Warning: this post is kind of long.
I like to avoid psychological terms, because I am skeptical regarding the epistemology of psychology* – but, to simplify the rest of this posting, I am going to freely use a term: “Sociopath”/Sociopathic.

Figure 1: sociopath
The term “hacker” has been used and abused in a variety of ways. We could probably decompile our various definitions of the word until it was unusable** and, in fact, there have been various attempts to do that: some people want to define “hackers” as curious technophiles who sometimes stray into places where they don’t belong, led by love of exploration – while others want to associate hacking with cybercrime and the societal costs of their activities. I used to fight that particular war, but it turns out that the word doesn’t matter because it’s being used as a sheltering label or demonizing label by two incompatible agendas: it’s not possible to agree on a definition because neither agenda will accept the other’s definition. So: some hackers are curious and harmless, others are criminal. This is a real problem because the media and the general public hear “hacker” and some of them take the favorable definition and others take the destructive one.
The reason I think that the dichotomy between white-hat hackers and black-hat hackers is bogus is because both roles involve adopting the mindset and methods of the worst role. In order to think like a “good guy” hacker you’ve got to think like the “bad guy” – now we’re down to arguing over the strange quibble I sometimes encounter in online games: “I’m not a bad person, I’m a good person who is role-playing a bad person!” To that, I usually respond that if the role you consistently play is that of a bad person, then you’re probably not role-playing, you’ve just found an excuse to do something that you would probably be doing, anyway, if you hadn’t been able to make up a handy excuse.
That’s why I think it’s going to be useful to be able to employ the term “sociopathic” – the stereotypical sociopath from movies are characters like Amon Goeth in “Schindler’s List” or Alex in “A Clockwork Orange” – they are characters that are so supremely selfish and lacking in empathy that they do things that strike the well-socialized viewer as lacking normal restraint, and a strange combination of predictable in their area of obsession, and unpredictable in other areas. For example, you can be pretty sure that Hannibal Lecter will do horrible things to you because that’s the focus of his peculiar obsession, but he may be so peculiarly obsessed about it that it’s almost funny; it makes sense – it’s practically forgivable. That’s why I feel that psychologists want to have a “disorder” called “sociopathy” or “antisocial personality disorder” they want to reflect, in a sense, that this person lacks a moral compass, that something is wrong with them, but because they are suffering from a disorder it’s not completely their choice.
There’s an important element to the stereotypical movie sociopath: they find a justification for their actions (usually as a response to a plot device) and their over-the-top reaction hinges on that justification – in fact, the drama of “Rambo” or “High Plains Drifter” revolves around this weird sort of: “you looked at me funny, so I burned your whole village to the ground” reflex. The difference between Hannibal Lecter is that he doesn’t really bother much with a self-justifying fig-leaf, but a movie sociopath like Alex in “A Clockwork Orange” will go to the trouble to cook up a reason to kick your teeth out so he can walk away feeling he’s done a good night’s work.
I want to avoid the whole stereotype (which I think is inaccurate) of the hacker-as-autism-spectrum non-neurotypical agent with reduced moral capacity, though it’s certainly hovering in the wings just offstage. The media loves to promote exactly that sort of obssessional behavior: the incredibly focused, brilliant, creative, socially awkward, genius. And there have been a few of them. The rest are more human and more ambiguous. The criminal hacker’s just in it for the money. They’re not hacking your machine to read your email, unless your paypal password is in there. They don’t care if they hurt you because getting your money is more important to them than your pain – they’re actually pretty morally clear: they don’t bother making excuses. The ones that are unusual are the ones that violate your privacy, invade you electronic home, throw electronic molotov cocktails at whatever they think will burn – and then try to convince you they were doing a you a favor. They’re sociopathic.
In an area where there is a deliberately-constructed gray zone of appropriate behavior, like hacking, you’re going to attract sociopaths.*** The media’s promotion of sociopathic hackers has forced a de-clarification of the line between appropriate behavior and unacceptable behavior, which allows the sociopaths to have it both ways: they violate privacy and convince you it was for your own good. Here is the problem: they’ve just showed you that they are willing to violate other people’s (and by extension, your) privacy and rights, but you accept their actions because they tried to convince you they’re on your side. They’re actually not on your “side” at all; they’re doing whatever it is they want to do, and they’re throwing up a sophisticated but utterly glib smoke-screen for why they are doing so.
I have some history with some of these guys. Before I start talking about that, let me emphasize a point I’ve tried to make implicit: I am not attempting to diagnose these people as having a “disorder” of some sort. I’m using the terms the psychiatrists use as an epistemological inventory indicating a “disorder” as a short-hand. When I call some of these hackers “sociopathic” I mean that they’re people I would never trust for a second because I have seen that they are glib, charismatic (sort of) (well, glib, anyway) moral nihilists who are quick at coming up with very plausible excuses for doing things that under circumstances except for with that excuse we’d consider their actions to be wrong, intrusive, suspicious, and mendacious.
Maybe you’re not a hacker, but you’re not a security security professional any more than a child molester is a day care expert.
The first of the hackers I ran across was Kevin Mitnick. He cost a few people I knew at Digital (while I was working there) their jobs, fulfilling his “curiousity” exploring the corporate network. There was no sign that he had any practical way of making money doing what he was doing – in fact, that was a lot of his defense of his actions. Never mind that when a hacker breaks into a system, the system’s administrator’s life goes south for a while, maybe they lose their job, and they certainly have their personal schedule violently re-arranged for a long time.**** Mitnick’s an interesting case: he simply cannot let go of hacking, it’s too central to his identity and his weak self-esteem. When he started off in hacking computers he got caught, was offered a job at Stanford Research***** (as a way of giving him a positive way to work with computers) but he immediately relapsed into hacking. He spent time in prison, on the run, and was hacking systems while the FBI was burning through taxpayers’ dollars trying to catch him, He got caught, was imprisoned again, and – wrote books about hacking, gave talks about hacking, waited till his probation was over and went back to hacking by putting a white hat on and selling his services as a “good guy.” It’s part of the old tradition of hiring safe-crackers to promote the security of your safes, but the wise safe-builder never turns his back on the former safe-cracker, especially if they have shown that they will go rogue again, and again, and again. How many times would Hannibal Lecter have to tell you he was cured before you’d have him over for dinner?
