A Supervisory Special Agent is a Big Deal in the Secret Service. And SSA Jack Lewis was a Big Deal.
Jack crops up as a character in Bruce Sterling’s The Hacker Crackdown, [pdf] – Lewis was part of Operation Sundevil, which was a massive steaming chafing tray full of eggs that the US Secret Service threw in its own face. [wik] After that faceful of eggs, the Secret Service sat back, thought about it a while, and looked for more eggs. At that time I was more concerned with what other people were up to, so I had a better picture of the world around me; I was not as well-connected then but I was better positioned to observe and I still cared.
When I was a pre-sales support consultant at Digital, I wound up becoming a used equipment reseller of sorts. In the 80s big vendors were constantly trying to position themselves as the preferred platform at significant customers. The game was about displacing HP, or Sun, or Silicon Graphics – win the entire business and then cash huge checks once you’ve got them locked in to your platform. Sales reps had a lot of leeway to make deals and one of the weirder, more pernicious ones, was when Vendor A would go to a customer and say “If you buy our stuff, we’ll pay you for your old gear you bought from Vendor B.” This was a corrupt practice, in those days, though I didn’t know it at first – there was no control on the customer’s side and frequently the customer point of contact would pocket the money. It was a bribe, and for some deals it amounted to huge dollar amounts.
A sales rep might pass $100,000 to the customer point of contact at some company, and the company would decommission a bunch of systems and buy a bunch of new systems from Digital (or whoever). The decommissioned systems would wind up in the back of the sales guy’s van, or a warehouse, on their way to a computer recycler or a dumpster. One of the sales guys I worked with, one day, said, “Hey Marcus? I have a bunch of Sun workstations to get rid of, would you like them?” Would I, what? I had just spent the last six years of my life as a systems manager for Sun workstations and I knew the platform inside and out. Suddenly I had a couple car-loads of them. Another sales rep gave me a small load of Digital workstations – DECSystem 2100s and 3100s. I was rolling in hardware and had a great time swapping memory and hard drives around and optimizing my systems like a hot-rodder. I picked up some pretty good spending money selling workstations to other nerds who wanted nice home systems. I also provided a couple of systems for computer gaming clubs and computer clubs; there was a gaming club in Baltimore that ran a server hosting 10-player games of Empire (Which I had ported to SunOS) with a small modem-bank. There was a computer club at University of New Mexico that was running a MUD [Multi-User Dungeon] on a DECStation 2100 that I had provided.
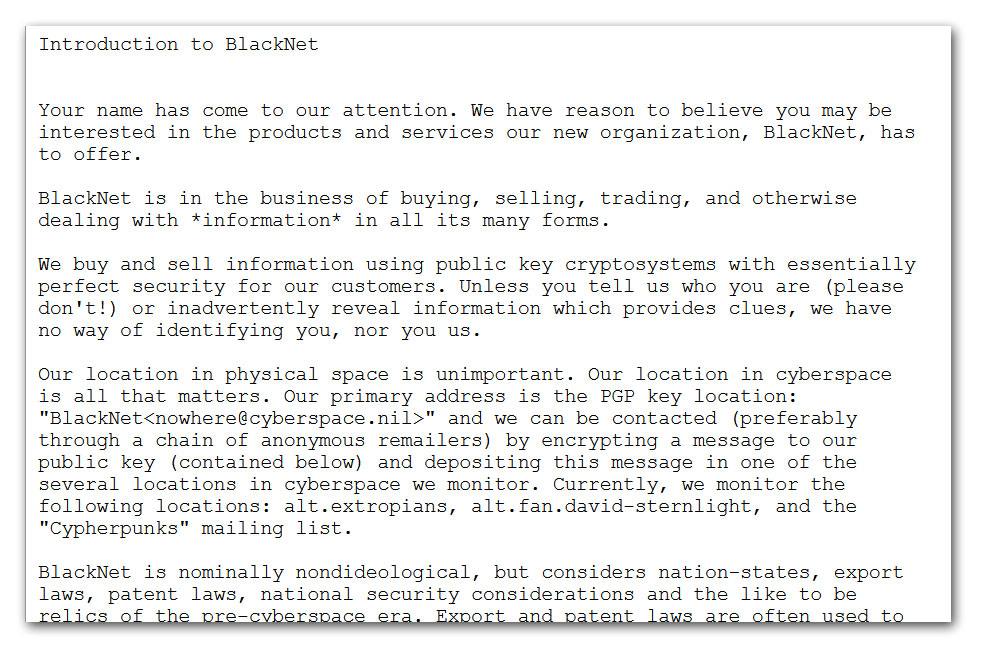
In one of my meetings at the White House, I met Jack Lewis and the experience was surreal. During the meeting, Lewis started talking about BlackNet as if it was a real thing. BlackNet was a spoof, a joke someone had posted on cypherpunks as a concept-piece of what a distopian cyberwar future might look like. In retrospect, it was pretty good. Suddenly I was in close proximity to someone who was investigating BlackNet as though it was real – someone who was, seriously, trying to eradicate this threat to US interests. Imagine if you were talking to someone and discovered that they thought Get Smart was a documentary. Given that the Secret Service had, in Operation Sundevil, mistaken Steve Jackson Games’ game Illuminati for an actual online cyber-conspiracy, I thought there was a real danger that they would try to identify whoever was behind BlackNet (a guy named Tim May) and do a Waco, TX, maneuver on them.
