I keep a few canary accounts. Those are email accounts that I don’t use to send anything, but I use to sign up to various sites. I used to do this so I could track which conferences sold their contact databases to spammers or marketers. On my ranum.com server, I set up forwarders that push most of the flood into my inbox, which uses bayesian spam classifiers to sort out the gunk.
Typical morning, I get 800 or so new messages in my inbox, 740 or so which go directly into the junk bin. Of the remainder there are usually a dozen or two that I actually read, and a few bits of product alerts (“your new thingum needs new firmware!”)
This morning, I had a message in my inbox that was aimed at one of my canary accounts, and was nice enough to even put it in the Subject: line.
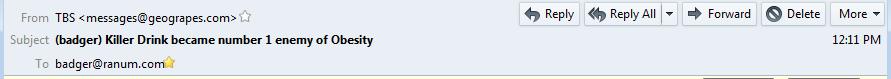
So that tells me that a certain very large social media site has leaked its email user database, which probably means its entire customer database is out there.
It’s probably Russian cyberspies up to their usual tricks: drop $1b in valuation of a great big publicly traded social media site and you’ve manipulated the US stock market!
If/when the news breaks, I get to say “I told you so.” That’s one of the few abiding satisfactions of working in information security.

This idea occurred to me a long time ago: if one were to set up a far-flung and organized set of canary accounts, it would be possible to determine who had leaked, and when. For example, I know “badger@ranum.com” is now burned but what if I had three canaries on that big social media site? If I got hits on all three, I could be pretty sure the whole customer database had left the barn. Then, I suppose I could short their stock and wait a while before I contacted the media. Back in the day, I came up with a whole series of desktop stock market manipulation concepts that I am pretty sure would make money fairly reliably. Since I’m so fortunate as to be pretty employable, I can stick to the straight and narrow. For now.
The “Canary” technique is widely used in large-scale spam blocking. You set up canaries that are easily collected by grazer-bots looking for email addresses, and – when the canaries start getting messages – those messages are known to be spam because there’s no actual person who would ever receive them. The messages collected on the canaries are immediately backfed into the spam classification codex, the originating IPs get downrated, etc. Basically, it’s a spam honeypot. Honeypots are a great tactical tool for security: it’s a system that’s value is in being attacked or compromised. Between 1999 and 2002 or so, I used to teach a 3 day class for SANS with Lance Spitzner; I think we were personally responsible for the blossoming of entire sensor-webs of honeypots. I remember I was always surprised by how easy it is to get hackers to stumble into your prepared kill-zone: they’re very very self-confident. That was when I interviewed one at a conference and discovered that the hackers never even contemplate the potential that they’ll be detected: security is so bad, that being detected (let alone personally identified) is generally not a concern.

So…I’m happy I’m not a large social media site customer?
… a certain very large social media site has leaked its email user database…
Or had it siphoned out – but the difference between selling it and spilling it from sloppy handling means next-to-nothing in terms of consequences.
Trump has a pretty good US stock manipulation scheme going with his tweets. Do you think he, his family or his entourage takes advantage of it?
Caine@#1:
So…I’m happy I’m not a large social media site customer?
In general, yes!
This does illustrate another point that’s worth repeating: don’t even use the same passwords across systems. A distressing percentage of the population does that, and when a user database on one site gets compromised, then it can be used in an offline attack to compromise accounts on other sites. A surprising number of celebrity breaches happen that way. You know, “russian hackers” …
Pierce R. Butler@#2:
Or had it siphoned out – but the difference between selling it and spilling it from sloppy handling means next-to-nothing in terms of consequences.
In terms of the amount of spam you’ll get, that’s true. Where it really hurts is if the password hashes get dumped. That’s when there’s a whole lot of bleeding (and it’s probably equally frequent) They Yahoo! breach was one where the entire customer database including hashes was compromised. They had every reason to believe that many many of their users were going to be hacked as a consequence, but still sat on that information for several years. They were very very naughty.