Mitnick’s “career” in computer security hasn’t been tremendously damaging, but it hasn’t been a success, either. There are few professional fields where you can list “was hunted by the FBI and was in and out of prison” as professional qualifications in your field. It doesn’t tell prospective clients you’re responsible, level-headed, and exercise good judgement. To me, that’s the key issue: I have no idea why anyone would hire a serial criminal, especially if they were trying to get you to pay them to continue doing the thing that wound them up in jail.

Adrian Lamo, the “homeless hacker”
Another of the sociopathic hacker elite I’ve had mild brushes with was the positively creepy Adrian Lamo. Lamo appeared fairly quickly on the hacking scene and became a star after hacking the New York Times. As often happens when the media is given an excuse to report about itself, he was briefly a media darling. Around that time, several conferences had the bright idea of giving the sociopath a microphone – William Hugh Murray, a serious old-school mainframe security expert, and I (and a few others) refused to be on panels with Lamo, because we felt that it was implying he was one of our peers; it’d be like inviting a serial arsonist to address a conference of fire-fighters. At that time, the news was full of fascinating stories about this odd-behaving young man who lived in ditches and abandoned houses, travelling the countryside and hacking large corporations using flawless technique. Except, like Mitnick****** his technique was pedestrian and not particularly creative. He appeared to be going after targets of opportunity: the New York Times hack was the result of discovering a misconfigured system that was trivially exploitable, then exploiting it. So imagine if you, armed with basic security knowledge, did target assessments against a dozen newspapers, the odds you’d make progress against one of them are fairly high (especially if you did as Mitnick often did, and glibly walked in the front door) Then when you publish your break-in, you don’t mention the other eleven you tried but didn’t get into. It sounds a bit like the Texas Sharpshooter Fallacy.
Lamo gave good interview, and he was “edgy” enough that he attracted a lot of attention from the media. It didn’t take very long for the security community to realize that he was just media-whoring, and to look into his background a bit. And it turned out that he was lying about lots of stuff – including the bits about sleeping in abandoned houses all the time, and so forth. Finally, he 911-called the police in for help, saying he was lost and delusional and was briefly institutionalized then diagnosed with Asperger’s. But here’s the thing: it would be a pretty good strategy to do that, if you were worried about being prosecuted for being an expensive pain in the ass. Now you can repudiate any or all of your lies and actions by saying variously “not my fault” or “don’t remember it” and so forth. Meanwhile, that gave people a chance to talk to his parents and it turned out that some of the times he was allegedly travelling around the country on hacking missions, he was comfortable at home. The whole wad of lies that was Adrian Lamo went into the dustbin after that.
I felt fortunate that I never took Lamo seriously at all; others were less lucky. Kevin Poulsen, who writes for WIRED, is also a former hacker elite who has (I’ll say that much for him) tried to reinvent himself doing something that’s not hacking and running online cons******* but I suspect Poulsen’s background and past sociopathic behavior may have made him particularly susceptible to Lamo’s stories. Lamo played Poulsen hard, before Lamo’s whole game finally crashed and burned. But there was still some life left in Lamo, another opportunity to show the world what a sociopathic manipulator he was: because of the press attention he had been getting, Lamo was the hacker Chelsea Manning contacted about how to release the trove of secrets.
It looks like a pretty simple, obvious transaction: Lamo knew he was on the FBI’s list of sociopaths to watch, so he gave them Manning in order to ingratiate himself with them. If you’re interested in the way Wikileaks got famous, and how Chelsea Manning got hung out to dry, you owe it to yourself to do a little bit of research on that particular time and those events. Glenn Greenwald (when he was writing at Salon) has a version of his view of what happened, a view which I largely agree with, but which is probably slanted by being justifiably disgusted by Lamo.[1] From my knowledge, there was also a security professional, Chet Uber, who got involved and directed Lamo’s interactions toward the FBI. Some of us do not talk to Chet, anymore, because of his shameful involvement in that situation.
Lamo flipped Manning to the feds, once Assange had the documents. Actually, Lamo was flipping Manning to the feds while the transfer was going on, it was a coin-toss how it all worked out, but no matter how it worked out, Manning was going to be roadkill and Lamo, Uber, and Assange simply didn’t give a shit for a second.
From Gawker[4]:
Here’s Lamo telling Manning their conversation would be protected because Lamo is “a journalist and a minister”:
(10:20:53 AM) bradass87: yes… questioned my gender for several years… sexual orientation was easy to figure out… but i started to come to terms with it during the first few months of my deployment
(10:21:09 AM) info@adrianlamo.com: May I ask the particulars?
(10:21:34 AM) info@adrianlamo.com: I’m bi myself, and my ex is MTF.
(10:21:34 AM) bradass87: im fairly open… but careful, so yes..
(10:22:00 AM) bradass87: im aware of your bi part
(10:22:24 AM) bradass87: uhm, trying to keep a low profile for now though, just a warning
(10:23:34 AM) info@adrianlamo.com: I’m a journalist and a minister. You can pick either, and treat this as a confession or an interview (never to be published) & enjoy a modicum of legal protection.
A journalist and a minister!? Lamo is trying to imply that he’s like the small number of journalists who have gone to prison briefly rather than reveal a source. And then he’s trying to imply he’s going to invoke the confidentiality of the confessional? Poor, naif Manning. If only Manning had a real friend to say, “talk to a lawyer immediately, and buy a plane ticket to Hong Kong.” Remember: Greenwald later took this lesson to heart when helping Edward Snowden – he did not trust the FBI or whistleblower protections because he’d already seen how Lamo/Uber/Assange threw Manning to the wolves after they had gotten what they wanted. They served manning as callously and coldly as Hannibal Lecter would serve one of his victims with beans and a glass of good chianti.

Julian Assange. Me spider, you fly.
Now we come to Assange. I don’t see Assange as more or less of a “piece of work” than these other characters; to me they’re all birds of a particularly nasty and dangerous sort, who flock together only when it’s convenient for them, and who’ll do or say anything without remorse, as long as it gets them what they want. One of the great tragedies of these affairs is that Julian Assange managed to successfully play one of the greatest sociopathic hacker scams of all times, to get himself positioned as a great human being, journalist, genius, etc. He’s definitely smart. But nobody who has had any interactions with the sociopathic hacker personality would turn their back on Assange for a second.
