Alexa is the name given to the voice that responds to your commands on the Amazon Echo device. In a recent post, I discussed the creepiness of having someone potentially listen to every conversation in its vicinity. As I understand it (not having one) the device is only supposed to be activated if you first say “Alexa” but apparently that is not the case.
A family in Portland, Oregon reports that an Amazon Alexa device recorded a private conversation and randomly sent it to a contact in Seattle.
Danielle, who declined to provide her last name, told KIRO-TV that the contact called her family to tell them that their privacy was being compromised.
“‘Unplug your Alexa devices right now,'” the unnamed individual reportedly said. “‘You’re being hacked.'”
“We unplugged all of them and he proceeded to tell us that he had received audio files of recordings from inside our house,” Danielle said. “At first, my husband was, like, ‘No, you didn’t!’ And the (recipient of the message) said, ‘You sat there talking about hardwood floors.’
And we said, ‘Oh gosh, you really did hear us.'”
On her new show The Break Michelle Wolf had an ad for the latest feature on the Echo.
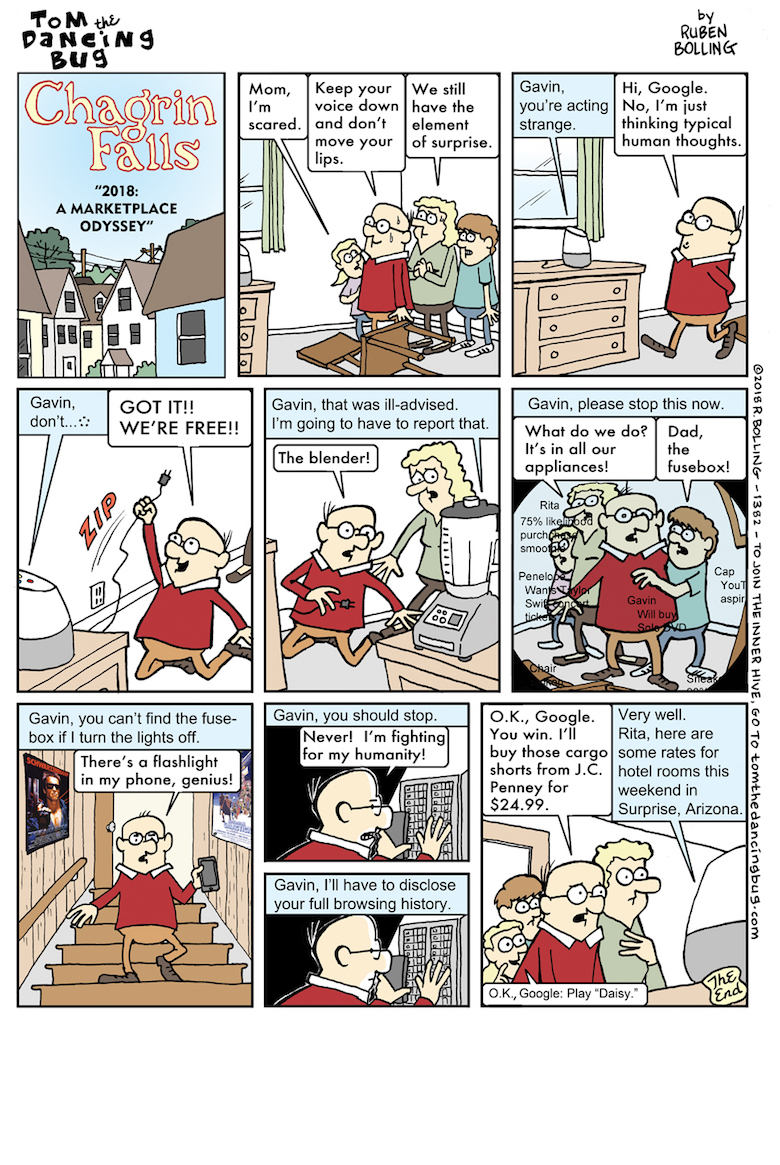
Cartoonist Ruben Bolling already warned us where this would lead.

Well, since it has to listen for someone to say “Alexa” then it has to listen all the time to everything.
I wonder how it’s implemented? Presumably they’re doing something like a local transform and rough matching and, if it can’t be made out, then the transformed version gets shipped to neural networks in the cloud… “What could possibly go wrong?” Well, if that is what they are doing, it’ now “Amazon’s data at rest” and the way the FBI likes to interpret your privacy rights, it’s probably ripe for the plucking with a national security letter.
All this stuff is obvious. I’m surprised that anyone is surprised. George Orwell called it the “telescreen” in 1984.
It’s relatively well known that many (most?) smartphones already listen to everything you say, and transmit it to your provider’s cloud, to sell to advertisers. Even when your phone is turned off, many phones are still capable of listening and transmitting. Thy only reliable method is to take out the battery (and many phones make that physically impossible -- it’s just a coincidence, I’m sure).
In related news, this is why we need to support initiatives like the libreboot project, and laws to open-source our hardware and firmware.
https://libreboot.org/faq.html
I guess that Marcus will probably say that it’s a losing battle for the end-user, and he’s probably right, but I still prefer to act like the eternal optimist and try to do something.
It’s not a losing battle. The battle was lost around 2002.
Touche.
