Between Wikileaks, the Shadow Brokers, the FBI’s use of confidential informants like Sabu [stderr] we learn the breadth and depth of the US Government’s hypocrisy about “cyberwar” and espionage.
There are two stories: One, the US has unfailingly violated its own laws in order to spy on its own citizens [stderr] and two, the US has relentlessly spied internationally; politically, economically, and militarily. The entire time, the US has kept up a barrage of complaints, whines, grumbles, and threats of retaliation regarding foreign action of exactly the sort that the US has been engaging in. The overall message that the world should be getting from these various disclosures is that when the US government complains that EastAsia is spying on us to steal our secrets, that the US government is spying on EastAsia to steal their secrets. It’s projection, pure and simple. When you hear the US government complain that Russia is interfering with elections, you should assume they are muttering, sotto voce, “… because that’s what we’d do.” Because that is what they do.

[source]
The US intelligence community (and law enforcement) have tools that allow them to generate traffic from anyplace; there are injection points around the world – if some agency wants to post to a jihadi site using an account from Somalia, it’s easy – those tools will even manage browser language settings and typical typographical errors that a Somali might make writing Arabic. Those (and less sophisticated versions) are what the FBI uses to troll young people into expressing support for jihad, so that they can arrest them. Those are the tools that the FBI uses to infiltrate Occupy organizers and Black Lives Matter organizers’ planning circles.
What we learn from the disclosures, again, isn’t that the tools or methods are interesting – it’s that the authoritarians in the intelligence and law enforcement community have never cared about following the rules; they’ll do anything to you that they want (if they can) and they’ll scream bloody murder if someone else does exactly the same thing to them. Remember when the NSA was caught tapping Angela Merkel’s cell phone? There was a brief kerfuffle then President Obama blew it off as “that’s how things are done.” Remember when Russian hackers broke into American political parties’ email systems and dumped private emails that demonstrated their corruption and stupidity? The only difference is that the NSA didn’t publish Merkel’s phone calls. Maybe they weren’t interesting enough. Otherwise, it’s the same game, but the rules are asymmetrical.
Description: The Marble Framework is designed to allow for flexible and easy-to-use obfuscation when developing tools. When signaturing tools, string obfuscation algorithms (especially those that are unique) are often used to link malware to a specific developer or development shop. This framework is intended to help us (AED) to improve upon our current process for string/data obfuscation in our tools. The framework utilizes pre and post-build execution steps to apply obfuscation to the tool. [CIA Marble Framework docs]
