This is another story in the “things I am tracking but I am not sure what they mean, yet” file. Unfortunately, we won’t (probably) know for a year or two; there are still a lot of shoes to drop.
[Edit: I wrote this monday afternoon. Since then there have been new developments, which I will comment on at the bottom. The bit about hypothetical Mossad spies inside Kaspersky Labs was kidding, when I wrote it, I swear.]
The main article about this news is behind a paywall [wsj] but it’s also summarized here [zd] – I think the coverage is fair, given how little we still understand about what happened. There are too many moving parts and agendas, though.
 Briefly, it sounds like this: there’s another leak of NSA top secret attack tools, and Kaspersky is getting blamed.
Briefly, it sounds like this: there’s another leak of NSA top secret attack tools, and Kaspersky is getting blamed.
To me, it sounds like bureaucratic deflection, to be frank: “oh, that horrible thing we did? Russians!” Isn’t this around the time we should be having a conversation about the NSA (and CIA, fwiw) developing attack tools using their massive covert budgets, then being so incompetent that they cannot keep their attack tools in their pants? Is now when we could discuss the over-reliance on untrustworthy contractors and the technical hollowing-out of the intelligence community? Would it make sense to talk a bit about how much damage and expense the leaks caused to computer users worldwide? Can we talk about accountability, responsibility, and oversight? Nah! Russians!
Elsewhere I’ve pointed out why it’s harder to defend than attack, in cyberspace – and that leads me inescapably to the conclusion that NSA (and CIA, fwiw) are on the offensive because they are incompetent at defense. The litany of leaks would bear that out. Defending is harder, but it pays off better: a defense against one enemy improves ones position against all enemies. If the US had competent cyber-security agencies, it wouldn’t be so bad – but right now, they’re leaking stuff that’s as damaging to US systems as it is to anywhere else.
Here is a complete guess as to what may have happened: Kaspersky, Sophos, Crowdstrike, McAfee, a bunch of other anti-malware companies, have “cloud whitelisting” models in their detection engines. The idea is this: when a new executable item is seen, it gets checksummed and the cloud servers are asked “have you seen this before?” the cloud servers reply one of: [ “yes, and it’s OK”, “yes, and don’t run it, it’s bad”, “never seen it.” ] In the case where the anti-malware has encountered something previously unknown there’s an option for pushing the data up to the cloud, where it’s exploded in a petri dish virtual machine, and its behaviors are scored against a litany of indicators of naughtiness. Then, the user is given the score-sheet and allowed to decide whether to run it or not, and the cloud server’s knowledge-base is updated.
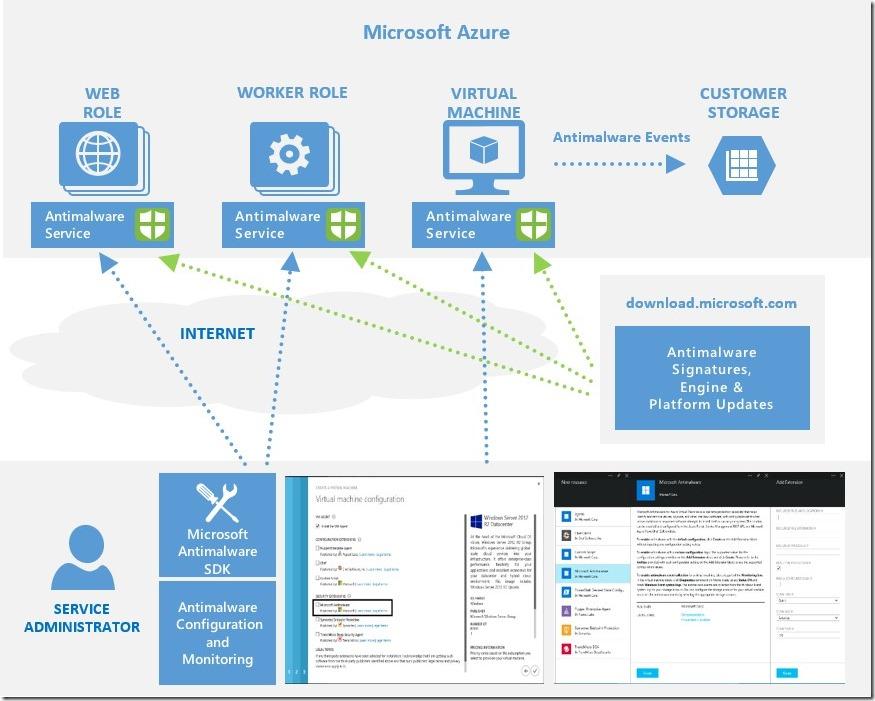
From some microsoft azure marketing puff piece
It’s what I think of as an “epistemological loop” – there’s a clean divide between “known” and “unknown” and a work-flow that transitions things between the three states I described above “known good” “known bad” and “unknown.” In most antimalware companies’ literature, that work-flow has a bunch of AI fairy dust sprinkled all over it, but it’s really just a bayesian probability analysis on top of the score-sheet. Nothing wrong with that; it works.
