Let me introduce you to the “intelligence Catch-22.” In case you’re not familiar with Heller’s Catch-22, from the brilliant book by that name, it goes like this:
You cannot possibly get a medical discharge from the military based on insanity, because only insane people want to be in the military; therefore if you want to be discharged from the military you are sane and therefore your discharge is denied.
The intelligence version of that is:
If someone is talking about how Russian spies are hacking the US, they must have access to what would be classified information; if they had that access they would be unable to discuss it therefore if they are making noises out of their mouth they don’t know what they are talking about.
What happens a great deal in intelligence (and computer security) is that someone knows someone who tells them something about someone who knows something who heard it from a squirrel in a trenchcoat.* I’ve encountered squirrel-people rumors a couple of times in my career and have attempted to debunk them but it’s insanely hard, since the amount of effort it takes to debunk a lie is much greater than the amount of effort it takes to tell one.
When squirrel people design weapons systems
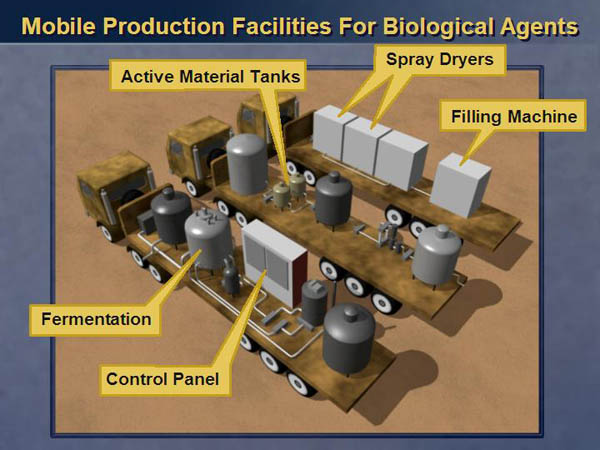
We saw a horrible case of this during the run-up to the Iraq war, where a single squirrel person, paid a bucket of peanuts, came up with a ton of “intelligence” about Iraq, including the now laughable “mobile biological warfare trucks” that Colin Powell disgraced himself over at the UN.

Google image search: seek and ye shall find
I wrestled for years with an information security entrepreneur, Alan Paller, the founder of SANS, who had been briefed by the squirrel people about chinese cyberattacks against the US, to the point where he adopted it into his belief system and amplified and promoted it at a much larger scale. Whenever I’d challenge him on his knowledge (including using the intelligence Catch-22 on him) I’d get an answer along the lines of “if you knew what I know you wouldn’t say that.”**
Today, there is a whole umbrella event called “TITAN RAIN” which is code for: “All the attacks we attributed to the same group of unknown hackers during a certain time-period. But they’re Chinese.” They’re Chinese because, we say so. The North Koreans who hacked Sony were North Koreans because, we say so. Go read the Wikipedia entry about TITAN RAIN, it contains this gem:
Adam Paller, SANS Institute research director, stated that the attacks came from individuals with “intense discipline,” and that, “no other organisation could do this if they were not a military”. Such sophistication and evidence has pointed toward the Chinese military (People’s Liberation Army) as the attackers.
Never mind it’s Alan, not Adam, the “evidence” is a simple appeal to incredulity. The logic behind it argues that Google is military, because there’s no way anyone could do what Google has done – that level of intense discipline points toward Google being military. I used to enjoy asking “How are you sure it’s not the NSA?” which usually would get me a blank look. Now, we know that my question was more likely to be the right one to ask, than “was it the Chinese?” The NSA question is not just me being a surrealist: “Sabu” the organizer of the “LulzSec” attacks on security companies, which shuttered at least one security business, turned out to be an FBI informant who had also directed attacks against corporations and government agencies in Brazil. Oh, and by the way, by Alan Paller’s logic, the LulzSec crew had to be military, too.