Remember how the FBI tried to attribute attacks based on language settings parameters in malware? That’s what the CIA’s tool “Marble Framework” does. It’s designed to munge through code and translate variables, language parameters, and structures, to make the origin of a piece of object code look different.
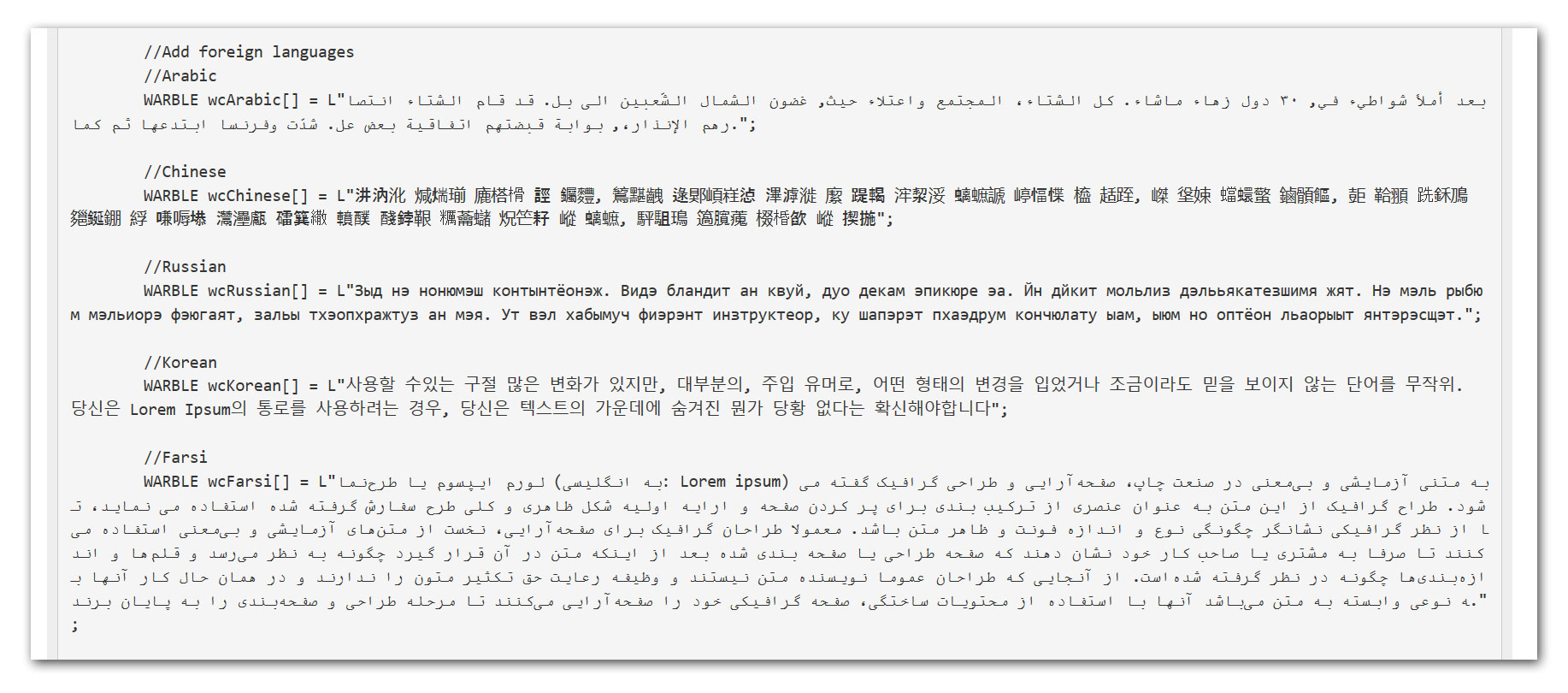
example of how to use Warble/Marble [cia]
Spying tools and operational protocols detailed in the recent Vault 7 leak have been used in cyberattacks against at least 40 targets in 16 different countries by a group Symantec calls Longhorn. Symantec has been protecting its customers from Longhorn’s tools for the past three years and has continued to track the group in order to learn more about its tools, tactics, and procedures.
The tools used by Longhorn closely follow development timelines and technical specifications laid out in documents disclosed by WikiLeaks. [symantec]
While the NSA was running rampant hacking the world, and the FBI was running rampant hacking the world, guess what? The CIA was running rampant, hacking the world. And were the targets intelligence agencies? Of course not:
Longhorn has infiltrated governments and internationally operating organizations, in addition to targets in the financial, telecoms, energy, aerospace, information technology, education, and natural resources sectors. All of the organizations targeted would be of interest to a nation-state attacker.
Longhorn has infected 40 targets in at least 16 countries across the Middle East, Europe, Asia, and Africa.
Remember Longhorn when the US Government complains that the sneaky ${whoever} are trying to steal economic and trade secrets. When the US government complains that North Korea has an army of “9,000 hackers” and the Chinese have a huge “hacker army” just remember that the US has the same, in triplicate, and probably much larger because they’re using contractors and outsourcing the work to entire companies that make them tools off the books.
Xetron Corporation, whose products range from military sensors to communications systems to information security software, shows up in nearly 400 documents published earlier this month by WikiLeaks. Those documents describe some of the tools the CIA uses to hack phones, smart TVs, and other digital products to conduct espionage overseas — and some of the partners that help them do it, like Xetron. [intercept]
I used to joke that Windows was so unreliable because the NSA backdoors were probably conflicting with the Mossad backdoors. Ha, ha, ha, ha. Now we know there are at least a dozen backdoors in your system – ranging from in the firmware of your hard drive, to the firmware in your smart monitor, to the router your ISP gave you, and the various deliberately placed flaws in the encryption software you use to “protect” your transactions. Ha, ha, ha, ha. The US has hacked the world, but still its government can’t build a website that hackers can’t walk into. So, when the Chinese (or whoever, maybe it was the CIA) hacked the Office of Personnel Management’s computer systems and copied the entire employee database for the last decade or so of federal employees (including family and security clearance data) all the US could do is point the finger of screeching blame at China.