After the meeting I sidled over to talk to Lewis, with a vague notion of trying to tell him that BlackNet was a will ‘o wisp, but he immediately took control of the conversation, “Have you ever heard of Kevin Mitnick?” Well, yes, I had. Mitnick had caused some problems at Digital by getting into our network and wandering about, apparently trying to get access to the VAX/VMS source code. There was some bad blood, there, because Mitnick’s actions had resulted in some systems people at Digital getting in trouble for not having adequate security. It was, in fact, partly because of Mitnick’s actions that I got sucked into network security and was assigned to implement a better firewall for Digital. I have never thanked him.
I told Lewis that I’d heard of Mitnick and then he asked me, “have you ever heard of a system called ‘moink.nmsu.edu‘?”
By this time I was getting tired of Supervisory Special Agent Lewis – he was, literally, throwing his weight around and I had begun to realize that he had no idea what he was doing.* So I cooly raised an eyebrow and replied, “know it? I own it.”
See, moink.nmsu.edu was the DECStation 2100 I had donated for the computer club at New Mexico State University to run a MUD on. I had configured the system, built and installed the MUD, and shipped it out a year or so before then. I had completely forgotten the system existed until Jack Lewis asked me about it. I’m not sure if I actually owned the system, anymore, since I had donated it to the computer club, but I thought it was arguable. More importantly, I was the system administrator of record and I still had the administrator’s password.
Jack Lewis got very excited at that point, and asked a lot of questions, which ended with him winding up a pitch that giving the US Secret Service authorized access to the system would be a good deed for America, and patriotic as all get-out. That evening I went home and (in my role as system administrator of record) I ran a remote dump from that system, over the internet, and produced a .tar file of everything that was on it. I FEDexed the tape down to Jack Lewis and more or less forgot about the incident until the year after when Kevin Mitnick tangled with Tsutomu Shimomura in a sequence of events documented in John Markoff’s book Takedown [wc] – Mitnick used a TCP sequence-guessing attack that was very advanced for its day, and there was considerable excitement. When that happened, I was at a conference called CMAD2 (Computer Misuse and Anomaly Detection) out in Sonoma, soaking in a hot tub with Bill Cheswick and kicking around ideas for a start-up that later became Network Flight Recorder, Inc. I went back to my room and logged into moink.nmsu.edu again (password still worked!) and poked around a bit. It turned out that Mitnick had been using that system as a place to chat with a few other hackers, including a young Israeli hacker who went by the handle ‘jsz’ (“Henri De Valois” was his login name, which still makes me laugh) jsz was developing the techniques and feeding them to Mitnick who, judging by his emails with jsz, really didn’t understand TCP/IP, or security, or UNIX, or much of anything.
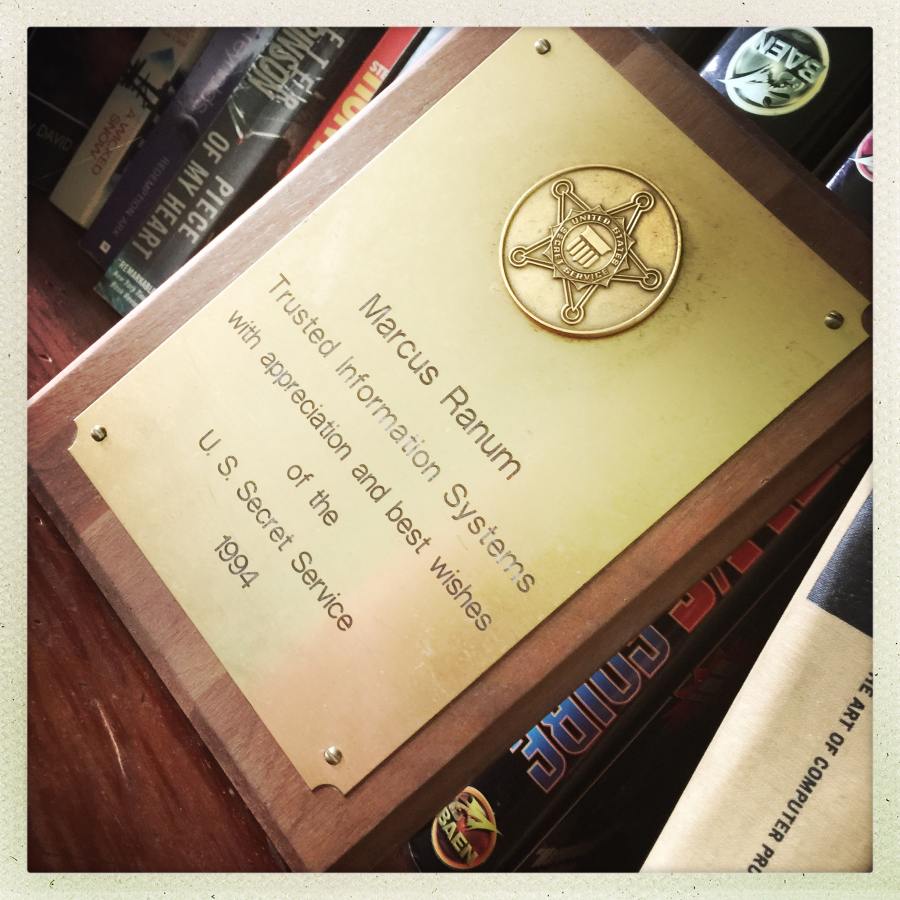
That situation blew up into national news, which resulted in Kevin Mitnick going to jail for a little while, mostly because his operational security was piss-poor. But I got the pleasure of calling Jack Lewis up, again, and asking him if he wanted copies of Mitnick’s sequence spoofing tool and the online identity of the author. After that conversation, I never talked to Lewis again, but a couple of months later there was an official-looking FEDEX document box on my doorstep from the US Secret Service. By then, I had decided that it was impossible to tell which direction things would bounce with Jack Lewis and I immediately imagined the box contained orders to turn myself in, or something like that.