I first ran across Assange when he bizzarely popped up on the firewalls security mailing list, with an out-of-the-blue attack on a computer security researcher named Dan Farmer. Dan’s not a bad guy, he’s done some good work, some of which got blown out of proportion, but he’s definitely not the sociopathic hacker type. Suddenly, Assange pops up in a professional forum for serious security guys who are talking about firewalls, and dumps a weird homophobic “rap” about Dan Farmer – it seemed as though Assange decided to attack Farmer because he was an easy target in the community and some of the stuff Farmer had been doing was seen as edgy/questionable.******** Mostly, it was as though Assange realized, “Farmer is getting attention, and by attacking Farmer, I’ll get even more attention!”
It’s a long read but if you really want a sense for what Julian Assange is, I highly recommend [2] and [3] He’s the same sociopathic stew as the other hackers I’ve been talking about, the only difference – and I mean only difference – is that Manning unknowingly gave him a perfect vehicle for self-aggrandizement. If you read Rudder’s profile of Assange, you quickly discern the same pattern: lies constantly, doesn’t seem to realize what criminal behavior is or why, builds a consistent world-view that justifies his actions so he can do what he was going to do anyway, breaks relationships as if he doesn’t really understand what interpersonal relations are about, betrays anyone and everyone without batting an eye because it can be bent to be consistent with the self-justifying world-view.
Assange went by the handle “Mendax” for a while:
Mendax formed a closed group with two other hackers – Trax and Prime Suspect. They called themselves the International Subversives. According to Dreyfus, their politics were fiercely anti-establishment; their motive adventure and intellectual curiosity; their strict ethic not to profit by their hacking or to harm the computers they entered. Mendax wrote a program called Sycophant. It allowed the International Subversives to conduct “massive attacks on the US military”. The list of the computers they could recall finding their way into “read like a Who’s Who of the American military-industrial complex”. Eventually Mendax penetrated the computer system of the Canadian telecommunications corporation Nortel. It was here that his hacking was first discovered. The Australian Federal Police conducted a long investigation into the International Subversives, Operation Weather. Eventually Trax lost his nerve and began to talk. He told the police that the International Subversives had been hacking on a scale never achieved before. In October 1991 the Australian Federal Police raided Prime Suspect’s and Mendax’s homes. They found Assange in a state of near mental collapse. His young wife had recently left him, taking their son Daniel. Assange told Dreyfus that he had been dreaming incessantly of “police raids … of shadows in the pre-dawn darkness, of a gun-toting police squad bursting through his backdoor at 5 a.m.” When the police arrived, the incriminating disks, which he had been in the habit of hiding inside a beehive, were scattered by his computer. The evidence was removed. [2]
Rudder appears to buy what I suspect is a bunch of self-justification: that Assange and his hacker cats-paws were “fiercely anti-establishment.” My experience with the sociopathic hacker mindset is that they are “anti-control” – i.e.: if you rebel against everyone who is telling you “hey don’t kick puppies” then you are a brave hero if you figure out a way to kick puppies. I don’t buy that it’s real ideology for a second, because real ideologues usually do two things that the hackers don’t do very much of:
- They stand up to argue their ideology (even if it’s stupid and they do it badly. c.f.: Vox Day)
- They believe in their ideology enough that they don’t feel the need to be anonymous about it
I’ve debated this question with hackers before many times. My view is that if you’re really “curious” and “interested” about what’s on my network you can come here, sign my non-disclosure, and we’ll have a look together. Oh, you don’t want to do that? I guess you’re not “curious” about what’s on my network: what you actually want is the thrill of violating my security. Your “curiosity” is easy to satisfy, and is easily satisfiable but your voyeuristic desire to manipulate and control is not: the only way you can satisfy that is to be naughty, because what you really want is to be naughty, not satisfy curiosity. Put differently, if Assange were anti-establishment, he’d be using his skills and sociopathic charisma to align himself with various legitimate anti-government protest movements or political parties. But the problem with that is – if what you really want is control over others with no control over yourself, you have to step outside of politics entirely to do that.
I somewhat sympathize. Philosophically I would probably describe myself as a “moral nihilist” because I cannot come up with a convincing bridge across Hume’s chasm, and I found Kant’s arguments unconvincing after years of pondering them. But I’m saying it openly, right here, on a blog, and when I get caught doing something naughty, like speeding (guilty!) I don’t trot out moral nihilism as an excuse for arguing that the state has no authority over me. That’s just self-serving childish bullshit. Like you’d get from Mitnick, or Lamo, or Assange.
More from Rudder:
Assange descended into a personal hell. He was admitted briefly to hospital, suffering from what Suelette Dreyfus describes as “a deep depression and consuming rage”. He tried and failed to return home to live with his mother. He frequently slept along Merri Creek in Melbourne or in Sherbrooke Forest. He told Dreyfus that 1992 was “the worst year in his life”. The formal charges against Assange were not laid until July 1994. His case was not finally settled until December 1996. Although Assange had been speaking in secretive tones about the technical possibility of a massive prison sentence, in the end he received a $5000 good behaviour bond and a $2100 reparations fine. The experience of arrest and trial nonetheless scarred his soul and helped shape his politics. In his blog of 17 July 2006, Assange wrote:
If there is a book whose feeling captures me it is First Circle by Solzhenitsyn.
To feel that home is the comraderie [sic] of persecuted, and in fact, prosecuted, polymaths in a Stalinist labor camp! How close the parallels to my own adventures! … Such prosecution in youth is a defining peak experience. To know the state for what it really is! To see through that veneer the educated swear to disbelieve in but still slavishly follow with their hearts! … True belief only begins with a jackboot at the door. True belief forms when lead [sic] into the dock and referred to in the third person. True belief is when a distant voice booms “the prisoner shall now rise” and no one else in the room stands.
Self-aggrandizement, narcissistic bullshit, social failure, and a deep sense of entitlement, privilege revoked, and a desire for revenge. These are not the motives that make for a great journalist or paragon of political thought. This is a guy who is winding himself tighter and tighter and looking for a chance for when his more powerful enemies turn their back, to kick them really hard – and run. This isn’t a brave warrior, this is more like the hobbit, at the battle of Pelenor Fields, who nails the lord of the Nazgul behind the knee with a dagger. As Rudder points out, Solzhenitsyn spent a lot of time in a gulag after standing up for his beliefs: Assange was caught trying to hide his actions. One was a brave hero, the other a sociopathic hacker.