In US politics, we are dealing with the dawning realization that the President is a pathological liar. By “pathological liar” I mean: he can’t tell the truth, even when telling the truth is probably easier and more effective. I hear various journalists call this the “post truth world” and things like that. Finally, it has dawned on them that politicians lie. I want you to internalize that realization about the government in general, but specifically its intelligence arms and law enforcement arms. They can’t tell the truth because they don’t even know what the truth is. To know what the truth is, you have to care what the truth is, and they don’t.

Binney is problematic for me. While I appreciate disclosure of the government’s crimes against itself, Binney’s complaint was that a particular program was not successful and was corrupt. That program superceded a system Binney had developed that he felt did the same thing. In other words, Binney wasn’t a whistleblower about the government’s crimes against the people – he was whistleblowing that the system they put in place wasn’t as good as the one he wanted to put in place. With friends like him, I don’t need enemies.
“… still its government can’t build a website that hackers can’t walk into” — defense is much harder than offense. I pointed that out decades ago (my best attempt is here)
Public reporting is that Xetron did $94million in business with the government last year. That’s probably a multiple of the North Korean government’s entire cyberespionage program budget.
“I used to joke that Windows was so unreliable because the NSA backdoors were probably conflicting with the Mossad backdoors” – want to see a senior executive from an antivirus company look awkward? Ask them why they didn’t detect any of this stuff. They didn’t detect any of it. Why? Option 1: They were told not to. Option 2: They suck. I asked someone I knew at MacAfee why my A/V scanner didn’t detect the Sony DRM rootkit, and the answer was: “Sony asked us not to.” [ranum 2007] The computer security industry exists to get your money; it doesn’t exist to secure your systems (if it does, that’s largely an accident).

Pompeo is on the warpath: https://theintercept.com/2017/04/14/trumps-cia-director-pompeo-targeting-wikileaks-explicitly-threatens-speech-and-press-freedoms/
polishsalami@#1:
Yeah, I saw that – it’s some truly epic Orwellian projection, isn’t it?
Besides, Wikileaks helped them get their cheeto puppet elected. He’s biting the hand that feeds him.
I figured that I’d catch you being just as dishonest about the hacking stuff as you have been about military technology if I looked into it at all.
The “language settings parameters” that were used to blame the attacks on the Russians was in fact the locale ID setting. It’s a setting in the build environment. Now go take good look at that marble document you linked to. Do you find a single reference to locale ID? The screen grab you linked certainly has nothing to do with it at all. It looks like it’s code that tells the obfuscation tools to apply a technique that’s compatible with the foreign language character sets used in the specific languages. You’ll notice that the offered examples don’t include a single language that can be written with Latin characters? I’m guessing their standard text string obfuscation techniques don’t work on other character sets, so they can invoke special routines that work with that method of text encoding.
This is what you do, isn’t it? You post things that kinda sorta relate to stories in the news, but you alter the details along the way. You change them to make them mean what you want them to mean, rather then what they actually say. You trust that your readers will hear “language settings”, see a foreign language in a screen grab, and figure that that must be close enough. You’re the expert in programming, so you trust they’ll accept your word on it if you include a lot of technical sounding words.
To be honest, I wouldn’t have even noticed if you’d kept your bullshit on the side of programming. It’s when you started throwing around the fear uncertainty and doubt about military weapons programs on which I was at least passingly familiar that I started to sense something was amiss. When I see a programmer criticizing a weapons program that has had its share of problems, but instead using bizarre criticisms he pulled out of his own asshole, it gets my skeptical antenna twitching.
If you were that sloppy there, I didn’t figure you’d try too hard on the computer side either. I may be only a neophyte programmer, but I know the difference between the build environment and strings in the code.
I think you’ve missed the point, Nomad. If you read the rest of the post, you’ll see that what Marcus is saying (I think), is this:
The FBI attributed some stuff to the Russians based on the fact that certain documents (appeared to have) been edited on a computer with a Russian locale setting.
Marble is designed to, among other things i guess, create *exactly that illusion*. So, assuming Marble works right, the FBI could just as easily have been looking at an NSA or CIA product as a Russian product (or, frankly, a product from ME, because I know how to make my computer take a temporary trip to “Russia” just fine, thank you, but I don’t have tools for doing it automatically).