Now, let’s imagine that some NSA contractor has Kaspersky on their home machine (disloyal, un-American that they are!) and they steal a copy of some NSA malware. Then, perhaps, a scheduled scan kicks up, hits the malware and gets a bunch of “unknown” and schleps the malware up to the cloud into the petri dish and – minutes later – some analyst at Kaspersky goes “WTF!? I have something that just tried to compromise my petri dish using an unknown exploit! In fact, I have 14 somethings trying to do that!”
That scenario depends only on the NSA contractor being stupid enough to bring malware home and store it on a system that has anti-malware software installed on it. The same thing would happen whether it was Kaspersky or anyone else. Sure, it’s bad, but the really bad part was “NSA contractor bringing home top secret malware” – that’s the beginning of that sequence of events.
What happened next? Here’s where it’s really murky. Perhaps the FSB is smart and professional enough that they have someone inside of Kaspersky’s operation, looking for exactly that kind of event. Now that I think of it, having a cloud-based runtime management capability is a pretty good idea for a nation-state: centralize runtime control for all government agencies. If I were a sales guy for Bit-9 or one of the American anti-malware companies, right now, I’d be trying to find someone who was willing to build a service like that and give it to the US Government because, then, someone would have to own you – that property would be a critical piece of strategic high ground. If the US Government’s cybersecurity agencies weren’t incompetent nincompoops, they should have bought a site license from Bit-9 or whoever, a decade ago. Given the kind of spend the US Government has on IT, a project like that would have been easy to do in-house, and just own. Oh, right, the NSA and CIA are all about offense, not defense.
The folks at ZDnet offer three theories; I’ll take #2:
THEORY 2: KASPERSKY DETECTED MALWARE, RUSSIAN SPIES INTERVENED
What’s more likely is that the Kaspersky product detected one of the NSA’s hacking tools, taken out of the safe confines of the agency’s offices, and was flagged by the software.
“Experts said the software, in searching for malicious code, may have found samples of it in the data the contractor removed from the NSA,” said the report.
It’s not surprising that Kaspersky would recognize either known malware or hacking tools, or malware-type behavior. The company, like others, already has a wealth of antivirus signatures of leaked NSA hacking tools at its disposal, including infamous malware strains like Stuxnet — which researchers believe was developed by the NSA. Hacking tools used by the so-called Equation Group, thought to be a hacking unit within the NSA, were publicly exposed by a hacking group known as the Shadow Brokers, which initially put the classified tools up for auction. It was Kaspersky that first discovered the hacking unit.
Kaspersky products sift through files and upload samples that are flagged as dangerous to be analyzed in the cloud. Many antivirus makers do this — including Windows Defender — in part to save on local system resources, but also to allow researchers to get samples.