Assange was then cocked and locked, ready to go off at – whatever – however he could. He appears to have gravitated toward the cypherpunks back around the same time that I was hanging out there, during the early part of the Clipper Chip wars. I coined a term “rubber hose cryptanalysis” in a posting there, and Assange used that as the name for a secure communications program he wrote (with others) that never gained much traction because Phil Zimmerman’s PgP was the odds on favorite in the pre-text-messaging era. But Assange’s lack of self control and sociopathic inability to work with others, kept resulting in fallings out with his fellow travellers. Wikileaks bears some of the hallmarks of typical Assange fallings out – it’s unsure to what degree Assange controls it or doesn’t, but I’ve always assumed that it’s Assange and whichever of his hangers-on he hasn’t fallen out with yet; a rotating cast of fellow travellers some of which are ideologues and others of which are just waiting to be thrown under the bus when there’s a bit more traction needed.
I will say that Wikileaks was a brilliant and timely idea; but I wish it were done under the auspices of establishment journalism or even international governance. I’m not comfortable with Wikileaks being Julian Assange’s toy and the proof of that, I suppose, is in the pudding. It appears to me that Assange believed the false news report that Hillary Clinton wanted him killed with a drone-strike[5] and probably would be happy to have revenge because she’s the quintessential establishment stooge who something something paranoia something something. I don’t even care what the reasoning might be: it’ll be self-serving motivated reasoning – consistent, defensible, and sociopathic lies.
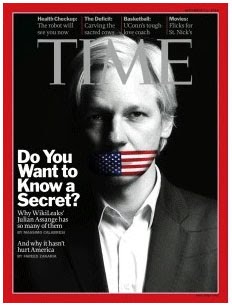 Where we collectively went wrong is when the shattered remains of the old media embraced Wikileaks and sanctified Assange (the same guy who helped ensure that Manning is now rotting in prison – how’s that for journalistic ethics?) The historical significance of all this is that it shows what a bunch of dupes the media are; in a sense Assange prefigured Trump. Apparently you can fool all of some people all of the time.
Where we collectively went wrong is when the shattered remains of the old media embraced Wikileaks and sanctified Assange (the same guy who helped ensure that Manning is now rotting in prison – how’s that for journalistic ethics?) The historical significance of all this is that it shows what a bunch of dupes the media are; in a sense Assange prefigured Trump. Apparently you can fool all of some people all of the time.
I’ll also note that for all the tragic abuse Chelsea Manning has suffered, the shocking “Collateral Murder” video did not have that big of a political impact. It promoted Julian Assange front and center, but it didn’t stop Obama from expanding his use of drone strikes, and it certainly didn’t do a whit to reduce American militarism in the middle east. Assange won the 2011 Walkley Award (the Australian equivalent of a Pulitzer prize) for advancing journalism but the foolish journalists didn’t realize that the project wasn’t about advancing journalism, it was about advancing Assange. Compare the way Glenn Greenwald and Laura Poitras worked the Edward Snowden case, if you want a better example of journalistic effort – and they didn’t even throw Snowden under the bus in the process.
I included Mitnick and Lamo in this discussion, in a posting which is mostly about Wikileaks and Assange. Because the kind of people I am describing here as “sociopathic hackers” are always all around us, and always have been. I don’t think that a power-hungry sociopathic money-making machine like Donald Trump is much different in his inner landscape from a Mitnick or an Assange. From my perspective I simply think of them all as dangerous people, because they’re like razor-sharp double-edged knives with razor blades on the handle: you cannot think you wield them. They are not your knife in your hand, you are the muscle and legs that they are using to cut whatever they think suits them to be cutting at that particular time. When I watch the ‘flexibility’ with which Donald Trump approaches facts, I don’t think there’s a difference in substance between him and a social engineer like Adrian Lamo – he tells you what’s convenient for him to tell you to get you to believe what he wants you to believe when it’s convenient for him at that time. The preceeding sentence was deliberately constructed to be confusing, because that’s what figuring out these peoples’ motives is like. They’re like the NPC bosses in a computer game: they’ll do things that are driven by a random number generator, stay out of their way and don’t expect anything from them other than complex randomness. When we think about a person having a personality and “character” we are really saying that they can be trusted to act fairly consistently – well, what kind of personality can be trusted to act inconsistently? What kind of person’s main characteristic of relationships is that they destroy relationships? What kind of person can you trust to be untrustworthy?
Wikileaks: too many people made the mistake of thinking that the enemy of their enemy was their friend. In that kind of logic, you have to constantly be aware who is whose enemy, really. Assange’s enemy is the establishment, so he’s going to turn on the establishment wherever and however it gets him the most attention. That doesn’t make him a friend of liberalism. He only appears to be liberal because liberals don’t tend to do things like extrajudicial military killings. I know I am treading dangerously close to a “no true scotsman” argument, there. Sociopaths don’t do “friend” very well and if you think this guy is anyone’s friend:
Ask Chelsea Manning.

Back when I was CEO at NFR, we got a phone call from CNN asking if I could come down and participate in an interview with Kevin Mitnick. Mitnick, at the time, was promoting one of his books – it must have been The Art of Deception, so this would have been 2002. CNN wanted someone to offer the counterpoint “… but not all hackers are good.” view because presumably they figured that Kevin was going to be blowing his horn loud and long about how he was just curious and trying to make the world a better place, etc. So I raced downtown in time to go live, got the makeup and earbud and was led into the little bluescreen room for the great American Talking Head experience. While I was sitting there, I decided I was going to play mean, so when the interview started and the first softball question triggered Kevin going into an explanation about how it was “curiosity” and he “wanted to improve security” I interrupted and said “while you’re at it, maybe you can talk about how much your curiosity cost the taxpayers for the FBI to hunt you down twice, and society to imprison you. Tell how that improved our security, too.” And my microphone went dead and I took the metro back up to the office and the adrenaline wore off, eventually.
A couple weeks later thenwife and I were eating dinner and the phone rang. It was for me, she handed it over.