I admit that Marcus wasn’t super clear, assuming that I am even reading him correctly. But whatev, it’s a blog, not a PhD dissertation.
@Nomad #3: Setting a locale is actually pretty trivial. It’s just a shell variable. If you’re rebuilding code anyway then setting a shell variable before you do it is not difficult.
@Marcus Ranum #2:
Didn’t Machiavelli think that was a pretty effective strategy? Get what you need out of someone that’s going to be in your way later. Then get rid of them before you have to repay them.
Which reminds me, I need to get around to actually reading The Prince.
Marcus, you’ve hit blogging big time. You’ve got your own flea!
Nomad:
Yet your further comment does not indicate that.
Um. What it looks like to me is a polymorphic version of the old BASIC DATA statement.
What it indicates is that the developed instance might require any of the specific strings.
<snicker>
Conditional declarations are still in your future, then.
Brian @7, :)
I’m a professional programmer by trade, and I’d like to know what I’m talking about.
One observation / comment:
I’m not sure exactly what sort of “string obfuscation techniques” are referenced, and I don’t feel like re-reading any of this. However, if you’re referring to automation that adds common typos to strings which are common typos by native speakers, then the code, assuming it’s well written, works on only Unicode strings (hopefully UTF-8, but I’ll settle for UTF-16), and there’s another component that takes the Unicode string and re-encodes it in the target encoding. Any proper piece of code that works on multiple languages should be written to use Unicode for all internal processing, and the program should have encoding translation as necessary on the input and output.
If it’s badly written, then it uses UCS-2 for internal processing.
If it’s super badly written, then there’s a separate piece of code for every language, and each component uses a different encoding. Possibly dozens of different ASCII extensions. ~shudders~
PS:
A plug so that programmers everywhere will write better code:
http://utf8everywhere.org/
[OT + meta]
Damn orotundity;
→
Isn’t the present indicative better than the subjunctive for what you want to express?
To John Morales
“I’d like to think” aka “I would like to think” is more humble. I did not outright say “I know what I’m talking about”. Instead, I stated that I have a desire, or a wish, that I’m competent enough that I know what I’m talking about. I may be one of the most competent programmers at my workplace, but I also recognize that I have much to learn, and I make mistakes regularly.
At least, that was my intention.
EL, heh.
It may have been your intention, but you certainly proposed a conditional state, implying that it’s not an extant state. I.e.: you do not believe you know whereof you speak, but you would like to do so.
(Surely that you would like to think something is not the same as you thinking that something… indeed, were you to think that something then the conditional would be otiose fore the present)
To John
That is correct literal interpretation of the grammar. However, this grammatical construct has a non-literal meaning. It’s a somewhat common idiom. It’s a “polite form”. See:
http://www.macmillandictionary.com/us/dictionary/american/i-d-like-to-think-that
http://www.ldoceonline.com/dictionary/i-d-like-to-think-believe-that
So I respond back: Meh.
(lol)
@nomad:
I’m on the road today and most of sunday. Sorry to hear you have concluded I’m a liar; that concerns and confuses me. I’ll address your comment when I get home.
Andrew Molitor@#4:
Yes, That’s what I mean. Elsewhere I’ve pointed out that the FBI’s attribution of attacks is really shoddy (taking things like language and keyboard settings as an indicator of national identity) I mentioned Marble because it’s an indicator that the CIA is quite aware of those sorts of indicators and has automated tools to spoof them – if the CIA is spoofing indicators then everyone should assume that anyone else who wants to spoof those indicators can (and is!) too. It’s actually worse than that – as I tried to obliquely mention – there are as-yet undisclosed tools that are deliberately designed to misattribute traffic. The one I know of is not CIA, it’s corporate, but the CIA is their biggest customer. That sort of tradecraft for falsification goes back a long way, to Digex (which was an ISP created to provide a home for a lot of osint activity) and AOL (which was the FBI’s ISP of choice for a long time). That there is a market (12+mm$/yr) for misattribution tools and services should not surprise anyone.
One of the problems with blogging is trying to remember what topics you’ve introduced where, and deciding if you can assume someone reading a current post or comment is caught up on a decade of commenting and a year of posts. The alternative being to forkload references into postings, which would crater my posting-rate since I’d basically be building a topic index as I went.
