In the wake of the latest terror attack, Theresa May was quick to begin banging the surveillance state’s favorite rhythm.
As I discussed [stderr] following the previous attack, governments are not going to miss an opportunity to increase their control in the name of security:
“Some people say that it is not for government to regulate when it comes to technology and the internet. We disagree.” [cnn]
I do agree that government ought to regulate when it comes to technology: it ought to be concerned with consumer privacy, system security, protection of customer data, and overall system reliability. It is rank nonsense of the finest vintage to throw up some straw man that people don’t want regulation – when we obviously do – and then simultaneously dismiss that while attacking privacy. And she didn’t even wait until all the bleeding had stopped and the bodies were cold.
“We need to work with allied democratic governments to reach international agreements that regulate cyberspace to prevent the spread of extremist and terrorism planning,” she said in a speech. “We need to do everything we can at home to reduce the risks of extremism online.”
The prime minister said internet companies provide extremist ideology “the safe space it needs to breed.” Google, Apple, Facebook, Microsoft and many other services have created encrypted channels that may shield communications from law enforcement.
Relax and have a homebrew
It’s funny how fast governments forget their pretended belief in capitalism and free markets: those companies are providing those privacy protections specifically in reaction to governments like the UK and US that violated their own laws (then kindly forgave themselves) in order to surveil their citizens. If Apple and Google, etc, are adding security, it’s because of people like Theresa May, not because of ISIS. And it’s bullshit, anyway: the companies listed have all provided backdoors into their communications (voluntarily or by ‘accident’) since at least 2005 – if being able to read Apple users’ communications was going to help defeat terrorism, that defeat rather conspicuously failed to materialize. Apple and Google and so forth are trying to give their customers what they want and the UK and US government are saying, “no, you can’t have that.”
After all, it works for China. The idea of a “great firewall” around an entire nation seems absurd but the Chinese are treating it as a technical problem and have put it in place as a technique for political control in advance of a time when it’s needed. In the US we call it “the internet kill switch” or a patchwork of other ways that the police state is able to shut down citizen communications during an emergency. The Chinese government learned a very important lesson after Tienanmen Square, right before the internet and smart phones became a big thing, and they “embraced the internet” in a way and to a degree which I suspect the US and UK governments envy.
The problem is not as May says it is, that ISIS is able to communicate secretly over the internet – the problem is that the intelligence apparatus of the US and UK have no strategic response to organic insurgency tactics. They don’t actually need one, because attacks like ISIS is pulling off are not a significant threat to anyone, but it’s a public relations disaster to the control freaks in government since it shows how helpless they are to actually control those things that they purport to want to control.
Her government called for such a backdoor after it emerged the killer in March’s terror attack near the Houses of Parliament used WhatsApp just minutes before stabbing a police officer to death.
And suppose GCHQ and NSA had perfect intelligence into the killer’s data stream: what would they have done differently, “just minutes before” an attack? Secondly, if they did react immediately based on monitoring data streams, they’d be predictable and easy to maneuver for an attacker. If I were a terrorist and I knew I was being monitored, I might mousetrap a bunch of response units into a kill-zone claiming there was going to be a knife attack and instead there were a bunch of IEDs and some propane tanks overwatched by 2 snipers.
I’m bothered by the overall stupidity of the surveillance state’s response: when your ubiquitous monitoring has been shown not to help you protect against attacks, the answer is not “more ubiquitous monitoring.” I am also bothered by the dishonesty of the surveillance state’s response: I don’t think for a second that they’re not aware of the problem, they just want to increase control because it may come in handy to protect the establishment if the people finally catch on to how badly they’re being screwed and decide to rebel.
CNN continues to propagate the lie:
The United States has called for similar backdoors. Former FBI director James Comey lobbied Congress last year to pass a law that would require internet companies to let U.S. law enforcement spy on encrypted communications. Comey’s proposal gained traction after the FBI had difficulty getting into the iPhone used by the shooter in an attack in California.
First off, Comey’s proposal didn’t “gain traction” – it got news coverage from the fawning press, but the FBI already has the access they were complaining that they need. Do they think they’re going to lure insurgents into a false sense of security or something? It’s always dangerous to assume your opponent is as stupid as you are.