(voice) “Hey this is Kevin”
Me: “Who?”
Kevin: “Kevin Mitnick. I wanted to call you and tell you what a bitch you are. You’re just mad because my book is selling better than yours.”
Me: “Oh, that. Kevin, if you think this is about money, you should look up the SEC filings under my name. I IPO’d a startup in 1997 and am on the board of directors of another publicly traded company. I don’t live off my book sales.”
Kevin: “Aren’t you wondering how I got your home phone number?”
Me: “Well, it’s on my website…”
Kevin: (click)

In this post I’ve only talked about a few of the sociopathic hackers that are out there – ones I’ve talked to, crossed swords with, cleaned up after. The “Anonymous” collective is interesting: I’m sure that some of them are using flimsy justifications for doing whatever they wanted to, in the first place. That’s why I find it so egregious that the FBI basically recruited Hector Monsegur (aka “Sabu”) after he ran around hacking a bunch of security companies and basically making a great deal of trouble. His group, “antisec”, was against computer security companies, on the flimsy basis that they supposedly felt a lot of security companies had bad security. To which I say: “Yeah? So? Are you surprised?” Sabu believed so much in what he was doing that, when the FBI collared him after a few months’ rampage, he flipped to being an informant and threw all of his old buddies under the bus, while launching FBI-sanctioned cyberattacks against companies in Brazil, Brazilian banks, and some Brazilian police stations. His friends discovered that he wasn’t their friend, apparently – he was just another sociopathic hacker who believed in nothing except gratifying his urges and saving his own skin.
There are some ideologues in Anonymous, who probably believe in whatever they are doing – whatever that is – but there are doubtless a few serious sociopaths in the Assange/Lamo/Mitnick mold: they may appear to be “on our side” as long as our interests briefly align (e.g.: in the Steubenville rape case) but they’re just as dangerously flexible as Assange or Lamo. They’ll turn on you in an instant if you give them “reason” to.
One example that comes to mind is the “Lizard Crew” that took down Xbox live and Playstation Network. They claimed it was to promote a new DDOS service that they were offering, It seems like that excuse was grafted on only after they discovered that their DDOS tool worked. That was in much the same way as the “North Korea hacking” story was grafted onto a fairly typical-seeming breakin. This sort of thing fuels a lot of my skepticism about attribution: I don’t think you should take any justification from what the sociopath hackers claim. Typical of the flexible truth of sociopaths, and their general glibness, they are perfectly capable of rapidly re-orienting their justification to make it more believable to the victims. For another example, if you believe a highly intelligent hacker who gets caught going after US Government systems was there looking for evidence of space aliens – you’re being played. He wants you to think he’s a lot dumber and a lot crazier than he is – now that he’s been caught. He could see that the “I was just curious, didn’t mean to hurt anything” angle hasn’t been working so well lately, so he’s going to try the slightly goofy conspiracy nut + aspy angle. After all, the Aspy angle worked great for Lamo.
They’re sociopaths, they’re not stupid. In fact they’re smarter than average, and they’re amoral (or close to it) and highly manipulative.

A note: Originally I split the use of Chelsea Manning’s first name, but thanks to Rob Grigjanis@#1, I understand that wasn’t the right way to do it, so I have adjusted the text. A note: because I am writing a historical narrative, I refer to Manning before he disclosed his interest in transitioning as “Bradley” and “Chelsea” afterward. I don’t know if that’s the right way to do it, and if someone tells me otherwise, I may edit the use of names.
[1] Glenn Greenwald at Salon: The Worsening Journalistic Disgrace at WIRED
(formerly)Firedoglake: Bradley Manning / Wikileaks Timeline
Wikipedia: The Texas Sharpshooter Fallacy
LA Times: ‘The Last Hacker’ He Called Himself ‘Dark Dante’ His Compulsion Led Him to Secret Files and Eventually The Bar of Justice. Kudos to LA Times for recognizing the obssessive/compulsive nature of some hackers.
WIRED: EX-Hacker Adrian Lamo Institutionalized and Diagnosed With Asperger’s
New York Times: Dismissal of Internet Security Guru Adds Fuel to Debate (Farmer was fired from Sun for releasing Satan. Mostly because, as an employee of a tech company, Satan would have been Sun’s proprietary software.)
[2] Kurt Rudder: Julian Assange, the Cypherpunk Revolutionary
[3] The Verge: Early Cypherpunk in Fact and Fiction
[4] Gawker: Hacker Who Turned in Bradley Manning is a Bigger Scumbag Than We Imagined
[5] Snopes: Julian Siezer
(* Per DSM IV sociopathy is a “personality disorder” known as “antisocial personality disorder” that demonstrates characteristics including an inability to get along with others, a lack of concern for social mores or rules, and violation of the rights of others. I am unconvinced that there is such a “disorder” but there are certainly people who exhibit those traits. For the sake of brevity I will refer to people exhibiting those traits, and related traits, as “sociopathic.” I want to be clear, however, that I am unconvinced, as the American Psychological Association appears to be, that there is a specific “disorder” that causes these behaviors. Some may be purely learned and some may be a result of neurochemistry or neurochemical over-learning. We can argue about this topic in a separate posting if any of you think it’s worth digging into. For the sake of this posting, I think we can use the term without my having to go to lengths to hedge my words skeptically.)
(** See: Argument Clinic: Linguistic Nihilism)
(*** You will also attract sociopaths, or people who want to role-play sociopaths, *ahem*, in some online games like Grand Theft Auto 5, or EVE. Note: I am not saying that these games create sociopaths, rather that these games were created as playgrounds for sociopaths. There are plenty of other games that promote guild/cooperative behavior and positive online interaction. But there are some games that specifically advertise that they implement a moral vacuum, and – surprise! You get more extreme and antisocial behaviors.)
(**** Some of us wind up shelving interesting work we were doing in massively reliable distributed systems and spending our lives working on security, instead. Security’s been interesting and lucrative but it’s not what I ever expected or wanted to be doing.)
(***** Computer security pioneer Willis Ware, at SRI, had the idea that hackers could be “reformed” but after his experience with Mitnick he concluded that there was sometimes an obsessive component that made it impossible to get them to stop. Since then there have been others, including me, who feel that way.)
