I’m usually surprised by the coverage regarding NSA/CIA/FBI spying: there’s some stuff we definitely should be scared of, and there’s other stuff that I file under “so, what?”
For example, the fact that the US government has consistently ignored its own laws regarding wiretapping: nobody who has observed any government in action should be surprised by that.
For example, Herbert Yardley published “The American Black Chamber” [archive] in 1931, documenting a slightly fictionalized version of his exploits monitoring communications during WWI, before, and after.
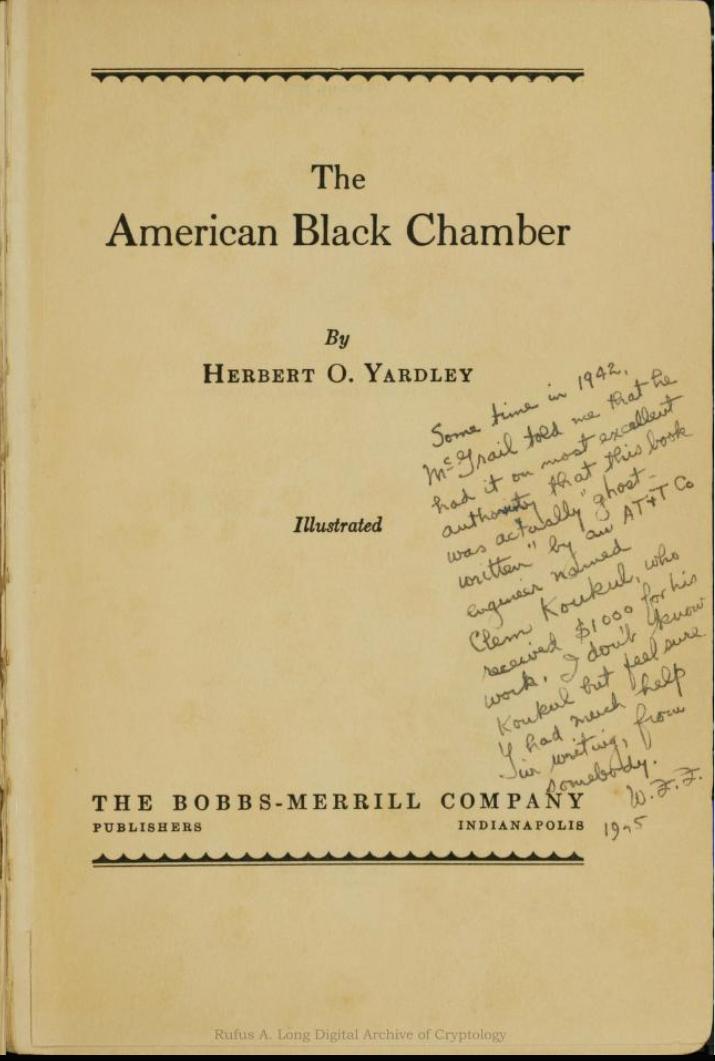
The annotations are by William Friedman, the inventor of mathematical cryptography(!)
At the time Secretary of State Stimson said (1929) “Gentlemen do not read eachother’s mail” it was a lie; he didn’t consider the Germans to be “Gentlemen” and was only referring to not reading friendly diplomatic communications. Given the way spies think, I am pretty sure I know how the US determined which diplomatic communications were or weren’t friendly: they read them.
AT&T was a new thing, and telegraphy immediately became important. And the US government (various agencies) immediately moved to tap and compromise it. When voice telephony took over, the newly-minted FBI began doing exactly what the NSA, FBI, and CIA are doing today: tapping it. And they began building call records of who called who, and when.

My pen register. Ebay is fun.
That’s a vintage phone call recording device. It comes in a lovely wooden box to dampen the sound of the solenoid, as it made marks on the paper with the pulse of the ringer. The connections on the lower right match a hole in the case where the wires could go in, and the tape went out a slit in the other side. By the way, it’s really heavy – solid brass with a great big wound spring inside.
The FBI used those for a while; there’s still a lot of law on the books regarding pen registers – the initial idea was that the number you called was “just metadata”[stderr] and there was this fig-leaf game they played of pretending that the number was all that was being recorded, while, actually, they’d tap a line pretty much whenever and however they wanted to. COINTELPRO blew the doors off of that, but the American people rolled back over and went to sleep; it really doesn’t matter what you monitor, as long as you don’t try to bust everyone for the little stuff like drugs and extramarital affairs and that sort of thing. We need to be honest with ourselves – we’ve known this has always been going on and always will be: the only people who have privacy in the US are the oligarchs.