The phone hasn’t got enough processing power, battery, or data allowance to transmit evrything to the cloud. It listens to everything looking for a trigger phrase, activates itself for a proper trigger phrase check (and possibly a voice print match), then considers whether to fully power up to record what you say, code it, transmit it, wait for a response from the servers as to the meaning of what you said, and then carry out some actions.
The net effect is that it listens to everything, but ignores most of it.
For people like the NSA who follow high-level targets, their very difficult challenge is to get recording capability out of a phone without betraying it by using up all the battery, transmitting too much information, etc.
With an Alexa-type device, many such restrictions are lifted: you have loads of power and local processing. Hacking one is going to be easier. You have few or no restrictions on uploading data to the cloud. Making it trigger unnecessarily and recording what it transmits or getting that from the receiving servers becomes a much simpler job.
I wouldn’t be surprised if GCHQ recruits are given this sort of challenge as an entry test, and anyone who hasn’t finished by lunchtime is sent home.
Except that Orwell didn’t realise that people would volunteer to have the damn things installed, and pay for the privilege too.
I generally turn off any sort of listening that I can. There are limits to this as its just a config option in most cases. I have to blindly trust that its being handled as I ask.
There is one class of voice activated device I do talk to however. The build quality can be shoddy at times which is somewhat tragic. Too bad because they have a pretty interesting operating system with remarkable pattern recognition and pathing capabilities. They seem to be very low maintenance overall but do require frequent verbal input. I often misplace them but they seem to turn up again at some point. Mostly I refer to them as “friends”. I dont see the point of any other voice activated devices.
To EigenSprocketUK
Note that on many modern smartphones, they come with two CPUs, the application CPU and the radio CPU. The radio CPU has access to the battery, microphone, and radio functionality. It can record, codec compress, and transmit, all without the assistance or even knowledge of the application chip. For many(?), the application chip can be completely powered down, and the radio chip can do all of these nefarious things. I’m sure that there are other reason (wink) why the radio chip, with its closed-source operating system / firmware, often does the voice compression codec compression instead of the application chip, but it’s very convenient that it does for the snoopers.
I agree for power reasons, it doesn’t transmit everything that it can record.
However, you implied that the smartphone needs to power up the application chip to send recordings over the radio, and that is generally wrong. Your phone can appear entirely off, but as long as the battery is plugged in, it can be recording, compressing, and transmitting.
Good point, EnlightenmentLiberal. Hadn’t thought of a hack that just transmits cellular without involving Internet connections and data quotas etc. Allowing the radio chip direct access to the mic and speakers seems a poor design shortcut to me, but then I’m not a phone designer.
I think that Apple’s phones have a separate audio chip for codecs (which do have access to mic+speakers), and the radio chip does all the RF coding and symbol / phase-shift encoding, so I’m guessing that iPhones might require a very difficult system-wide hack not just a single-chip breach. (Wouldn’t surprise me if the NSA has managed it, though.)
To EigenSprocketUK
I don’t know the specifics of iphone hardware. However, my understanding for most phones, and I doubt iphone is an exception, is that the radio chip runs its own proprietary, closed-source operating system, and the hardware makes it so that the radio chip can do whatever it wants, and the application chip is a slave to the radio chip. Even if the compression codecs were on a third chip, it seems likely that the radio chip could power it on, use it, all while keeping the application chip and the screen turned off and leaving the user none-the-wiser.
Marcus could tell you about stories where at a hacker conference, someone in a presentation, in realtime, used a radio transmitter to hack into the proprietary OS on the radio chip by using a bug in that code, and use that to do a memory dump of the application chip OS, and used that to inject a root bash shell, all via the radio, and all without the user being able to notice. Of course, this required prior knowledge and prep regarding the particular vulnerability in that particular radio chip code, and so this exploit is not applicable to all phones. However, I wonder how many phones in the real world are running the same radio firmware, or firmware that inherits the same bug. Scary.
EnlightenmentLiberal@#10:
Of course, this required prior knowledge and prep regarding the particular vulnerability in that particular radio chip code
The bug was in the software in the antenna controller. Nowadays that’s all integrated together onto a single chip, and (as you say) it has its own runtime -- I don’t know if we can call it an “operating system” because it’s basically just a ‘do … while’ loop. However, it’s able to do direct memory access (DMA) across the bus so it can get/put data to/from the CPU. Once you’ve found a vulnerability in the controller chip, the first thing you do is write a stub that dumps the entire system memory, exploit the vulnerability with that, and you’ve got the entire system image including the running kernel. Check a couple of phones and notice that the kernel is Linux, and that it’s loading the process table in the same place, and you can actually create a process running as ‘root’ from outside the kernel. It’s spooky stuff.
The Intel Management Engine (IME)
backdoorvulnerability is particularly interesting. There’s a separate region of silicon on the CPU, which is running a version of the Minix kernel and that includes an IP stack and a web server and all of it is full of great big security holes. My bet, if I had to make one, is that it was some dumbass at Intel’s idea of a good idea, not the NSA being sneaky. Unless the NSA has gotten so sneaky that they hide their attacks by making them look like normal incompetence.Marcus, thanks for the clarifications and additional information.
Amazon is the CIA.
I get called a luddite, an old fogey, and stuck in the last century. Still don’t have any kind of mobile device or Alexa or google devices. I have a landline that no one ever calls me on, and this pc. I don’t bank online so let them hack this thing. They wont get anything but my throw away yahoo email addy.