The other theories are:
THEORY 1: HACKERS EXPLOITED FLAW IN KASPERSKY TO STEAL DATA
THEORY 3: KASPERSKY DETECTED AND STOLE MALWARE FOR RUSSIA
Theory 1 is similar to the scenario where the FBI tried to get Apple to send down a patch version of iOS in order to unlock someone’s cellphone. It’s a credible theory if Kaspersky is as subject to government pressure as US companies are. Theory 3 is similar to the scenario of a government agency subpoena’ing someone’s cloud drive. It’s possible, too, someone stupid enough to steal NSA top secret malware and take it home might be stupid enough to put it in a file share. They’re probably stupid enough to brag about it, too.
How does the US Government know what happened? Perhaps the CIA is smart enough to also have someone inside of Kaspersky’s shop. You know, he’s the guy who joined the research time at the same time as the guy from the Mossad; too bad neither of them knows who the other works for. Does the FSB have people inside at McAfee or Crowdstrike or Microsoft? Probably not. Why not? Because the NSA and CIA’s security is so bad they hire dingbats who take home top secret malware.
Update:
According to the New York Times and Washington Post,[wp] Israeli spies hacked Kaspersky, and that is where the story comes from – they noticed that Kaspersky Labs had the NSA’s malware and notified NSA. The situation is kind of Keystone Kops: NSA are so incompetent that they discover their malware was stolen when the Israelis, who are hacking a Russian company, stumble over it. I’m not sure where the fingers are going to point: we get all sorts of complaints about Chinese, Russian, or North Korean hackers attacking American companies, so I’m sure there will be fingers of outrage pointed at Israel, right? Or will there be probing questions about the NSA’s lack of competence? The Israelis probably already have the full archive of NSA malware; it was developed and given to them, allegedly, as they are the ones who allegedly deployed Stuxnet. The US Government is currently partway into pitching a fit about having systems compromised by a foreign power, while compromising the systems of a foreign power, and trading in its own secrets with another foreign power.
Elsewhere, I have described cyberwar as a “weapon of privilege” – a weapon that the dominant power feels free to use, makes dire threats of retaliation against anyone who’d use it on them. I’m afraid that the evolution of US cyber-policy is completing the trajectory I predicted back in 2001.

“I’d be trying to find someone who was willing to build a service like that and give it to the US Government” – I’ve suggested that several times before, to some of those companies. Mostly, they are too busy printing money following their existing sales model. I even suggested the idea to Howard Schmidt when he was president Obama’s cybersecurity advisor; his take was that nothing that good ever happens. (My words not his) I estimate the whole service would cost under $5m to build and about $1m/year to maintain.
“Elsewhere I’ve pointed out why it’s harder to defend than attack, in cyberspace” – I used to have a few postings about cyberwar grand strategy on the fabius maximus site, but the editor started to veer uncomfortably toward global warming denialism and equivocation about white supremacists, and I asked him to remove my material from the site because I didn’t want to be embarrassed by association. Eventually I’ll re-write the arguments.
In 1995 or so, I got stuck in the middle of some controversy regarding Checkpoint’s Firewall-1 firewall software. There were rumors of a Mossad backdoor in the firewall. These rumors were persistent and widespread and it was pretty much impossible to quash them – that’s how rumors work. I happened to know that the rumors had been planted by a value-added reseller who specialized in federal agency sales for a company called Raptor, which made a competing product. He planted the rumor to wall Checkpoint out of the market that he was selling into. 7 or so years later, a guy I knew who used to work for Computer Sciences Corp, took me aside and gave me copies of the NSA’s report – CSC did the analysis for NSA (even then, NSA was sliding into incompetence) – and he was one of the team that decompiled the product and figured out what it did. It’s probably OK to post that stuff now. It may no longer be interesting but I laughed long and hard, at the time.
One thing I do not like about the ZD article is that it promotes the waffle: “including infamous malware strains like Stuxnet — which researchers believe was developed by the NSA” Um, no. Stuxnet was developed by NSA, full stop. If the media is willing to accept and repeat the FBI’s claims that Russians were involved in hacking based on IP addresses, they damn well need to accept that the NSA caused Stuxnet to be developed based on detailed examination of code fragments and the gene-lines of different malware releases and when they were discovered.