Then you have the 90s’ and AT&T whistleblowers coming out and describing the secret room(s) at phone company locations, where internet peering points were tapped. But nobody cared because the establishment told some story about “metadata” to the media and the media pretended to buy it and it really didn’t matter because, aside from a few dirtbags who needed to get busted, and the occasional political hatchet-job [stderr] it really didn’t interfere with anyone’s lives. The silk road was a thing in the early oughts, and you could buy drugs online, and child porn, and – the FBI can always excuse anything if it busts some child porn. Nobody should be shocked to find out that the government has continued its uninterrupted policy of ignoring the constitutional protections against self-incrimination or search. Nobody even cares when the FBI regularly and openly cheats in how it collects evidence by digging where it has learned there is other evidence, illegally. That process is called “parallel construction” [wikipedia] and it’s been a practice for a very long time. In the early days it was a confidential informant mentioning “the gun that was used might be in the toolbox in the garage” and now it’s “a text message that was collected without a warrant” – it’s all OK as long as there’s a warrant when the FBI agent searches the toolbox, and “oh! Look! I stumbled on a gun!” right?
I’m not saying we shouldn’t care – I hate that “so what? This is nothing new!” argument. The reason I hate it is because it’s not saying “don’t worry about government surveillance because they’ve always been doing surveillance to some degree or another” – I hate it because it’s saying “you woke up and found you’re in a police state and have always been in a police state and you’ve never had a ghost of a chance of doing anything about it.”
That’s the core message, to me, behind the CIA dumps and the Snowden dumps: we have collectively tried to do something to secure our communications but we never even had a ghost of a chance against our own government because – simply enough – they never were even going to give us that much. We used encryption because we wanted our communications to be private. Otherwise, we’d have left them public, right? The observation that we tried to speak privately argues that we have an expectation of privacy. If we were going to be allowed it, that is. Which, we’re not.
When the FBI complains (as they did consistently through the 90s!) that “encryption is making the internet go dark”[fbi] they were lying: they just wanted to pass CALEA[wikipedia] and force providers to give them obvious back doors, or the Clipper Chip,[wikipedia] which would obviously backdoor everyone’s crypto. That was just them asking nicely. But they not only never had to ask nicely, they made sure they had parallel backdoors so that even if we struggled to secure our communications by switching to Signal (or whatever) they could just go around it. In fact, using PGP – as some of us used to – probably flagged you higher in Xkeyscore because you were attempting to do secure communications and, well, we can’t have that.
I’ve written elsewhere about the retro-scope:[stderr] law enforcement’s ability to go back in time and decide retroactively who might be a trouble-maker, then to retroactively strip-mine their communications. That strip-mining? That’s what the CIA and NSA and FBI’s fancy tools are for. They’re not using it to stop billionaire child molesters like Jeffrey Epstein: they’re using them to analyze the communications and activities of people who annoy billionaires.
The FBI is currently trying to push for warranted access to #NODAPL Facebook group’s membership and communications. The ACLU is bravely trying to fight this battle which has already been lost: the NSA already has that data, and now it’s sharing it “before privacy protections” (whatever that means) with other federal agencies. That means the FBI is just hand-wringing for the camera; they’re already investigating all the friends of friends of #NODAPL and people who said “I’m going” and if you just purchased a large amount of ammunition or a high capacity weapon, they’re going to be looking at your credit card purchases and see if you’re making “card present” transactions heading toward North Dakota.
The ACLU filed a motion in Whatcom County Superior Court on Wednesday to block a police warrant to search the Bellingham NoDAPL Coalition’s Facebook page. A hearing is scheduled for Tuesday morning. According to the ACLU, the Whatcom County Sheriff’s Department served Facebook with a warrant seeking data on not just the NoDAPL protesters themselves, but on people who merely interacted with the Facebook group. [ars]
The name of the game is not even collection, anymore. It’s integration and fusion. It’s tools like Palantir and Xkeyscore. The problem they have is not that they don’t have access to your data: it’s that they have all the data and it’s really hard to figure out who’s worth looking at more closely. There’s too much data. But, like when the lidless eye of Sauron turns upon you, once you become a target, your protections: your iPhone, your Signal, your Facebook, your complicated password – it’s not worth anything. The only thing that gives you a chance of staying off the radar screen is good tradecraft. Or being a billionaire. Or not giving a fuck. Those are, seriously, your three choices.

The NSA’s data center in Utah. And look, a national guard armory to defend it.