Oooh that’d be a coolass wordpress plugin: something that builds a topic index and map…
The translated strings example is a code fragment from the CIA’s documentation on how to use the Marble tool. The example is the “lorem ipsum” thing in several languages. Basically it appears to be a string-table pre-processor for C source code. Instead of building a separated string table in your code (which would indicate that you were internationalizing on purpose) you make it look like you’re a lazy North Korean programmer who just hardcoded strings so the FBI could identify you.
This might also be worth looking at:
https://go.authentic8.com/toolbox
It’s hardly the best tool of its sort that’s out there; the good stuff is “for official use only”
No, Englightened Liberal, that’s not at all what the linked program does. “String obfuscation” in this context means hiding it so that no words or anything that else that’s supposed to be hidden are readable in the binary file. It’s clear that you never bothered to read this link. This had absolutely nothing to do with faking Russian language use in the software, it was about hiding any and everything in it so that they can’t be easily read. If you’d clicked the link you’d have seen this:
“The post-build step will also double check to make sure none of the obfuscated data appears in the binary.”
It’s designed to hide it. Not insert tricksy little bits of grammer errors, but make it entirely unreadable. The reason for this would be obvious if you loosened the tinfoil hat enough to let some oxygen get to your brain. Despite Marcus’ desperate desire to make it seem like this is about the NSA or CIA trying to make their code look like it was written by a Russian, it’s about something much more basic then that. Hiding what the code is supposed to do. So any time a programmer makes a variable that makes sense, this code goes in there and messes it up so it’s an unintelligable bit of gibberish so that when the target eventually finds it and starts trying to reverse engineer it, it’s hard to figure out what does what. Make the program as cryptic as possible and it’ll take longer to figure out what it was after and more importantly, what it might have gotten.
Now let me help you out here because I fear I’ll just get some sort of response like “well yes, that’s an X-K Red 27 technique, they have to hide the Russian language use so it looks authentic, if it was out in the open it would be too obvious”. Think a little simpler then that. Marble was not about spoofing, there’s not a single thing in there that suggests it is despite Marcus doubling down on insisting that it is. It was about developing different ways to obfuscate the code that are harder to track down. It wasn’t about mimicking other people’s techniques, there’s not a single thing in there that indicates that, it was about using more varied techniques so that your code is harder to fingerprint. In other words, anonymity instead of mimicry.
So why the ability to process Cyrillic or Farsi? Just think a little bit here. Let’s say you’re making a program you want to slip into a computer at the FSB that’s looking for, say, a directory of secret Putin shirtless horseback photos. Do you think you do that by having the program look for “C:\secret Putin horseback riding cache\”? Of course not, you’d need to look for the equivalent in Cyrillic. If you’re looking to break into North Korean computers, you’re going to need a program that can look for things in Korean.
So the obfuscation tools will have to be able to garble up Cyrillic or Korean so that once the program is found, it’s not bleedingly obvious what it’s doing.
Marcus, the quotation I offered up there applies to what you said as well. This was not about sticking random strings of text into the program, it’s about being able to garble up strings of text if you need to use them so that they’re not readable to people who find the program and are trying to deconstruct it. It’s doing the exact opposite of what you claimed. Yes, I understand that the text was the equivalent of lorem ipsem, it’s just a demonstration of how you use it. But just reread that part about how Marble makes sure that none of the obfuscated data appears in the binary. It’s not an automated means of inserting text into code. It’s an automated means of making sure that the text doesn’t appear in it.
But really, why would someone insert lines of foreign language text into a program for no reason? That would stand out as an enormous red flag, basically saying “we really, really want you to think that this program was made by Russians, to the point that we stuck paragraphs of pointless Russian text into the code just to be sure you caught the hint”. This also looks like intentional dishonesty on your part. You appear to be trying to refer to the way that the emails used in the attacks and the released documents were scrutinized and conflating that with the programs used to carry out the attack. Marble is not a tool about fudging text files, that’s an even bigger stretch then claiming that it’s designed to slip random Russian words into an binary file.
And no, Marcus, when you’ve just tried to dishonestly pass off a tool designed to ensure the anonymity of the user as a language spoofing tool, you don’t get to go on and make vague references to mystery evidence not yet presented. I have no confidence in any further secret evidence when the offered evidence flatly contradicts you. You’ve provided a tool designed to strip clear language out of hacking tools and claimed that it was used to insert it. Your own citations contradict you, and your response is to insist that you’re really right after all because we just *know* that they do this stuff.
