Internet security is complicated and there are lots of dependencies – usually if you ask an internet security practitioner “is ${this thing} safe?” they’ll tell you “if you’re trying to do ${this} or ${that} then…” and carry on for a half an hour in that vein.
Another problem with communicating about internet security is that it has a lot of wonk appeal but most people seem to be dismissive of it. That’s the reason why security practitioners often say (behind closed doors) that the main pleasure of working in security is being able to say “I told you so.” In my case, as someone who consults on high-profile breach response, I get to charge my clients an awful lot of money to say that. Sometimes, very, very, rarely I get a call from an old client, “Hey, that thing you told us to do a couple years ago? We did it, and it just saved my job.” I love those calls more than the more typical, “can you get on a plane out here for a couple of days? We have a situation.”
So, here’s a site [securityplanner.org] you can point your ageing parents at, if you don’t want to have to explain it to them point-by-point. I’ve reviewed its suggestions and I think they are generally excellent. Of course, they’re things I’ve been saying for years: use password vaults, don’t use the same password anywhere, use random passwords, store some in devices and some vault-only, use two-factor authentication on web sites that offer it, that sort of thing.
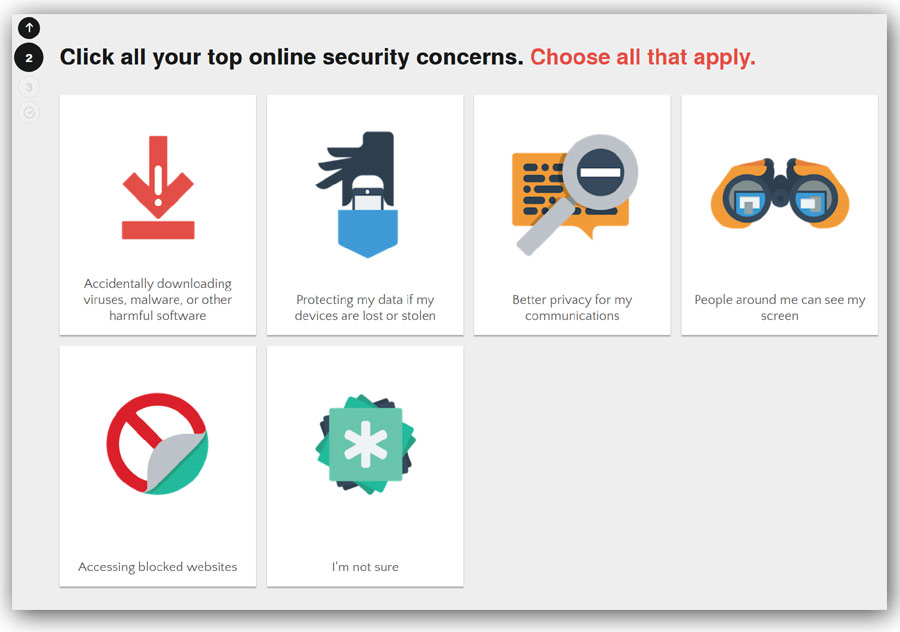
One of the nice things about the site is that it asks you about your concerns – what we security wonks would call “threat model.” Usually, if I were dialoguing with someone, I’d be asking them similar questions, off a long-established decision-tree that’s in my head. Here, it’s been turned into javascript. (I guess that’ll teach me not to think highly of what’s in my head)
Once you tell it what you’re worried about, it builds you a punch-list of recommendations, sorted from most important to least.

It also gives you links to all the details for how to do whatever it recommends. That’s pretty cool – it’s a single-point reference instead of a great big shopping list of recommendations.
If you don’t want to be stuck in the role of IT security consultant for your friends – point them at the site. [securityplanner.org]
Usually, when I post suggestions for computer security-related practices, there’s at least one of you who says, “… yeah, but that doesn’t apply to me.” Sure, yes, I get that. Here’s how it works: sometimes you get lucky, sometimes you don’t. I’m always happy to see someone get lucky, but nearly 100% of my clients didn’t. Your perception of risk is probably based on your having used the internet for years (decades, even) with no problems – if you’re one of the lucky ones. My perception of risk is based on having to do damage control on disasters for decades. It’s a lot of “I told you so.”

Hat tip to abbeycadabra [stderr] who suggested I review the site.
I would consider these recommendations to be “consumer grade” security – good suggestions for most purposes, but if your threat model includes CIA/NSA/Mossad/CSE/GCHQ/FSB, consumer grade security won’t do the trick. In fact, I’m not sure anything will.

