One of the frequently recurring arguments offered by those supporting the widespread NSA surveillance programs is that this should not bother anyone who has nothing to hide. While this is a spurious argument at the best of times, it has a sinister corollary in that people who do take steps to protect their privacy may be assumed by the government to be up to no good, even though there are many reasons for guarding one’s personal information that have nothing to do with any form of criminality, let alone terrorism.
And in fact, that is what is happening.
Dan Goodin writes that the latest NSA revelations released on Thursday about what the NSA is allowed and not allowed to do say that if you use PGP or Tor other encryption devices to ensure the privacy of your electronic data or communications, that fact alone may result in you being especially targeted by the NSA for surveillance.
Using online anonymity services such as Tor or sending encrypted e-mail and instant messages are grounds for US-based communications to be retained by the National Security Agency even when they’re collected inadvertently, according to a secret government document published Thursday.
The document, titled Minimization Procedures Used by the National Security Agency in Connection with Acquisitions of Foreign Intelligence, is the latest bombshell leak to be dropped by UK-based newspaper The Guardian. It and a second, top-secret document detail the circumstances in which data collected on US persons under foreign intelligence authority must be destroyed or can be retained. The memos outline procedures NSA analysts must follow to ensure they stay within the mandate of minimizing data collected on US citizens and residents.
While the documents make clear that data collection and interception must cease immediately once it’s determined a target is within the US, they still provide analysts with a fair amount of leeway. And that leeway seems to work to the disadvantage of people who take steps to protect their Internet communications from prying eyes.
…
Supporters of the recently exposed NSA surveillance program have frequently argued that it is narrowly tailored so that it doesn’t track the communications of ordinary US citizens and residents. Rules requiring inadvertently collected US communications to be destroyed once the error is discovered would appear to be key in supporting that view. The exceptions to that requirement may give critics new ammunition. Tor is a staple of many human rights advocates who want to prevent repressive governments from tracking their location or intercepting and reading their e-mail and instant messages. Encrypted e-mail, while by no means easy to use, remains a core practice among lawyers, corporate executives, and privacy advocates.It’s hard to read the documents and not be struck by the irony that use of these services may subject people on US soil to a much higher likelihood that their communications will be retained by an agency that’s supposed to focus on foreign targets.
Meanwhile, Mark Masnik writes about a ruling by the 9th Circuit Court of Appeals that says that the constitution’s Fourth Amendment protections against “unreasonable searches and seizures” restricts the overwhelming power given to government agencies to search and seize one’s possessions even at the border.
In a somewhat surprising 9th Circuit ruling (en banc, or in front of the entire set of judges), the court ruled that the 4th Amendment does apply at the border, that agents do need to recognize there’s an expectation of privacy, and cannot do a search without reason. Furthermore, they noted that merely encrypting a file with a password is not enough to trigger suspicion.
While the NSA restrictions and these small legal victories in favor of individual rights are encouraging, they only mean something if the government believes in the rule of law so that we can expect that it stays within the bounds of even these loose restrictions. But since 9/11 we have entered a phase in which we now clearly have governments that believe that they can do anything at all in secret, irrespective of the law and the constitution, as long as they can claim that they are doing it to ‘protect the homeland’ or ‘fight terrorism’ and that we have no right to ask for evidence or even to be given the reasoning behind the government’s actions. We just have to trust them implicitly. So it would not surprise me in the least to find that government secretly violates even its own stated restrictions and court rulings.

One thing to like about “nothing to hide, nothing to fear” is that it works both ways. A government that has nothing to hide has nothing to fear from it’s citizens. This way around it is actually a good thing. Liberty instead of tyranny. What a government does when it is found out by its citizens is a watershed moment. Do they get back in line or to they double down?
But in a democracy, I wonder where the responsibility lies. Is it primarily with the government, which needs to behave, or with the citizens, who need to make it behave?
“If you have nothing to hide, you have nothing to worry about.” This was the justification for the many domestic spying programs in the Soviet Union. It remains the justification for similar programs in China, Singapore, Iran and other countries.
It scares the shit out of me that, after my parents and grandparents fought to end totalitarianism, my own generation is working hard to bring it all back and more.
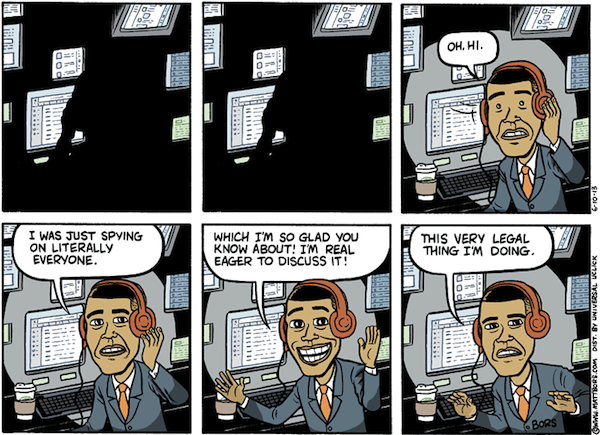
This DailyKos cartoon is not exactly intended to be funny, and it’s probably less funny if people who walk past you on the street might racially profile you. It is relevant to the topic today.
http://www.dailykos.com/story/2013/06/27/1218692/-Chagrin-Falls-Gavin-has-nothing-to-hide-from-the-NSA
What these revelations tell us is -- most importantly -- that the government does not respect “rule of law” at all; it is something to be bent, stretched on the rack, or broken outright. US society has become one in which there are two truths: one for the party, one for the people.
When people claim that they are ok with corporate and government snooping since they “have nothing to hide,” my response to them is: “If you have nothing to hide, then why do you have curtains on your bedroom windows?”