Right now there are vast fortunes being made on “big data” – data fusion, data integration. What do you think that’s for? The basic stuff is in-house: amazon notices that you buy one weird product, and it offers you a list of others that other people have bought. The other stuff: that’s not looking for “terrorism” that’s looking for potential cells of revolutionaries forming, so that – when they need to – if they need to – they can ask some database: “how many people who went to Standing Rock also swapped emails with people who were in Seattle making credit card purchases during the globalization protestsriots?” Then refine that by weapons purchases: Oh, look, Marcus Ranum bought a dozen israeli-made gas masks on amazon.com and had them shipped to Standing Rock: put him on a watch-list and yellow-flag anyone who communicates with him who also buys explosives precursors.
I’m not writing about that like that’s the horrible future we’re doomed to if we don’t do something. That’s the horrible present we’re living in already, because – unfortunately – a lot of politically naive nerds (my peers!) designed the systems that are going to be their own shackles, because they’re hoping they’ll make enough money to be on the fringe of the minor oligarchs’ club, and they’ll be passed over and someone else who can’t afford a good lawyer (or who has the wrong skin color or name, or isn’t a citizen) is going to get investigated. This is our current reality.
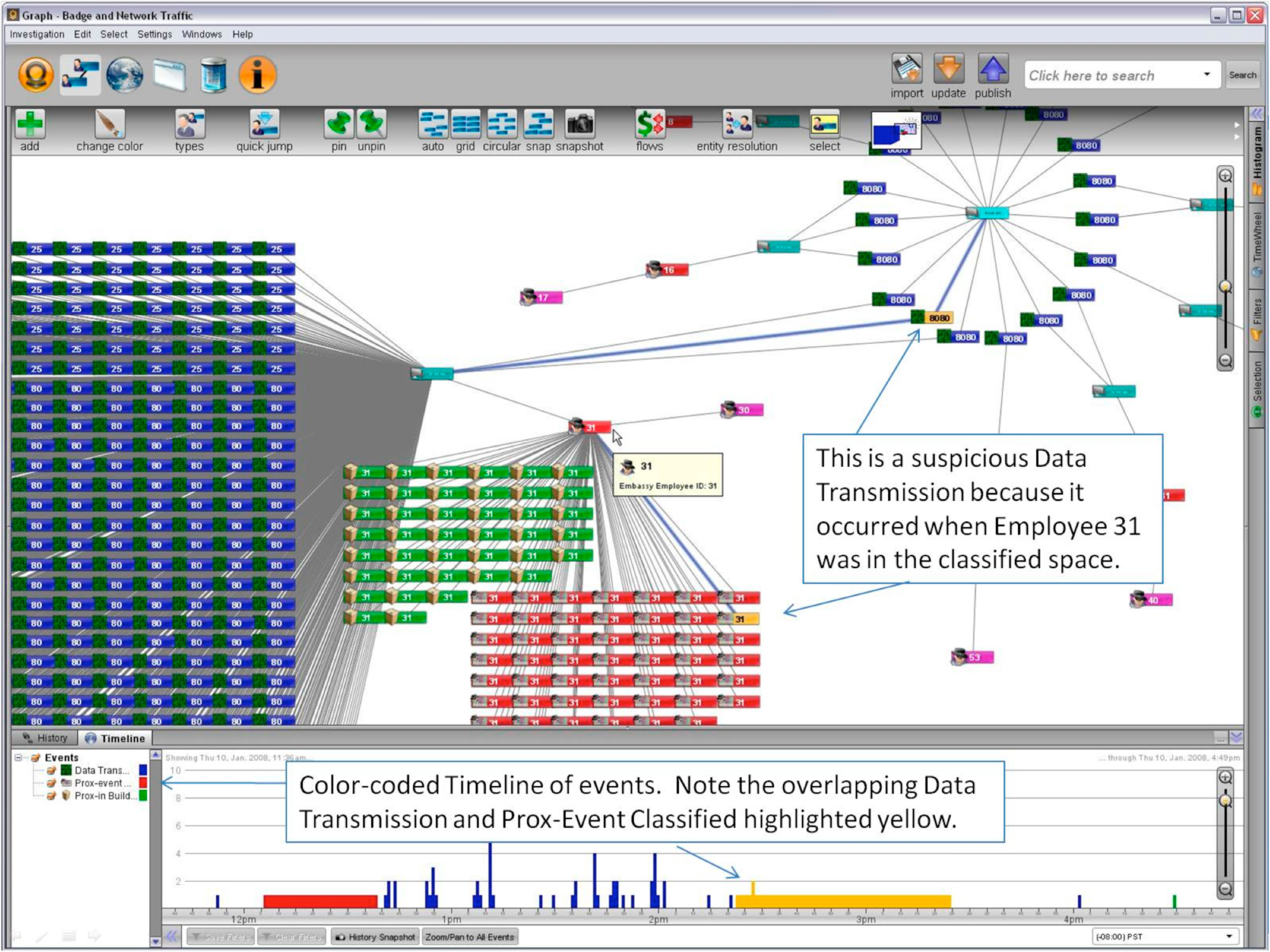
Palantir User Interface
I live in gun-toting 2nd amendment worshipping rural America; everyone out here would probably vote to oppose some kind of additional registration requirement on guns. What they don’t realize is that that additional registration happened silently and organically about a decade ago. They don’t realize that UPS and Fedex are required to share “metadata” and so are banks and credit card companies. What “metadata” is that? All of it. You want to know who’s buying ammo? Ask the UPS shipping database who got ORM-D packages weighing over 10lb from (long list of websites) and paid more than $50 for it. And that’s assuming that the site you bought that ammo from doesn’t have a National Security Letter from the FBI asking for their customer database and purchase records. The rigamarole about registration laws and no federal databases: that’s just stage-management for the rubes who don’t understand the kind of triggers you can build when you combine shipping flags, package weight, sender/recipient, with purchase history and website classification. Do people really think that the USPS added all that computerized tracking stuff in order to make their customers’ experience better? (Well, yes, they did, but who are their “customers”?) This is what I meant about having good tradecraft: it’s not enough to be able to assemble your conspiracy in secret, because they can go back and catch you for mistakes you made before you decided to start the conspiracy at all.