I’ve looked at securityplanner.org when abbeycadabra mentioned it, and it seemed to agree with what you had said earlier. Only three things raised questions in the scenario I tried.
One, they say that if you use SSL, “[…] governments, Internet Service Providers, and other third parties won’t be able to snoop on the information you enter into webforms […]”. I would rate that probably false; true; and true except rare brief windows of time when it’s not, respectively. Am I far off?
Two, they recommend GlassWire. I don’t know anything about them — are they trustworthy?
And three, they said I might want to use a VPN, because it’s “good practice”. Is it? I did not select any of the more paranoid options — I did not say I was concerned about government snooping, for instance (if they really want to do it, they will anyway).
cvoinescu@#1:
One, they say that if you use SSL, “[…] governments, Internet Service Providers, and other third parties won’t be able to snoop on the information you enter into webforms […]”. I would rate that probably false; true; and true except rare brief windows of time when it’s not, respectively. Am I far off?
I’d say you are correct. But then I’ve never been a believer in SSL – I believe it is a deliberately flawed design and that puts me in “grab your tinfoil hat!” territory for a lot of security people. On the other hand, I do favor use of SSL because it causes the FBI and NSA a minor problem – a very minor one – when they try to say “there is no expectation of privacy on wifi/cellular data” because “of course there was an expectation of privacy – that’s why I was using SSL.” Naturally, the US government, so concerned about “rule of law” ignores arguments like that anyway, but they must be made.
Glasswire’s OK – it’s a lightweight analytical thing that lets you observe some of the activity on your system. It’s useful for detecting possible malware, if you’re concerned about that. I’ve given up trying to detect malware any more and just assume my systems are all compromised. I know people who use it and are pretty happy with it.
And three, they said I might want to use a VPN, because it’s “good practice”. Is it?
I don’t, but it’s worth considering. The VPN option goes a long way toward defeating ISPs that track their customers (which is basically all of them) and sell the marketing data. The question is whether that matters or not. I doubt it adds much in terms of resistance to any particular kind of attack. Some VPN services do interesting things on the backend to try to detect malware traces or block the worst of the malware ads. That’s probably worthwhile. I don’t use them because I have crappy bandwidth and anything that causes any additional delay is not anything I want.
I realize as I read this that I’ve pretty much given up. Which is bad, since – as a practitioner and consultant – I probably can’t tell my clients “hey, just give up.” I’m going to have to think about that.
Happy to be the bearer of useful news. I have to say, I thought the recommendations and threat model looked reasonable, but I am no sort of security expert – I’m that sort of software developer who’s just paranoid enough to know NOT to try to roll my own solutions or assume I a priori know what’s out there.
Do think about that, Marcus, yeah. I’d noticed a strong fatalistic streak in your security talks. It’s almost to the point where I have to ask: is there any overlap at all between that group of technological malefactors (ALL of ’em, from script kiddies to the panopticon) that we should be worried about thwarting, and that group that we have any chance of thwarting?
abbeycadabra@#3:
Do think about that, Marcus, yeah. I’d noticed a strong fatalistic streak in your security talks
I think sausage-makers tend to prefer not to eat hot dogs.
is there any overlap at all between that group of technological malefactors (ALL of ’em, from script kiddies to the panopticon) that we should be worried about thwarting, and that group that we have any chance of thwarting?
Basic internet security is OK against the basic threat models. Beyond that, I think it all falls apart very fast.
When it comes to common-or-garden cyber criminals, it’s very much like the old joke about the two guys running away from the bear: “I don’t need to outrun the bear, I just need to outrun you”.
There is no lock that can’t be defeated by the truly determined thief, but a simple mortice on your front door is enough to deter the average thief. They’re not necessarily looking to rob you in particular, so they’ll move on to lower hanging fruit if you take even basic precautions. The existence of professional safecrackers doesn’t mean it’s not worth locking your doors.
Dunc@#5:
There is no lock that can’t be defeated by the truly determined thief, but a simple mortice on your front door is enough to deter the average thief. They’re not necessarily looking to rob you in particular, so they’ll move on to lower hanging fruit if you take even basic precautions.
The bear joke is a staple in the security community.
Your two sentences there are a neat summary of threat assessment. You prepare for the worst that you need to handle, but that doesn’t mean you don’t also need to deal with the run-of-the-mill stuff. Most practitioners focus on the worst-case threat because there’s generally overlap downward: if my network can keep out Mossad agents, it can probably keep out script kiddies. The trick is always to figure out what is the worst-case threat, and then to see if there is a response to it.
What I’m afraid of is that there are no practical responses against a certain threat level. For example, I believe that all of the operating systems we have available to us are subverted. Most of the hardware is (the Intel Management Engine backdoor being one example that is well-documented) subverted. The architecture of most hardware makes subversion easy, too. And application software is full of holes and offers opportunities for subversion. I have reason to suspect that most public cryptography has been subverted, too. Here’s your tinfoil hat! But what would it look like to build a non-subverted system? You’d need to start with hardware and build upward – and entirely modularized hardware and software stack in which the components that could be subverted were walled from those that shouldn’t be. There have been systems built like that, the most notable being MULTICS. But it would be relatively expensive. If I were CTO of a reasonable-sized nation, though, I would pay that price and be working on it; the US’ intelligence agencies appear to have subverted the entire global internet software and hardware stack! Building anything on what we currently have comes with a virtual backdoor for American spy agencies (and anyone else who learns about the backdoors when the NSA/CIA leak them, which they seem to be doing a lot lately)
Sure, you’re probably right – but when you start trying to deal with MOSSAD / CIA / NSA level threats, there is literally no solution. They’ll break into your house and physically modify your hardware if need be – and even if you were to come up with a defense against that, they have the option of abducting and torturing you. There is no combination of hardware or software that can protect you against spending ten years in a cage at Gitmo. So yeah, there’s a level of threat that’s well beyond any IT security measures… But I don’t see much point in worrying about, for more-or-less the same reason I don’t carry meteorite insurance.
Let me put it this way: trying to restrain or resist the National Security State through hardware or software measures is like trying to devise a system of zoning regulations and anti-vandalism ordinances to prevent Godzilla from destroying downtown Tokyo. You can pass all the regulations you like, but Godzilla is not going to restrict his activities to the designated areas or carry third-party insurance, because Godzilla is a gigantic radioactive monster who does not recognise the rule of law or the concept of private property. He will not respond to court documents, or attend anger management classes. He’s just going to smash the fuck out of anything that gets on his way and then disappear beneath the waves. As long as he exists at all, everybody is just going to have to live with that.
Dunc@#6:
Pretty much.
Did you know that if your play a Godzilla movie backwards he repairs Tokyo and then moonwalks out to sea, after inhaling puffs of fire?
To Dunc:
Sure there is a defense. It’s just out of the budget of most people. Small nations could afford it though. Of course, the ultimate threat level is that the United States military openly invades your country, and I agree that there’s little to no practical defense against except a nuclear deterrent and a large and modern army (i.e. China and Russia).