Breaking News: We are now told that the police have identified the attackers, and have arrested a dozen people from residences believed to be the homes of the attackers. [bbc] Of course the retro-scope will be useful for determining if any of them were involved or aided the attack but there is no possible increased amount of surveillance that would have prevented the attack in the first place. I am also more than a bit concerned regarding the wisdom of swooping down and arresting everyone an attacker lived with or interacted with – it starts to look a lot like collective punishment, doesn’t it? What’s next? Israeli-style “we bulldoze your family’s house” retaliation against the relatives of dead suicide attackers, because they’ve placed themselves beyond the reach of the state? I do not think that any of these tactics are going to be effective, and may be worse than ineffective.

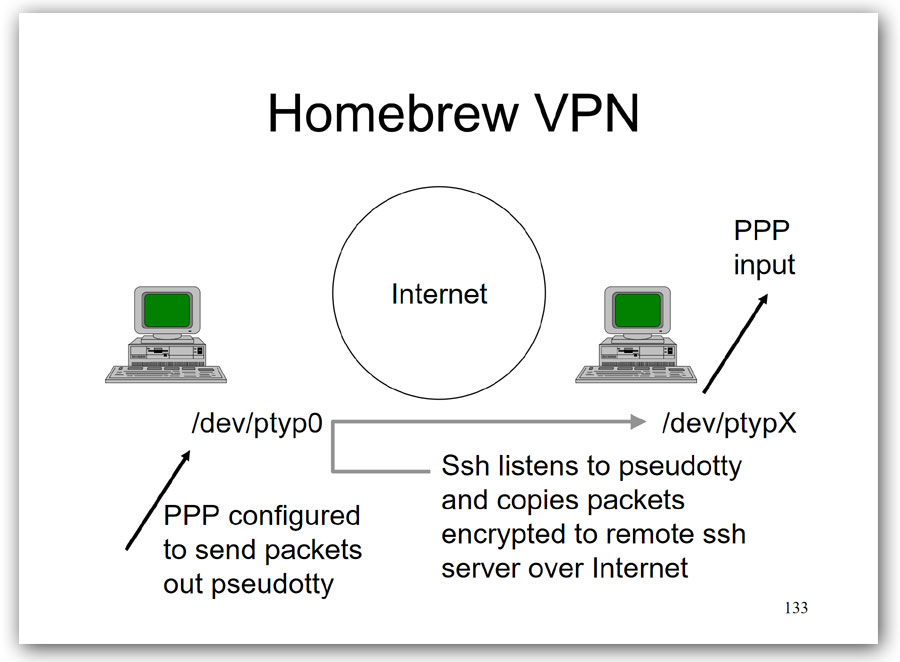
 Back in the late 90s I taught a class for USENIX on “secure communications over open networks.” (PDF of slides) since it was becoming obvious this was going to happen. I sort of hoped that the people who were going to push ubiquitous surveillance would realize how easy it is to defeat, and refrain, but I hadn’t taken into account how easy and attractive it is to spend lots of other people’s money. In my class I included simple techniques for establishing VPNs using basic tools and bulk encryption engines, how to plot a conspiracy using in-game chat in online games, and any of a variety of other techniques. Some of them are less viable now, because you’ve still got to worry about falling into the retro-scope, but if you’re a suicide attacker, you’re immune to retaliation and you’re pretty much impossible to block unless you’re stupid and plan your attack on a 6-month time-frame.
Back in the late 90s I taught a class for USENIX on “secure communications over open networks.” (PDF of slides) since it was becoming obvious this was going to happen. I sort of hoped that the people who were going to push ubiquitous surveillance would realize how easy it is to defeat, and refrain, but I hadn’t taken into account how easy and attractive it is to spend lots of other people’s money. In my class I included simple techniques for establishing VPNs using basic tools and bulk encryption engines, how to plot a conspiracy using in-game chat in online games, and any of a variety of other techniques. Some of them are less viable now, because you’ve still got to worry about falling into the retro-scope, but if you’re a suicide attacker, you’re immune to retaliation and you’re pretty much impossible to block unless you’re stupid and plan your attack on a 6-month time-frame.