The Intercept has a story about Palantir [intercept] that’s worth a read. But I see it as sort of deceptive because it misses the point: Palantir is not particularly useful unless it has a gigantic, huge, dataset behind it. A tool for analyzing and building networks of relationships based on tenuous data (like, “thin thread”s – get it?) – that’s a job for AI but the real story is the depth and detail of the dataset. The threat is not Palantir, the threat is big data and that threat materialized a decade ago. Every private corporate dataset is potentially not private against the police state: remember, when the American of Japanese ancestry were detained in concentration camps during WWII: they were rounded up based on census data that was supposedly gathered for, well, purposes other than rounding people up and putting them in concentration camps. Palantir isn’t the problem, it’s your ebay history, your amazon history, your Facebook friends list, and all of those have been winnowed through and the interesting bits have been flagged and sorted and attached to your master database record.
Consider this story: [guardian]
A New York woman says her family’s interest in the purchase of pressure cookers and backpacks led to a home visit by six police investigators demanding information about her job, her husband’s ancestry and the preparation of quinoa.
Michele Catalano, who lives in Long Island, New York, said her web searches for pressure cookers, her husband’s hunt for backpacks and her “news junkie” son’s craving for information on the Boston bombings had combined somewhere in the internet ether to create a “perfect storm of terrorism profiling”.
“Quinoa” is code for something horrible, I’m sure. But how did this happen: “had combined somewhere in the internet ether” No, that was an example of an over-broad rule some analyst did a fishing expedition on. Someone was looking at a Palantir console and it detected a bunch of matching terms between over here and over there and drew a bright red line. So six police investigators showed up at someone’s door asking about her husband’s ancestry.
The police and the national police serve the establishment: the rich, the powerful, the corporations (in that order) As the US heads toward ever-increasing spiral of inequality and unrest, they’ve already chosen which side they’re on: they’re already buying increasingly militarized technology and establishing the long-term databases that will allow them to decide who to round up and when. It’s not happening now, but we’re actually at a point where the government is investigating people because of who people they know swap Facebook messages with. Let that sink in.
The situation is vastly worse than most of us realize. It’s probably worse than I can imagine. Your Xkeyscore probably went up a tiny amount just for reading my blog. But you may as well stick around, it’s already too late.

Back in the late 80s/early 90s some people used to put “NSA fodder” .signature lines on their USENET postings. I did that, myself, but intermittently (because if you do it always, it’s really easy to filter) The fancy tools like Palantir – those were written as a response to the incredible new complexity in the info-sphere: not because it’s harder to find stuff it’s because there’s so much more to find.
I just want to circle back and encourage you to think a bit about “parallel construction.” If you have any idea that there’s a rule of law, trial by evidence and a jury of peers, that should cure you. Because the idea of presenting evidence in court is so that the defense can challenge it and part of the challenge is whether it was lawfully obtained. The government admits that its premier law enforcement agency regularly manipulates how it gathers evidence, in order to protect the secrecy of how it illegally surveils its targets. This is not a new thing: this is how it has been done since the 70s (and probably sooner). That stuff about “rule of law”? They’re referring to the golden rule, baby: that’s the only rule that’s respected.