(****** And with the 2016 “Russian Hackers”)
(******* Poulsen and Justin Peterson “Agent Steal” took over phone systems in the LA area so thoroughly that they ran a scam where, whenever some radio station was doing a “dial in award” they would manipulate the number so they were the only people who could dial in. Very clever. But this was not a quick hit; it was a pattern of remorseless criminal activity – not “curiousity” or “exploring”)
(******** Farmer and my old friend Wietse Venema wrote a vulnerability assessment tool called “Satan” that automated much of the recon work that a hacker would do. Chris Klaus – also a hacker-turned-entrepreneur – wrote a similar tool called ISS Scanner a little later. Vulnerability assessment tools were the original “dual use technology” in computer security and that has always caused some debate. Farmer’s choice of the name “Satan” provoked a news flurry because christians are socialized to get uncomfortable when they hear that name.)

From 2013:
I read this as saying “use Chelsea”, even for the period before disclosure of transitioning. The exceptions are rather narrow.
Erm, I have a post up called Fellow Travelers too, but it couldn’t be more different!
Caine@#2:
Erm, I have a post up called Fellow Travelers too, but it couldn’t be more different!
Yes! Imagine my surprise this morning when I saw that!
I’ve been working on this piece for most of a week, now. I’m not sure if I should re-title it or not, because the working title is how I came to think of it.
What are the odds!?
Rob Grigjanis@#1:
Thank you. Fixed.
Now I feel stupid because I didn’t research that myself, and simply picked what I thought I would want, and did that. I doubt Manning will ever read this, but, … I’m sorry and it won’t happen again.
I’m going to add a post-script of my own in the comments.
Regarding Glenn Greenwald: if you go back and research the events and exchanges of the time, Greenwald and Poulsen got into a pretty heated exchange over the amount and type of information Poulsen, acting on behalf of WIRED, was publishing. If you’re interested in journalism/journalistic ethics or Glenn Greenwald, I suggest that now is a good time to look back and review that whole period of time.
I’m not particularly interested in journalistic ethics, other than “it would be nice” but I have some respect for Greenwald. He’s clearly passionate about what he does, and he has consistently been an advocate in favor of whistleblowers and frozen peaches. OK, that’s not fair: he’s consistently been against the intelligence state’s privilege and against official secrecy. In the context of this posting, which is about how easily people are manipulated by glib sociopathic hackers, Greenwald is sort of a stand-out. His frustration and then fury at Poulsen is motivated by his support for Wikileaks (because Wikileaks aligned overtly with Greenwald’s agenda) and he’s unable to contextualize what happened except as there being some kind of plot against freedom of information and journalism.
Greenwald, in other words, was played by the sociopaths, and when that started to sink in, he couldn’t believe what was happening at first. Because he believes that what Wikileaks said it was doing was important (I do, too, if that were Wikileaks’ agenda) and he supports Assange, he defends them. My conclusion is that he made a mistake when he conflated the stated agenda of Wikileaks and the stated agenda of Assange, and believed that any of that was connected somehow with what Assange and the other hackers would or wouldn’t do.
I expect that the recent comments from Wikileaks made Greenwald’s head explode, as they made Nate Heavenstone’s as well. That pain you’re feeling is your illusions leaving your body.
I find far more alarming than the possibility that the Russians Hacked Our Election the much more likely scenario that our recent election was hacked by people as described in this piece, motivated by the idea that *it would be funny* if Donald Trump won.
What would be *funny* would be if The Donald used his new President For Life powers to murder some of these assholes from afar. And then, later, less funny things would begin to happen.
Andrew Molitor@#6:
I find far more alarming than the possibility that the Russians Hacked Our Election the much more likely scenario that our recent election was hacked by people as described in this piece, motivated by the idea that *it would be funny* if Donald Trump won.
Yup. Trolling level: superpower.
Overlong post –> overlong comment.
I’ve long had the impression that the term “hack” originated among MIT students and at that time meant “any clever programming success” – e.g., (if anachronistically) Hertzfeld writing the original Mac “tile game” DA using less than 1 KB was a neat hack. Since a lot of MIT computer science “studies” consisted in trying to finagle root passwords and prank the system, a certain degree of ethical ambiguity popped up about when “hack” turned back into a verb.
… Lamo was the hacker Chelsea Manning contacted about how to release his trove of secrets. … Poor, naif Manning. If only he’d had a real friend …
Your re-pronouning seems incomplete.
Assange went by the handle “Mendax” for a while…
which suggests “mendacious” etc. Often even the most twisted show an underlying tendency towards honesty, though trying to sort that out leads leads quickly into deep psychological weeds.
… if you’re really “curious” and “interested” about what’s on my network you can come here, sign my non-disclosure…
If you have anything of $eriou$ value in there, doesn’t the NDA add up to a way of turning your back with paper where you need Kevlar?
… Hume’s chasm…
Do you mean the is-ought differential, or have I overlooked yet another pit to fall into?
… it didn’t stop Obama from expanding his use of drone strikes… Compare the way Glenn Greenwald and Laura Poitras worked the Edward Snowden case, if you want a better example of journalistic effort…
Which also didn’t stop Obama from drone-missiling what “privacy” we had left, as he continues to do now.
Why did the FBI sic Sabu on a bunch of Brazilians?
Marcus:
No, no, it’s perfect! I’m going to fix some dinner now and actually sit down and read this.
Thanks for writing this. I’m going to snork it on my own blog. I’m usually bad at reading long posts all the way through, but I managed to do that here quite easily.
I definitely fell for Wikileaks myself, as you noted, and only recently came to that realization, as seen at my blog.
(Off-topic note: you should update the subscription options for your blog; the only one available doesn’t allow people to subscribe to your blog directly, only comments on a particular post, and the emails it sends are text-only, making them incredibly ugly [at least, in my experience].)
(for someone who spends as much time in front of a keyboard, he’s a lousy typist!)
I’ve long had the impression that the term “hack” originated among MIT students and at that time meant “any clever programming success” – e.g., (if anachronistically) Hertzfeld writing the original Mac “tile game” DA using less than 1 KB was a neat hack. Since a lot of MIT computer science “studies” consisted in trying to finagle root passwords and prank the system, a certain degree of ethical ambiguity popped up about when “hack” turned back into a verb.