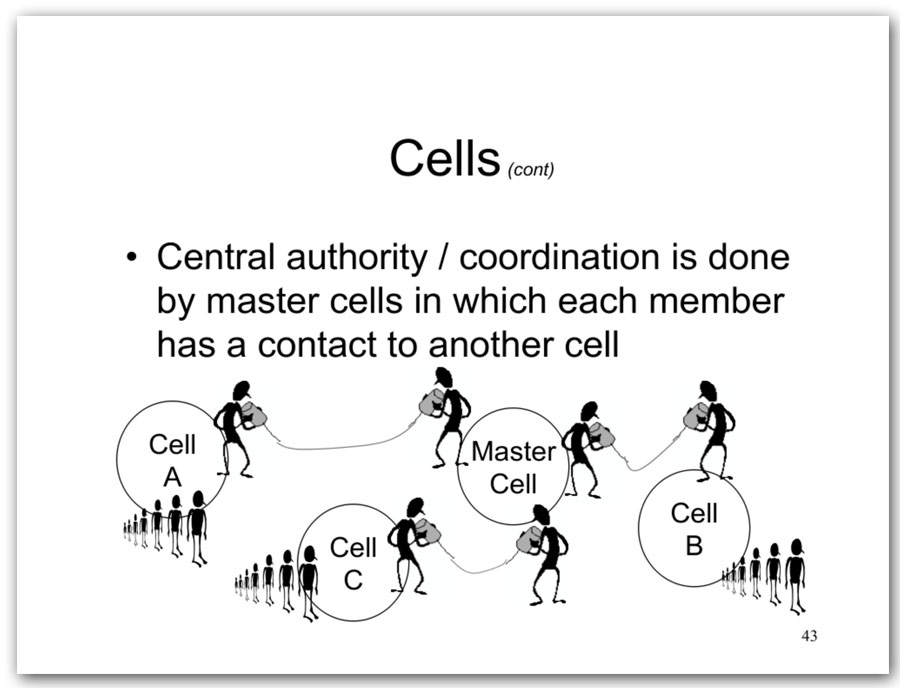
The “cell structure” slide is an example of one that no longer works – and it’s why ISIS doesn’t structure like a 1970s espionage agency; they’re using 4th generation cyberinsurgency tactics.
I am going to reiterate something I’ve mentioned before here, and elsewhere: the best way to respond to government’s intrusion into citizen privacy is to retaliate in kind. If you write software that will be used by government agencies, backdoor it. If you build systems for government, backdoor them. If you handle secret material, disclose it. If you are building the Great Firewall Of America, build the Great Backdoor. The justification for doing so is exactly the same as the justification they’re using, so if they believe it, they ought to accept it going the other way – they won’t accept that justification, of course, because they never meant a single word of it.

Yeah, when you’re looking for needles in a haystack, making the haystack bigger is not a solution.
As always, we learn after the fact that the attackers were “known to the security services”, and a bunch of people wonder aloud “if they were known to the security services, why didn’t you do anything about them?” To which the answer is: huge numbers of people are “known to the security services”, we haven’t the foggiest idea which ones actually pose a threat and which ones don’t, and we can’t “do something” about all of them without building concentration camps.
It’s a fundamental screening problem: how do you screen for a rare condition in a large population when your tests have low specificity, and false positives are expensive? Answer: you don’t. It’s statistically impossible.
Still, you can tell they’re taking it seriously, because they’ve rounded up twice the usual number of suspects…
Dunc@#1:
Yeah, when you’re looking for needles in a haystack, making the haystack bigger is not a solution.
But we know how to build big haystacks! The biggest! YUGE!
Apparently some of the attackers were pretty open about being jihadis. The only triggering event they had to conceal was that they specifically planned to “go operational” and do something. An attack like theirs took probably 10 minutes to plan, so there would have been no window for the police to act even if the attackers had posted their plan on facebook.
Theresa May’s tough talk about expanding the powers of the police and doing everything possible to help them out would be less pathetic if she hadn’t been responsible for sacking over fifty thousand police officers in her time as Home Secretary, thanks to her government’s swingeing public service cuts. The British police despise her as much as the medical profession hates Jeremy Hunt (sic) and the teaching profession hates Michael Fucking Gove.
cartomancer@#3:
if she hadn’t been responsible for sacking over fifty thousand police officers
That’s part of the premise of the surveillance state: instead of having beat police wandering around helping people, you have a small operations center staffed by voyeurs who watch flat panels. It’s leverage! Or something. Of course, it really equates to cutting jobs and moving public money into the security tech/military/industrial sector. If the NSA has accomplished anything in the US, it’s good at that, at least.
So if you want to be a terrorist the first thing you do is get a pitchfork and start making the haystack bigger? No wait, the security services are already doing it for you.