As you can probably guess, I get a lot of emails related to whatever’s going on in the security world. There was a very short buzz around the “Russia Hacking” thing but very few security practitioners care about it at all. Except one, who sent me this:
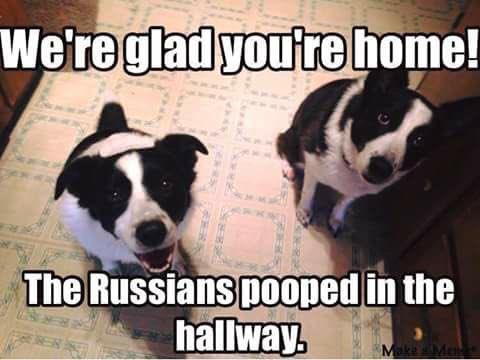
Someone on the internet did this, I know not who
That pretty much summarizes how I feel about the whole thing. Now that the US Government has officially blamed Russia for its rulers being so stupid as to fall for basic phishing attacks, they’ve piled on and also blamed a couple Russian cybercriminals and security researcher Alisa Shevchenko.*
So, the unknown artist on the internet who created the dog poop meme pretty much got it right: those extra pounds that recently materialized around my waist – probably put there by the Russians. That fart in the elevator? Probably Russian. My washing machine has been acting up lately, it’s probably “Operation Whirling Bear” and APT Gruppe Panzerfaust 2.0 behind it.
All of this fuss and drama, when the obvious and straightforward solution is: don’t have your security completely suck.
Here is my own contribution:

FNORD FNORD FNORD FNORD

“Security researchers” like Alisa, Equation Group, Cult of the Dead Cow, and Hacking Team[2] have had free rein to act and sell exploits on the edges of the security scene for decades or more.
(* The Daily Beast article[1] asks rhetorically whether Shevchenko may have had a hand in the DNC hack. Considering that the DNC hack was something that anyone with basic tools could accomplish, I’d say “who cares?”)
[1]The Daily Beast: Did This Mysterious Female Hacker Help Crack the DNC?
[2]Foreign Policy: Fear This Man (Dave Vincenzetti and Hacking Team)
Marcus Ranum at Fabius Maximus site: In Cyberspace the Best Defense is a Strong Defense