I’m not supposed to have this, nyaa nyaa nyaa
Another incident was the Checkpoint Firewall MOSSAD Backdoor non-incident. When Checkpoint first started making massive inroads into the US/global market, the firewall “industry” hadn’t happened yet. There were a small number of players at the time: My product, the TIS Gauntlet, Raptor’s Eagle Firewall***, Secure Computing’s Sidewinder, and Harris Corp’s Cyberguard. Checkpoint started kicking ass and taking names and suddenly the brakes were on because: there was a rumor that there was a MOSSAD backdoor in the product.**** Around that time I was having lunch with a sales guy who sold Raptor and casually commented that yeah, he thought that was a good story to start because Checkpoint was winning deals and hurting his bottom line. But the story kept going and growing, until it got to the point where I had senior people who ran a big stock exchange in New York actually tell me that they “had evidence” of the backdoor. Of course, I immediately would ask, “tell me!” but I never got anything better than “If you knew what I know…” I should have waterboarded them. Fast forward a few years and I learned through a friend who actually is a squirrel, that the NSA had done an in-depth review of the Checkpoint product, and found “only a few suspicious things.” It took me years of additional snuffling around in dark corners before I finally got my hands on the actual report.
So for the nerdy among you: in 1995, if you wanted to throw Simple Network Management Protocol (SNMP) traps out of your product, you used a library from Carnegie-Mellon University that implemented the client side of SNMP. I remember that software well, because I had resisted using it in my Gauntlet firewall since it was a horrible great wad of codespew that looked like it had been written by a college undergrad with a methamphetamine inspiration. In order to make the code “configuration free” one option was to compile the code with a set of default IP addresses; i.e.: you could hardcode the SNMP trap transmitting layer to send its packets to your network management station without having to set up a configuration file. It looks like Checkpoint used that library and, in some version, somewhere, someone turned SNMP on, didn’t provide an address, and – horror! – packets start leaving the firewall, heading to an off-network IP address. Resulting from that was a great big intelligence kerfuffle because, apparently, intelligence agencies don’t hire people who can look at a packet and go “oh, someone misconfigured SNMP on this thing. LOL.” That entire issue should have been resolved in 30 seconds and not required a dissection/review and analysis from a defense contractor working on behalf of the NSA.*****
I could tell you more, but if I did – I’d have to kill you.

I don’t want to go into attribution at length in this blog because I’ve done it elsewhere:
Marcus Ranum: Attribution is Hard, Part 1
Marcus Ranum: Attribution is Hard, Part 2
To accurately establish attribution, you need evidence and understanding:
- Evidence linking the presumed attacker to the attack
- An understanding of the attacker’s actions, supporting that evidence
- Evidence collected from other systems that matches the understanding of the attacker’s actions
- An understanding of the sequence of events during the attack, matching the evidence

(* I used to work with a guy who, literally, carried a Zero briefcase and wore a tan burberry everywhere he went. And sunglasses and sideburns. I always wondered if I grabbed him, and ripped open his shirt, if he’d collapse into a mass of squirrels as they abandoned the framework and the controls that moved the arms and legs and animated the face. The scene ends with an empty trenchcoat and a lifelike face, lying in a heap next to a shiny aluminum briefcase.)
(** I actually know a whole hell of a lot more about security than a lot of people will ever know)
(*** Which was basically a cover of my design of the DEC SEAL)
(**** You know, like NSA would do)
(***** Any of you who have detected professional contempt on my part, regarding NSA, this is just one story of many…)

… there was a rumor that there was a … backdoor in the product.
Hrrmm. Someday please tell us what you know/are allowed to about PROMIS.
So have you told Iris about these squirrel disinformation agents?
Pierce R. Butler@#1:
You’re referring to the police databases? I haven’t had much direct experience with them but, let’s just say, the times I wanted to do a query against them there were people I could call and just get the information. It’s pretty distressing. The FBI’s databases are better but mostly because they’re so backward.