Yes, that’s the accepted etomology of the word. I tried to avoid getting down into that weed-patch because (as I said) it’s been variously used to de-emphasize the damaging nature of hacking, to promote it as curiosity, or to demonize it as crime. I think the word has been so ill-used for so long and so hard that it’s probably not worth trying to come up with a definition that would please a simple majority, let alone everyone.
I will note that, under the “original MIT construction”(if I may) of the term, signifying something clever or creative – most of what today passes for “hacking” is neither. Dumpster-diving, for example, is not clever or creative; the person who first thought it up, sure, but the generations of hackers since who’ve used the technique are just following a well-worn path. Social engineering, individual exploits may be creative, but at this point it’s all mostly spamming phishing attacks where it’s not breaking and entering (which takes some creativity but is hardly creative). A lot of what’s going on in the hacking world is pretty lame, in other words. The interesting and exciting stuff appears to be coming – unfortunately – from the NSA’s TAO or “equation group”
Your re-pronouning seems incomplete.
I believe I have now fixed it. Thank you. It turns out there were several spots I missed.
>Assange went by the handle “Mendax” for a while…
which suggests “mendacious” etc. Often even the most twisted show an underlying tendency towards honesty, though trying to sort that out leads leads quickly into deep psychological weeds.
It gets deep, indeed. I don’t buy a lot of psychology. OK, I don’t buy most of psychology. But we can see certain patterns in how some criminals behave. Part of the psychologist’s problem with these people I call “socipathic hackers” is that it’s hard to decide if they are criminals or obssessive-compulsive or delusional or what. That’s part of the epistemological problem of psychology that I referred to, which is why I didn’t stick with that field after I got my BA.
If you have anything of $eriou$ value in there, doesn’t the NDA add up to a way of turning your back with paper where you need Kevlar?
Not terribly valuable anymore; a few of some people’s secrets. I stopped carrying other people’s secrets when I was doing some consulting in the middle east and decided that it’d be easier to work on paper than with a computer – the US DHS folks were too interested in my hard drive when I was coming back in, and the secret police at my client’s were too interested in my hard drive on the way out. These days when I am dealing with anything sensitive I write it down in a kids’ composition book, which I use to light my wood-furnace when I need kindling.
Back in the NFR days I paid a group of hackers to look through our internet-facing code, and they found a few things that would have been problematic if we had shipped the product with them. That was a pretty valuable effort and it allowed them to allay any curiousity they might have had, as well as to get some serious money. So, yeah.
I think the scenario that I find hard to believe is the “It was just curiousity” that led me to break into your newspaper and start reading the journalists’ email. Well, yeah, we can all be curious about these things, but they’re not exposed to public scrutiny by the choice of the person would-be being scrutinized. At a certain point, hacking started to go a bit far with that – if I want someone rummaging around in my stuff, they should ask. I will note that I am just as unhappy about the FBI and NSA doing the rummaging as I am a hacker. That’s an important point because the hackers get a little uncomfortable when they have to confront the fact that they are doing the same thing as the despised fellow traveller totalitarians.
Do you mean the is-ought differential, or have I overlooked yet another pit to fall into?
That’s the one.
Which also didn’t stop Obama from drone-missiling what “privacy” we had left, as he continues to do now.
Yes. Obama’s actions and inactions are shameful.
Why did the FBI sic Sabu on a bunch of Brazilians?
We don’t know, and he’s not telling. The FBI also whitewashed his case; I think he got a slap on the wrist with a wet noodle, but during their heyday the “antisec” crew did a lot of damage and cost a lot of money. It’s possible the FBI told him “do what you want just stop attacking US targets” or it’s possible they helped direct him to specific targets. You know, like the FBI say the Chinese and Russian secret police do? Like that.
http://motherboard.vice.com/read/exclusive-how-an-fbi-informant-helped-anonymous-hack-brazil
The whole thing stinks like a great mountain of shit. But that’s because the FBI touched it. They tend to produce stinking great mountains of shit out of whatever they touch. At least it wasn’t CIA: they prefer corpses to shit.
Update: interesting, the link I put above mentions:
logs reveal that Syria, Iran, Nigeria, Pakistan, Turkey, and other government sites fell victim to attacks orchestrated by Monsegur while he was working with the FBI
/snark
I hope he didn’t interfere with any elections
/snark
Edit:
Pierce R. Butler@#8:
And now I just burned a few hours queueing up an article about Sabu. It’ll drop monday.
Nobody really talks about Coolio anymore.
Jerome Haltom@#12:
Coolio got his act together and (I think) has been running clean ever since. There are lots of hackers who’ve seen the error of their ways and gone on to do other things. It’s the obssessive ones – the ones for whom hacking defines an essential part of their identity – who can’t let go of it, and who can’t be trusted either.
I’d normally think that once law enforcement gives you a good shake and a spanking and tells you to fly straight, you’re either going to fly straight (and we never hear from you again) or you simply are incapable of getting it, and are going to be a problem for everyone for a long time.
Really interesting post, while I already kinda had a similar view of hackers/sociopaths as you seem to, it did a better job of conveying why and gave an interesting brief history of the topic.
Just one minor formatting issue: please stay away from end notes, or at least, put them at the end of the relevant paragraph rather than the end of the article. It’s super irritating to see an asterisk and have to scroll all the way down to get the relevant information then scroll all the way back.
@Matrim (#14): Echoing your formatting frustration with the footnotes. I usually like to read footnotes “in context” as it were – that is, the asterisk prompts me to scroll to the end of the piece to read the interesting aside. However, in a piece such as this, finding where I left off is frustrating, especially on a tablet*.
What would be useful would be links back and forth between the asterisk and the footnote. Looks like this wordpress plugin might do the trick: https://wordpress.org/plugins/endnotes/screenshots/
*Reading on a tablet is my usual method. It’s easier with a desktop browser – Ctrl-F and search for a string, but still a bit of a faff.
Matrim@#14 and Sunday Afternoon@#15:
I’ll figure out a better way to do it. I like to have lots of notes and references (mostly because that tracks my mental process of how I assembled my beliefs) and usually I read annotated text through, then look at the annotations and rely on my memory to figure out what the references were. I hadn’t thought about it being annoying because I’m so used to it.
I may stop doing footnotes entirely, on the basis that “if it’s worth saying, it belongs in the text” and just drop to a tangential comment section, and then reference links.