So, the Russians are behind the squirrel attacks? Or are the squirrels behind the Russians?
I can neither confirm nor deny.
I have seen many posts sceptical of the russian hackers meme here and elsewhere, and denunciations of the evidence as being underwhelming, but I have not really seen an explanation as to why it is so. Is there an examination of the ‘russian hacking’ case and the details provided by the government in plain, non-expert language for us internet amateurs to look at?
Holms@#3:
Interesting question. Offhand, I don’t think there is one.
Here’s what: (treat this is opinion; I know you will anyway) there are a number of experts in the field including myself that are saying this “attribution” is not good enough. There are others that dismiss it outright because the attribution is not good enough. I see that latter as a skepticism fail and interpret it as motivated reasoning; I think the correct response is to say “I’m not convinced – do better!” not “I am sure it’s Russians” or “I am sure it’s NOT Russians.” My view is that I’m uninformed and I don’t like that one bit, because I am expected to believe the government based on really bad evidence.
In my paper here: ( https://fabiusmaximus.com/2011/10/21/30004/ ) I contrast the attribution of international marine salvage experts regarding the sinking of the South Korean ship Cheonan and the kind of evidence that can be assembled and should be presented for cyberattacks as well. I am considered “hard core” and “extremely skeptical” in the security community and probably demand a higher standard of attribution than most of my peers, but in turn most of my peers also expect better attribution than the government is providing in this case.
The standard for attribution that I want is: (per my article https://www.tenable.com/blog/attribution-is-hard-part-1 )
There are examples of this being done, in computer security. For example, Kaspersky’s paper deconstructing the actions and code-evolution of “the equation group” is conclusive: it places technology, time-lines, derivation of pieces of software, and the purpose to which the software was put. Kaspersky stops short of saying “Equation Group is NSA” because they can’t – but they point out that Equation Group clearly developed Stuxnet, which the US has admitted it used on Iran. The Kaspersky report is not readable by the average person off the street, but a programmer with any understanding of software development will immediately understand it and be able to follow their reasoning.
https://securelist.com/files/2015/02/Equation_group_questions_and_answers.pdf
Another example of attribution was a paper by Mandiant called “APT 1” which did a pretty good job of profiling Chinese cyberespionage operations — but which did not manage to close the loop by actually placing APT1 behind the keyboard of actual attacks. I know something about how that report was produced and I am comfortable that the traces they based it on were accurate; they were not allowed to publish that information because their customer owned control of it.
https://www.fireeye.com/content/dam/fireeye-www/services/pdfs/mandiant-apt1-report.pdf
That latter point is particularly difficult with the government. They expect consultants to keep their secrets for them, even though they can’t keep them, themselves, and I think it’s mostly because the way they get hacked shows how horrible their security is. For example, the attack used to break into Podesta’s email was laughably basic – it says more about how stupid Podesta is than how clever the hackers were.
Nomally with a technical problem I expect a tree of analysis to form: the deep domain experts look at the nitty gritty stuff and give it the thumbs up/down and then the “popularizers” give higher level analysis of the deep experts’ opinions and eventually the reader gets something that’s basically peer reviewed and fact-checked. That was my experience with how the room temperature fusion kerfuffle played out, for example: I don’t understand the physics beyond wondering why, if there was fusion, the experimenters didn’t suffer radiation sickness – but I waited for that tree of analysis to form and was able to pick the issue apart thanks to watered-down versions of expert consensus.
And that’s why I’m so unhappy with the government’s approach to this problem: they’re telling the domain experts “trust us” and they’re pissed off that we’re not just saluting and saying “we believe you.” I think computer security practitioners are owed better information from their government, so we can help make thier case, for them, better. But they aren’t doing it. Which immediately makes me think that they actually have no case.
More –
So why is it underwhelming?
The bits that they did provide don’t point conclusively to anything. The indicators of compromise they posted don’t point to a piece of software being used that is well attributed to Russia, and the IP addresses they posted are onion router addresses that are typical of any hacker, anywhere. So they have demonstrated that the attack was accomplished using typical tools in typical ways. That’s not good enough.
Imagine that your house was broken into and your toaster was stolen. The police say “It’s Fred. We’ll go arrest him.” You point out that the door was broken by someone apparently smashing it with their shoulder. “Yeah, Fred does that.” And you say “and don’t other people occasionally steal toasters?” They reply, “well, Fred specializes in small kitchen appliances, and he’s been known to steal toasters”
Is that good enough for you?
Well, if they served a warrant on Fred and found your toaster, sure, that places the crime soundly on Fred. But if all they’re saying is that someone broke a door (as many burglars do) and stole an appliance (as many burglars do) you’d be right to be uncomfortable with the attribution to Fred unless there was more evidence. It could be that Fred’s size 14 boot-print is on the door and Fred exclusively wears Mephisto hiking boots and that’s a very specific thing to Fred, then the attribution gets better.
So, I don’t like arguing by analogy but approximately what the US Government is doing is saying “shouldering in doors and stealing appliances is Fred’s thing, he did it, we’re sure.”
This sort of reminds me of the Climategate thing; the general narrative was all ‘hacked by climate sceptics, trust us’ yet the only person I saw reading through the email headers to piece together the university internal network setup disagreed and was completely ignored.
http://www.smalldeadanimals.com/FOIA_Leaked/
As far as I can tell this had exactly zero circulation except on climate dissenter websites, but to my very limited eye, the argument being made actually looked pretty reasonable.
Holms@#6:
I haven’t looked at the climategate stuff, but now I can see I’m going to.
By the way, I apologize for the general incoherence of my comments last night. I had just flown in on a late flight, done a day of meetings, and then drove home through 80 miles of snow, jagged on caffeine and adrenaline. I shouldn’t have been commenting at all.
Holms@#6:
I’ve reviewed the climategate article you referred to. It’s interesting! The fellow who wrote it’s analysis is pretty good. There are some parts I disagree with – he asserts that it would be hard to :
I wouldn’t say “extraordinary” – this is all pretty basic stuff. Furthermore, it’s pretty easy to see what machines contain what, by looking where administrators log in from, where system logs are configured to go, “last login” for admin, what systems backup dumps go to, etc. The odds that an exploit would be needed against specific machines is probably zero – most places that are not crazy about security will have a common administrative password or shared executable filesystems. Once you’re on one machine in a cluster, the rest of the cluster is, for all intents and purposes, compromised.
The other stuff, about the data files, how the script works, etc, – that’s all spot on.
The emails in ordered format might have been pulled from a POP or IMAP server, or from a local cache that had been kept ordered. For example, if someone accessed my personal email archive they would get 15 years of correctly ordered emails (because I occasionally run a compaction process across them that deletes spam and writes out the despammed files in time sequence)
It doesn’t look suspicious, though. That’s all basic operations stuff. What’s suspicious is a scenario where it goes like this:
– I am served a subpoena for all my emails
– Someone looks at my emails and sees 15 emails between me and Holms
– Someone asks Holms and Holms says “15? are you kidding? we talk a lot!” and Holms shows he has 2,500 emails between us
If the idea is that the climate scientists are altering data and hiding it, I’m disinclined to believe that. Doing that right is a lot of work (and it still usually doesn’t fool anyone)
For example, I did a forensic gig back in 1998 where this one guy had a rather interesting hole in a bunch of emails. In fact, the guy apparently got no emails at all on a certain day. Which was weird because EVERY OTHER DAY THAT YEAR the guy got: calendar reminder, joke of the day, rotisserie league email, etc. Uh, yeah. And what was more interesting than that was that edge server logs recovered from backup showed that his calendar reminders for that day were sent and received – they just “weren’t in his trash or in his in-box.” Of course what he had done was deleted his messages for that day in a blind panic, and then deleted them from the trash, then compacted both files. But he couldn’t compact the server logs.