It did not:

The complete BlackNet piece: [bn]
* If you read Sterling’s book, you’ll get a much stronger impression that Jack Lewis had no idea what he was doing.

Now that you’ve told us the story, do you have to kill us?
OMG you saved America from BlackNet! We are not worthy etc.!
That is pretty hilarious. On the other hand it’s also kinda scary. Those SSA dudes have some serious resources to throw around at imaginary/otherwise enemies.
The Big Hack: How China Used a Tiny Chip to Infiltrate U.S. Companies
PZ has already posted about this article, which seems to be denied by every named entity other than Bloomberg, and he does not have any credible expertise. Maybe you’d like to take a crack.
kestrel@#2:
I think what was going on was the early stage of running up hackers as a great big scary threat. The cold war had paused and the spooks were afraid of budget cuts – the hackers generously stepped up and offered to be the new shibboleth. Now, if you look, hacking is equated with terrorism as a huge threat, which allowed them to rewrite the rules of engagement. In its own silly way, BlackNet was part of that.
Reginald Selkirk@#3:
Interesting.
Ok, I’ll post some things about that.
The short story is that the Chinese appear to have backdoor’d the part of the supply chain that they could without causing massive damage. Intel has backdoored the CPUs and the crypto and network interfaces have been backdoored by NSA. CIA has backdoored the operating environments and FBI has backdoored the businesses that run the systems. The GRU has backdoored the CIA and NSA and the Mossad has backdoored the GRU.
That is not a joke. I guess I’ll have to do a posting on this with a link-farm of references. The current state of affairs is really, really, shit-smeared.
Speaking of national cyber security, what does our esteemed host think of “a href=”https://www.forbes.com/sites/arthurherman/2018/09/24/a-national-cybersecurity-strategy-better-late-than-never/”>America’s first comprehensive National Cybersecurity Strategy in fifteen years“?
Oops – who know that putting quotes around a link would render it a non-link? Not me!
Hmmm – not losing that 1st angle-bracket might’ve helped too…
Re: Marcus @ #5:
I am a back door man
I am a back door man
Well, the men don’t know
But the little girls understand
When everybody’s sound asleep
I’m somewhere making my midnight creep
Yes, in the morning, the rooster crow
Something tell me, I got to go
I am a back door man
I am a back door man
Well, the men don’t know
But little girls understand
I’ll hazard a guess that there is no rank above “Supervisory Special Agent” for the simple reason that the resulting title would never fit on a business card. And before anyone gets hung up on the “secret” bit of “secret service”, why give anyone a title like that if they can’t introduce themselves with it?
—
Re: Marcus Ranum (#5):
Maybe an essential step towards transparency, freedom and democracy is to oblivionise* all security everywhere. Then all you have to do is cross your fingers and wish really hard that noone exploits the situation. Although a world where MAD is considered a sensible strategy and trolls roam the internet is probably the wrong place for that kind of optimism.
*If you can’t think of a word, make one up.
You are a character out of the sf I was reading in the eighties AICMFP.
That was what I took from descriptions of his exploits too: very little technical acumen but a lot of chutzpah and a knack for “social engineering”, and the ability to keep hammering away at a problem when a better-adjusted person with a more developed sense of self-preservation might have given up and walked away…