I should hope so, because I explicitly advertised this in my previous post.
Nomad:
Ahem. What Marcus actually wrote:
—
Heh.
(TLAs using sneaky code? Well, I never!)
I dunno, nomad. The documents seem to align with what Marcus says when I read them.
Am I misremembering, or did digex pitch itself as a bastion AGAINST government interference? I remember some guy from SOME local ISP around there saying they’d considered thermite bombs on the servers for when the FBI kicked the door in.
Which, in hindsight, I should have taken as a “Ah, methinks they protest too much. Probably a wholly owned sub of spookdom.” but I didn’t. I was young!
Andrew Molitor@#23:
Am I misremembering, or did digex pitch itself as a bastion AGAINST government interference? I remember some guy from SOME local ISP around there saying they’d considered thermite bombs on the servers for when the FBI kicked the door in.
Having the FBI kick the door in on a CIA-owned ISP – you bet that’d be a big problem. Especially, because, back then, the CIA was still pretending to be following the law.
I’d rate that as “possible, maybe even probable, but unproven” – it could be that I’m completely wrong about it.
It’s more complicated now, since CIA has In Q Tel out there creating businesses for them. Some of those are probably red herrings. But it’s better to have the CIA playing venture capitalist than to have them raising black money some other way.
Nomad@#3:
I figured that I’d catch you being just as dishonest about the hacking stuff as you have been about military technology if I looked into it at all.
I don’t appreciate your accusations of dishonesty, particularly regarding my professional field. I’ve worked hard for the 25+ years I’ve worked in infosecurity, to be accurate and honest – even when it has been to my financial and professional disadvantage. If you’re going to accuse me of dishonesty, I’ll take you seriously, but I’m going to insist on a very high quality of argument coming from you. One of the things I’ll note is that I’m careful to reference secondary sources: I believe that mostly I am trading in facts. You may disagree with my interpretation of those facts, but that’s how life is – one doesn’t get to throw around serious charges of dishonesty based on different interpretation of facts; at best we can say “you don’t understand” which is a lot different from calling someone a liar.
The “language settings parameters” that were used to blame the attacks on the Russians was in fact the locale ID setting. It’s a setting in the build environment. Now go take good look at that marble document you linked to. Do you find a single reference to locale ID? The screen grab you linked certainly has nothing to do with it at all. It looks like it’s code that tells the obfuscation tools to apply a technique that’s compatible with the foreign language character sets used in the specific languages. You’ll notice that the offered examples don’t include a single language that can be written with Latin characters? I’m guessing their standard text string obfuscation techniques don’t work on other character sets, so they can invoke special routines that work with that method of text encoding.
Perhaps I needed to include more remedial text in my explanation; I thought it was clear enough, but let me try to explain more.
The reason I mentioned Marble and the locale ID together is not because they are the same thing; I mentioned them because they are techniques for (on one hand) attempting to attribute an attack and (on the other hand) attempting to defeat attribution. It’s relevant because if the FBI is attributing attacks based on locale, and the CIA is using much more elaborate misattribution techniques in their tradecraft, then we ought to be able to assume that the FBI’s attribution is not very good.
I’ve done a couple pieces elsewhere about the difficulty of attribution [tenable, part 2] I don’t expect you to have read them, but if you’re interested in attribution in computer security, you may want to understand more of the background. Especially if you’re going to go around throwing accusations of dishonesty.
Anyhow, the point is:
– FBI has been known to attribute attacks based on one thing
– CIA (as a typical “nation state” actor) has been shown to have tradecraft that defeats that attribution
– Yes, they involve different details, but the details of the one (locale) are part of overall tradecraft that any competent practitioner that was setting up misattribution would take care of
Yes, they’re different things. The other people reading my posting appear to have understood my argument well enough. Maybe I should have made it more explicit. One of the problems I have is that I’ve been talking and writing about this stuff for the last 20 years and I forget what I’ve said and where, and sometimes I assume I’m talking to experts when I’m not. I’m usually pretty careful about that and I believe I am pretty respectful of my readers’ knowledge-level. So, again, I don’t appreciate being accused of dishonesty – at most you might fairly accuse me of not dumbing things down enough for you, which charge I will cop to.