I have a post I’ve been meaning to write on the topic of police and law enforcement databases. It’s scary and depressing. I usually spend a while thinking and fact checking a lot of these things before I post.
inquisitiveraven@#2:
I assume Iris has intelligence sources that relay that information. But this is not the place to talk tradecraft ;)
Marcus, amusing as they are, both the book’s Catch-22 and your version are logically flawed, since they depend on hidden (and false) premises. Not that this is particularly relevant to your article.
In passing, there was a related article in Australian news this morning:
(Gotta love the [paraphrasing] “we want to be transparent, so we deliberately won’t narrow it down to something specific” line)
John Morales@#5:
I think that was Heller’s point: the logic is completely wrong. Which was fitting for that time and situation. I don’t know if you’ve read the book (the movie’s not bad, either, though I saw it too young and was traumatized by the scene where Yossarian is traumatized trying to rescue the gunner (Art Garfunkel) I wasn’t able to watch it and think about it until I was much older.
security controls in place were insufficient to protect the network
Let me translate that from the original incompetent: “there were no security controls in place, so we got owned. Therefore it was the Chinese.”
Marcus,
Oh. Thanks!
(I started reading it decades ago, but found it boring and didn’t finish it)
Perhaps our military systems are better than our Government ones [he said wistfully].
(Or at least, please please God don’t let them be vulnerable to ransomware!)
John Morales@#7:
My experience is that military and government systems are more or less on par. Which is: bad.
The US’ Air Force drone consoles got infected with basic malware thanks to some goofy wingwiper plugging in a USB stick from his home computer (probably so he could download video illicitly of him killing someone) It took them months and several complete system re-builds to get it cleaned up (which is funny: a corporate IT manager would have had those systems in lockdown with USB lockout and so forth) The US government is very incompetent and the Australian government follows the US’ play pretty closely.
The US Office of Personnel Management hack is the quintessential stupid: it’s like they didn’t realize that they had the org chart for the entire US Government, including clearances and compartments. (eyeroll) If anyone competent had done a risk assessment there, they would have freaked. Oh, wait, they did – years before the breach and every year thereafter. OPM said they couldn’t fix stuff because it’s HARD and they didn’t have ENOUGH MONEY etc.
Marcus Ranum @ # 3: You’re referring to the police databases?
Sort of. PROMIS was an acronym for “Prosecutors’ Management Information System”, a software package developed to store and organize all the people, evidence, law, notes, etc needed by your friendly neighborhood District Attorney (et al) in complicated cases. Back in the Reagan era, a small company developed this and tried to peddle it to the Justice Dept.
Long & mostly unknown story short: some Government Spies™ saw it, decided it would work handily for their investigations. Indeed, it worked so well they got a hold of the source code, customized it a bit, and started selling it to “friendly” spook agencies – with at least one handy-dandy back door.
The developers, all bent out of shape over the petty technicality of not being paid for their product, took the case to court – apparently around the same time that Mossad, MI-6, and other allied snoopists found out they were also snoopees. Some muckrakers like Mother Jones tried to expose what they could, and at least one book was published (which I never got my hands on, and cannot presently recall the title), but between a spate of Very Serious Men Wearing Dark Glasses and Black Ties muttering about National Security®, the developers’ limited litigation budget, and oh so many other Reaganista scandals, apparently the story died even before Robert “Pills” MacFarland did.
Pierce R. Butler@#9:
PROMIS was an acronym for “Prosecutors’ Management Information System”, a software package developed to store and organize all the people, evidence, law, notes, etc needed by your friendly neighborhood District Attorney (et al) in complicated cases. Back in the Reagan era, a small company developed this and tried to peddle it to the Justice Dept.
Oh, right, that. I’ve never come across it. Inslaw was when I was in high school!
With respect to government playing fast and loose with software licensing – classification covers a myriad of mistakes, whether intentional or accidental. I don’t think they do things that way nowadays, though – instead they funnel great big bags of money through the revolving door.