Plan B would be to float them in a text box, like books did in the 90s, but I think that would help make the text unreadable.
Anyhow, I promise I will figure out a better way to do this, soon. Thanks for your feedback and patience.
For a perceptive look at the psyche of Julian Assange read “Ghosting” by Andrew O’Hagen in the 6 March, 2014 issue of the London Review of Books (on line at http://www.lrb.co.uk/v36/n05/andrew-ohagan/ghosting — but it’s behind a paywall).
Assange made a deal to produce his autobiography (for £600,000) for Canongate and Knopf. The publishers hired O’Hagen to ghostwrite it and sent him to meet and work with Assange long-term. The book never happened and in the article in the LRB O’Hagen describes how it didn’t happen. Suffice to say the narcissism, confabulation, paranoia and other traits described here come to the fore. It’s a good read (O’Hagen is a great writer) and a disquieting personality study.
sirbedivere@#17:
YES! Thank you! I read that in LRB when it came out, then forgot where I had seen it, and I guess because of the paywall it didn’t wind up being findable, since.
It appears to be accessible without a paywall, at the URL you gave.
It’s a fascinating read; I second your recommendation.
[meta + OT]
Marcus @16,
This platform supports ABBR tags, which any compliant browser should be able to process.
sirbedevere @ #17:
Wow. Thank you for this. I was able to read it, too, so either they’re having a free weekend or it’s not behind a paywall.
That is… disquieting. I have to admit to a bit of discomfort while reading it… Julian seemed to really trust Andrew, and I’m still getting over my need to be friends with everyone (from a childhood full of bullying). Had I been in Andrew’s shoes, I don’t know that I could have ever published something like that. Obviously that’s on me; I admire Andrew here, and I see why he felt he needed to publish it. I’m sure Andrew is now another one of Julian’s “enemies”. And poor Sarah! I wonder if she ever got out… I sort of hope she did. That does not seem like a healthy relationship. Julian is really incapable of being in a relationship.
I do have a question, though… wasn’t Chelsea Manning going by that name in early 2014, or am I off on that timeline? It seemed weird seeing her referred to as “Bradley” when that’s not her name.
In the interest of balance, I found the following article in the Guardian, written by Colin Robinson, called “In Defense of Julian Assange”.
The more I discover about Wikileaks recently, and after reading your post here, Marcus, I find myself siding more with Andrew than with Colin, but I do think it’s worth posting here, anyways. This whole thing is rather fascinating in a dark way… it would be very interesting to meet and chat with Julian Assange…
Perhaps the LRB allows a few free views before requiring a subscription? I’m a subscriber so I can get access any time but if anyone else can find the details perhaps a mention here would be worthwhile.
What stays with me from that article is how sad a character Assange seems in the end, in spite of all his reprehensible behavior.
Did you know that the 2004 PC RPG Vampire the Masquerade: Bloodlines features a hideous, sewer-dwelling vampire hacker called Mitnick as an homage to this charming fellow?
For what it is worth I like how you are using sociopath. What we call mental illnesses are collections of features that come together at a statistically higher rate. There are patterns in there that are useful to casual thought and speech though. To me the trick to doing it right is to identify the phenomena that is universally human in each diagnostic criteria. I screw things up for myself mentally if I fail.
So your people with sociopathic tendencies can be said to be informative. While I would not apply a diagnosis, I can recognise obsessive behavior and figure out how that works with such socially obsessive people. You can use little snips like understanding repeated positive reward seeking that violates the property of others.
Or thinking about how “Anonymous” as an entity is whoever wants to act politically in a perceived benefit to society (It’s like internet meets pseudonym using political phamplet writers of hundreds of years ago). Or using psychopathic behavior as a means of approaching instrumental aggression.
Another good habit is reading about diagnosis from the people who have it. That is essentially a process of social normalization to account for biases. There are selfish and selfless reasons to accept this stuff in a neutral sense. You get to figure out how to interact with others in a beneficial way and you get a very powerful way of looking at the world.
Society gets really fascinating when you start looking at it with a lot of those little universal chunks of fragmented cognition in mind.
cartomancer@#23:
Did you know that the 2004 PC RPG Vampire the Masquerade: Bloodlines features a hideous, sewer-dwelling vampire hacker called Mitnick as an homage to this charming fellow?
Filed under: “backhanded compliment”
I had no idea!
Brony@#24:
What we call mental illnesses are collections of features that come together at a statistically higher rate. There are patterns in there that are useful to casual thought and speech though. To me the trick to doing it right is to identify the phenomena that is universally human in each diagnostic criteria.
Psychology does have a real problem, though. Because they’re dealing with sometimes self-reported symptoms, measured behaviors (which are pretty easy to fake) and building inventories of them — then prescribing drug and other interventions — I wish they actually had a good cause/effect epistemology, while I recognize that maybe they can’t. The terminology is interesting and useful, but to me it’s about like saying “asshole syndrome.” Does Assange suffer from “asshole syndrome”? Yeah, as long as that’s not a diagnosis with medical or social consequences. What bothers me is that someone being diagnosed as a “sociopath” might wind up committed or legally disempowered if their actions were contextualized that way. For example, a jury might be convinced that a diagnosed sociopath was incapable of experiencing remorse, and sentence them more severely than a “plain old asshole.”
Marcus@#26:
Or the opposite — suffering from diagnosed “asshole syndrome” is something that happens to you and not something you choose to do, so it’s not entirely your fault; whereas being a plain asshole is your choice and you’re fully culpable. All the defense needs is an asshole expert* to say so.
Entirely divorced from the discussion on assholes, I wanted to say that I waited a few days to read this post, because I wanted to do it justice. It’s always a pleasure to learn new things from an eminently sensible perspective**.
* Ambiguous grammar is ambiguous.
** Please read as highest praise.
cvoinescu@#27:
Yeah, I guess “asshole syndrome” cuts both ways. I wonder how/who’d certify assholishness. Perhaps John Scalzi could be the internet’s first Master of Assholishness. (based on the old British Masters in Lunacy, per “The Ruling Class”)
Thanks for your feedback, I’m still a bit unsure as to whether I’m just wagging my jaw over here, or not, so it’s good to know I’m on some kind of track.