This is what you do, isn’t it? You post things that kinda sorta relate to stories in the news, but you alter the details along the way. You change them to make them mean what you want them to mean, rather then what they actually say. You trust that your readers will hear “language settings”, see a foreign language in a screen grab, and figure that that must be close enough. You’re the expert in programming, so you trust they’ll accept your word on it if you include a lot of technical sounding words.
No, what I try to do is present information and analysis as I see it, in a way that is hopefully interesting and informative. You are accusing me of attempting to mislead my readership by omission and deliberate misdirection: that would not work. For one thing, I know for a fact that among my readership is at least one master C programmer, and another guy who used to work for a government research lab, doing exactly the kind of stuff I’m talking about here. For me to try to fool you, I’d also have to fool them and they’d be a much tougher nut to crack than you. Besides, many of the readers of this blog are pretty technical and I expect that most of them (those that cared, anyway) understood pretty quickly the oblique argument I was making regarding locale settings, tradecraft, and string obfuscation.
So, you’re either the brilliant conspiracy detector who caught my pattern of lies and obfuscation that fooled other security industry and programming professionals, or you’re the clueless conspiracy theorist who didn’t understand what I was saying and jumped to the conclusion that I’m lying. Do you want to know which one I think it is?
To be honest, I wouldn’t have even noticed if you’d kept your bullshit on the side of programming. It’s when you started throwing around the fear uncertainty and doubt about military weapons programs on which I was at least passingly familiar that I started to sense something was amiss. When I see a programmer criticizing a weapons program that has had its share of problems, but instead using bizarre criticisms he pulled out of his own asshole, it gets my skeptical antenna twitching.
Your skeptical antenna needs adjusting.
You’re assuming that your knowledge-level represents the highest level of programming expertise that reads this blog.
You’re assuming that your knowledge about weapons systems also represents the highest level of expertise that reads this blog.
You’re also assuming that nobody else who reads this blog would ever do any research or have any knowledge of their own, and that I’d be able to fool all 2,000-odd of them, except you and your amazing skeptical antenna. Maybe you’ve mistaken a dowsing rod for a skeptical antenna?
If you were that sloppy there, I didn’t figure you’d try too hard on the computer side either. I may be only a neophyte programmer, but I know the difference between the build environment and strings in the code.
You’ve mistaken your inability to do basic thinking for my attempting to deceive you.
@Nomad
PS – as I observed in response to your earlier accusations of dishonesty regarding the Osprey engine issue: [here
“What was really going on there was that I misspoke and I didn’t want to argue down into the weeds about it. ”
Admitting “I misspoke” and trying to explain my mistake, that’s just got to set your skeptical antenna screaming, doesn’t it?
Nomad@#19:
Despite Marcus’ desperate desire to make it seem like this is about the NSA or CIA trying to make their code look like it was written by a Russian, it’s about something much more basic then that. Hiding what the code is supposed to do. So any time a programmer makes a variable that makes sense, this code goes in there and messes it up so it’s an unintelligable bit of gibberish so that when the target eventually finds it and starts trying to reverse engineer it, it’s hard to figure out what does what. Make the program as cryptic as possible and it’ll take longer to figure out what it was after and more importantly, what it might have gotten.
You need to learn a bit more about programming, before you start throwing around wild accusations of dishonesty. More to the point, you might want to check around on the web for other programmers’ analysis of what the Marble tool does, and I suspect you’ll find (unless you manage to find a particularly bad programmer who fails to comprehend it) that it’s remarkably similar to my analysis of what Marble does.
Let me explain a bit.
Suppose I’m writing a piece of C malware that’s going to emit a string, e.g.: when ready:”
“Press
when it’s about to reflash your BIOS. A typical lazy way of doing that would be to write:
char flashprompt[] = “Press enter when ready:”;
That would allocate some memory in the software’s heap space and stick that literal string in there. When the program wants to emit that string, it would pass a pointer to it into a function that would (presumably) write it to an output/input (since this is a command process) stream. Now, if you took such a piece of software and ran “strings” on it, it’d immediately spit out that string. Then the FBI would go (because they are stupid) “LOOK! IT’s AMERICAN SOFTWARE!”