Israel deploying Stuxnet: there is a lot of caginess about that (claim made by the Obama administration and others) and reporting continues to apply a fig-leaf of vagueness. Why? Because, if the US developed Stuxnet and gave it to Israel, the US also developed Flame and Duqu – it’s tricky and complicated; the landscape of malware has NSA’s fingerprints all over it: [cnet]

Really? In this day and age, infosec companies are very much high-value targets, and I expect that all competent (and most incompetent) national security agencies devote about as much effort to compromising them as they do to compromising diplomatic missions, the military, and rival (in all senses of the word) national security agencies. There’s an interesting question there as to whether the companies in question realise this and take appropriate counter-intelligence measures, but I would assume that they do. So of course Mossad has someone inside Kaspersky. They almost certainly also have someone inside any other infosec company you care to name, as do the NSA, MI6, the FSB, and half-a-dozen other agencies from around the world. And of course none of the people working for any of those agencies are (formally) aware of each other – they’re probably not even (formally) aware of any other people working for the same agency. And everybody’s playing guessing games about who the other players are and whose side they’re on…
I kept reading, e.g., the Azure service that Microsoft provides, as “animalware”, and it sounds positively beastly.
Pierce R. Butler@#2:
I kept reading, e.g., the Azure service that Microsoft provides, as “animalware”, and it sounds positively beastly.
When machine is infested with animalware, machine eats you.
Dunc@#1:
So of course Mossad has someone inside Kaspersky. They almost certainly also have someone inside any other infosec company you care to name, as do the NSA, MI6, the FSB, and half-a-dozen other agencies from around the world.
That’s how it’s starting to look, isn’t it?
I’m not sure if it’s “someone inside” or just that the companies are deeply owned. I was not at all happy to hear that Kaspersky was apparently owned by both the Israelis and Russians – that’s not exactly doing “a great job” of malware detection for a company that does “malware detection.”
I wonder if there’s an insider, or how these compromises are done. I tend to assume an insider because it’s more reliable, they get medical benefits and stock options, and they’re harder to detect. Malware offers a great bit of plausible deniability, too: the insider can just hang out, do their job, keep track of what’s going on, and if the malware gets discovered, then they wait till a co-worker goes to the bathroom and they put a USB dongle in their machine for a second, then go back to work. Since the security companies are always (in principle) trying to improve their products, it’d be useful to have someone in the pre-release stream so that there wouldn’t be any embarrassing moments when a new version of the product reveals that the corporation’s own systems are massively owned. That would mean that you’d want your agent to be a QA engineer.
It’s probably both.
Also, I strongly suspect that many infosec companies have relationships with state security agencies not entirely unlike those between the military and their major contractors.
Dunc@#5:
Also, I strongly suspect that many infosec companies have relationships with state security agencies not entirely unlike those between the military and their major contractors.
I absolutely know for a fact that they do. It’s usually pretty hands-off, though. Like the NSA paying RSA $10 mil to let them “help” with implementing some crypto routines. [reuters]
We should probably assume the Russian government is able to apply pressure on a Russian company, the same way the FBI is able to apply pressure on Apple. Usually, it’s “hey we’re a really big customer of yours. Can we have your source code? So we can escrow a copy.” Yadda yadda. And in some of those cases, it’s probably legit: they want to diff new versions and see if the Mossad is adding backdoors, etc.
The whole system sucks because internet security is bad enough without having well-funded government agencies going around deliberately making it worse.
Well, yeah, there’s the RSA thing and the like, but that’s the stuff we know about – spooks, by definition, specialise in getting up to shit that nobody knows about, so I assume that there’s a heck of a lot more. Who’s the NSA’s equivalent of In-Q-Tel?
Dunc@#7:
Who’s the NSA’s equivalent of In-Q-Tel?
X Group and DARPA. But I think In-Q-Tel also shares some of their agenda.
Look at those names, they’re like silly boys playing 007. Sheesh.
I share your belief that covert operations are about like mice: if you see one, it means there are dozens. I don’t know the ratio; of course that would be classified.