remain under seal.
The documents are under seal because if they were disclosed that would demonstrate that the FBI had engaged in “parallel construction” on certain cases. That is to say: they manufactured evidence so that they could keep the actual source of the information secret. The judicial system has come to accept “parallel construction” as a legitimate technique but it’s fabrication of evidence, no matter how you slice it.
Assume that every place where data is stored about you, or by you, that it is subject to offline attack. Except you can’t even call handing it over, “here ya go!” without any resistance an “attack.”

Rep Larry Householder, who was just arrested for some apparently spectacular corruption, is doubtless a good case study of parallel construction: [usatoday]
“It was a very covert investigation,” said U.S. Attorney David DeVillers. “I am not going to get into the means of our investigation, but it was critical that we, as the U.S. Attorney’s Office and the FBI, kept this a secret…”
There’s likely more to come in the case, with investigators urging anyone with any information to contact the FBI’s tip line at 614-849-1777.
“It has now changed from a secret investigation to an overt investigation,” DeVillers said. “We are not done with this case. There are things we couldn’t do before, people we couldn’t interview, people we couldn’t subpoena, documents we couldn’t subpoena, search warrants we couldn’t execute… As of this morning, there are a lot of FBI agents knocking on a lot of doors asking a lot of questions, serving a lot of subpoenas, executing a lot of search warrants.”
In other words: the initial investigation was done offline, by analyzing emails and txt messages, etc. By the time they were done, they had a good enough picture of what was going on, and knew where all the bodies were buried – then they could arrest him and start executing search warrants. Search warrants which will be very effective because they already know where the evidence is.

Anybody want to bet that the same sort of “constitutional originalists” who insist that the “right to bear arms” obviously includes AR-15s with bump stocks and extended magazines will also argue that the “right of the people to be secure in their persons, houses, papers, and effects” obviously doesn’t include digital records? Heck, I can even sketch out the argument – “arms” is a general term and can be assumed to extend to more recent invovations, whereas “persons, houses, papers, and effects” is a list of specifics, and therefore cannot be extended to other similar things that couldn’t have been imagined at the time. Rules lawyering FTW!
I do find mild encouragement in the Householder bust. This was a takedown of Republican politicians in an election season. It gives me small hope that there may be one or two federal agencies that have not been completely corrupted by Trump.
re Reginald Selkirk @2: YET!11!11 THEY ARE ON THE LIST!!!!!111!
Reginald Selkirk@#2:
I do find mild encouragement in the Householder bust.
I did, too, then I remembered how the FBI works. What we’ve probably got is a supervisory special agent in some field office who actually did want to make a stand against what appears to be a remarkably corrupt lawmaker. They have a fair amount of independence in who and how they investigate corruption – but what remains to be seen is whether Bill Barr is going to come swooping in like wrongo-world batman and fuck up their case, and fuck up the SSA who led the investigation. I’m sure that the SSA probably also figured that, and figured that if they nailed the guy now, it’d be an election season issue if Barr does that. If the republicans get slaughtered in the election, as we all hope they do, it won’t matter and Householder will decorate some prison cell for a few years, but if they don’t it won’t matter, either, and Householder will be rehabilitated after the case against him quietly falls apart and DOJ declines to pursue it further.
slavery being illegal but not enforced in the colonies
Eh?