The site my canary was on is not Yahoo! It’s Footbook, and it’s an account I don’t log into and have a very strong password on. There is no mapping I’m aware of between the user name and the notification email, so I currently suspect that Footbook’s user database may have gone walkies.
I don’t set my canaries up carefully (I just do it out of curiousity and not for serious effect) If I were setting them up as a professional exercise, like some of my friends do, I’d have crackable but not guessable passwords on them, and the endpoint account (in this case badger@ranum.com) would actually allow login into a captive account on a ranum.com server, so I could see if anyone came knocking on that door. And then I’d be able to collect their IP addresses and map them to Russia!! $$Profit$$!
Jean@#3:
Trump has a pretty good US stock manipulation scheme going with his tweets. Do you think he, his family or his entourage takes advantage of it?
They’d be crazy not to. So, they probably aren’t. Others probably are.
What you can bet is that there are day-traders following Trump’s twitter-feed and trying to jump short on companies Trump dishes on. That’s legit. The folks who do the computerized fraud detection for insider trading are actually my old friends at Depository Trust Clearing Company; they do some neat stuff including correlating transaction times with news feeds. So, if you knew Trump was going to say something stupid about Lockheed Martin, you’d get caught if you pushed your trade before Trump blew the tweet. Once the tweet hit then you’d be OK because now it’s public knowledge.
A depressing fact is that the SEC only does under 100 insider trading investigations annually, and it’s very rare that anyone gets prosecuted, because the criminals are rich and can afford good lawyers and – besides – it’s professional courtesy between oligarchs. The stock market is inherently corrupt. Any appearance that it’s not is purely intentional. (On the other hand, since it’s tied to the economy, you can still do OK as a small investor, because “a rising tide lifts all boats” – but on Wall St some boats rise a whole lot more than the others…)
I wonder about accounts that have 2 step authentication? I have sloppy security, I use passwords that I remember, instead of a password locker. I tried a password locker and forgot the password to it, so lost those passwords!
Anyway, I did enable 2 step authentication where I could, so if a hacker got my login and password hash, they’d need to get my phone too for those accounts, no? I wonder who that Russian is knocking at my door, brb…..
The biggest hit I’ve taken was with Apple. I had my AppleID linked to my credit card. The card expired and I was sick at the time, so I thought while on sick leave I’d buy a few RTS type apps to play. I updated the card details and spent about $10 on the app. Next day at the shopping centre, went to use the card and it was maxed out. There was a bank branch nearby and I alerted them. They killed the card, gave another one and put a hold on the debt that we claimed wasn’t ours. Someone had spent big on computers at OfficeWorks using our card. In the end, the bank accepted it wasn’t us, so we didn’t repay. Just an inconvenience. Still don’t quite understand why there wasn’t a news item about Apple having been hacked, but the bank said we weren’t the only Apple users at the time to have been done….It wasn’t phishing, as I did change the details myself, not click on a link, through Apple channels.
Brian English@#7:
I use passwords that I remember, instead of a password locker. I tried a password locker and forgot the password to it, so lost those passwords!
Don’t do that!! NooooOOOOOOOO!!!
Should I do a posting on how to bootstrap to using a password locker?
So, even thought the password is something unusual, but memorable to me, and has 2 step authentication, it’s no good?
I’ll look into a password locker again. :)
Yes, please!
Long time lurker here. I find your advice very useful. Password Security is something laypeople like me my friends and coworkers totally seem to underestimate.
Yes please! :)
OK, I’ll do a bit on passwords soon. It’ll depend on if I get stuck in an airport overnight or otherwise have a good block of time …
Brian English@#9:
Short form: don’t think of them as passwords, think of them as passphrases and make them long but memorable. For example, I used to use: “TheBestOfTimes&TheWorstOfTimes”
Something like that is effectively un-bruteforceable. Then use your mobile phone for your password vault. 2factor is also good.
Well, I do the first. That’s what I was getting at long, but memorable passwords.
How does one use the mobile phone for passwords on the PC? Can’t cut an paste, and emailing clear text seems a weak spot.