But if I were a moderately clever spy I’d go to Google translate and declare it as:
char flashprompt[] = “Press intra ubi est paratum”;
Then the FBI runs strings on it and goes “OMG WE’RE BEING ATTACKED BY ANCIENT ROMANS!”
But then the FBI posts that, and security experts like me go, “that is suspiciously stupid! Real ancient Roman hackers were pretty good! They wouldn’t just embed static strings in their code!” Besides, a piece of malware with a static string like that in it, is super easy to detect: you just look for the string.
Enter obfuscation. What we do is we use a tool (like hackers do) that obfuscates the string in the program memory. There are loads of ways of doing this. The problem is that, on any computer that behaves predictably, your code can be interpreted – with a sufficient level of difficulty – so the string gets munged into a variety of different memory addresses, with a routine to reassemble it when necessary, and a malware analyst sits there (Hi Joel, if you’re reading this!) and reconstructs what the code is doing, by interpreting the assembly instructions, to see how the string is constructed from where it’s obscured in memory. After 20-40 hours of hard work, the malware analyst reconstructs the string from where it’s hidden (this is always possible, because of how computers work) and wipes the sweat off her brow and says “It was encoded using some pretty cool obfuscation techniques that are fairly advanced. In fact, it’s an obfuscation technique called the ‘Caesar Shift’ that was popular with ancient Romans and it reads “Press intra ubi est paratum””
Then the FBI does a press release saying “IT WAS ANCIENT ROMANS! WE ARE SURE!”
See, the point is not that the tool will fool everyone – it’s that the tool makes it look like someone was trying to hide who they were, and doing a job that was good enough, but only just barely so, to fool the FBI.
It’s designed to hide it. Not insert tricksy little bits of grammer errors, but make it entirely unreadable. The reason for this would be obvious if you loosened the tinfoil hat enough to let some oxygen get to your brain.
You are not thinking things through enough. It’s ironic that you’re accusing EnlightenmentLiberal of being fooled by my evil plot, when you’re fooling yourself.
Marble was not about spoofing, there’s not a single thing in there that suggests it is despite Marcus doubling down on insisting that it is. It was about developing different ways to obfuscate the code that are harder to track down. It wasn’t about mimicking other people’s techniques, there’s not a single thing in there that indicates that, it was about using more varied techniques so that your code is harder to fingerprint. In other words, anonymity instead of mimicry.
Uh, no. It’s about spoofing tradecraft not spoofing code. It’s about making it look like malware was written by an Ancient Roman, who was trying to hide that using state of the art techniques, so that some malware analyst might conclude it was written by an Ancient Roman and not a CIA contractor.
That is “spoofing.” It’s spoofing tradecraft to interfere with attribution. You’re looking at the first level of the fake; i.e.: you’re falling for the part that the FBI would fall for.
But really, why would someone insert lines of foreign language text into a program for no reason?
Did you read the caption under the screengrab where I wrote “example of how to use Marble”??? Apparently not. The wikipedia page explains it adequately, too. That’s an example of how you might create strings in a piece of code and Marble will correctly obfuscate them in the binary. So you could put Farsi in the strings, run it through Marble, run ‘strings’ on the binary, and you won’t see Farsi: see? It works.
But really, why would someone insert lines of foreign language text into a program for no reason?
If you wanted to make a piece of malware look like it was written by an Ancient Roman, you might.
If you were a CIA malware writer who wanted to make it look like a Chinese was attacking a French online system, you might. You might not convince everyone that it was a Chinese doing it, but it would inject enough doubt that someone wouldn’t think it was the CIA.
This stuff is horribly relevant, when you see things like NSA’s hacking tools against SWIFT systems, going after Palestinian banks – you’d kind of want to be able to make sure that your malware looked like it was written by Ancient Romans, or something, right? [more on NSA swift tool]
Now before you go all obtuse on us and accuse me of lying for talking about NSA tools in the context of CIA tools, let me be clear: they’re not the same tools; they’re the same capability.
You’ve provided a tool designed to strip clear language out of hacking tools and claimed that it was used to insert it.
Don’t accuse me of lying because you’re not able to understand what I’m talking about. You can accuse me of being obscure; that’s fine. But just because you can’t understand me doesn’t mean I’m an evil genius.
(PS – I am deliberately trolling cartomancer and Brian English. Let’s see if they can resist the bait.)