Privacy for the oligarchs: The President can have Marilyn Monroe or Monica Lewinsky or Kay Summersby or whoever in the Oval Office for a tryst and they never show up on the activity logs kept by the massive staff. The staff that knows where the oligarch is every minute of every day. And the other oligarchs are safe because, hey, as long as there’s no political hay to be made, who cares if Bill Clinton flies on Jeffrey Epstein’s mobile teenfuck palace?[1] It is a gigantic 727 flying around controlled airspace and people get into and out of it through airport security. Yes, there are surveillance camera frames galore of young girls getting on and off that plane. Of course all that stuff is recorded and monitored; the establishment just ignores it. Unless you annoy The President like Khizr Khan. Of course, this is how history has always been: the powerful are the only people who have any right to privacy. Peasants have whatever anonymity they get because they don’t matter. Any of us who think we have any privacy: we’re peasants.
My quip about “thin threads” above: I’m referring to Binney’s analysis engine for NSA “thin thread”[wikipedia] which was, basically, Palantir without a pretty programmable user interface. There are a lot of techniques for clustering information. It’s an AI problem, really, and human AIs are getting pretty good at this kind of thing. I’d be utterly shocked if there weren’t IBM salespeople falling all over themselves trying to pitch Watson to the FBI and NSA. Uh Huh:
Both the N.S.A. and the Central Intelligence Agency have been testing Watson in the last two years, said a consultant who has advised the government and asked not to be identified because he was not authorized to speak.[nyt]

The rich are the powerful, why else accumulate money? Any corporation that isn’t rich isn’t powerful.
Unless there’s a special class of poor person who has launch codes of ICBM’s that I’m not aware of…
You’ve done an Euthrypthro and used synonyms. Rich is powerful is rich.
Apart from that. I’d just like to offer my services to our overlords. As a trusted internet tool I can be useful to your purposes and have few quibbles, apart from being tortured….
Not only does this song contain the title of this post in the lyrics, it’s the perfect accompaniment to any article on the shenanigans of the US Deep State (which I’m told doesn’t exist, btw) https://www.youtube.com/watch?v=0x8mKsGQeBs
You were right, it’s much, much worse than I thought. And I don’t feel better at all.
:-( Wow. I know people who went to the incredible hassle of completely deleting their Facebook account due to a fear of this very thing. But too late I suppose. Ah well.
My PayPal account was once shut down because I bought a base for model horse showing and made the poor choice of writing the person a thank-you note for it. I have no idea why that would trigger Homeland Security; but it sure did. I had to write these long novels explaining why I would buy such a thing. Model horse showing has to be one of the most harmless hobbies on earth; you can’t even get kicked or anything.
I’m not surprised.
It’s not completely hopeless. We just need to elect a government that respects privacy rights. Programs can be shuttered, data warehouses can be shut down, the retroscope can be dismantled.
Except that (at least) 99% of voters, on all points in the political spectrum, actually oppose privacy rights. So maybe it is hopeless.
But still, massive and expensive programs can be dismantled and data can be destroyed. Ideally, we’d use the retroscope to figure out who had access to surveillance data and have them euthanized, since for an illegal spying program this extensive, proper data destruction includes copies retained in human memory.
Incidentally, why the hell hasn’t anyone ever sued to stop this nonsense? File a suit, subpoena all records any agency has collected on you, and you’re bound to find a couple that can’t squeak through any of the usual loopholes.
Should have told them to piss off.
@4:
Should have told them to piss off.
I’ve learned through experience* that when a cop accuses you of terrorist plotting, the best way to escape the situation is to tell him to piss off.
*Experience as a white person; results not typical.
The surveillance state has nothing to do with elected officials. The spooks do what they do regardless, and unless we elect people who are willing to shoot spooks for spooking they’ll continue.
And I’m pretty sure a president who shoots spooks is, in practice, a pretty bad idea.
@Jessie Harban: that’s all well and good, except that: my PayPal account would *still* be inactive, if I had done so. I run an online business and I need other people to be able to use it so they can send me money; and who knows, this might have escalated. I don’t even understand why someone would care if I bought such a thing in the first place. In the other case? Those people would most likely have been jailed. For…. something. “Resisting arrest” or something. They might even still be in jail.
I do agree that there are times when someone in our society who is relatively powerful can do such things, and I applaud them doing so and also think that if one is in the position to do so without bad consequences, one should. However, when you are not top of the heap, it just doesn’t go all that well. Alas. As I see that you noted.
re: my comment on the Deep State at #2
https://www.buzzfeed.com/alimwatkins/actual-intelligence-officials-are-laughing-at-the-deep-state?utm_term=.hlBQBAE4b#.wme20QDvp
Milo Black & Gilbert Shelton were way ahead of you back in ’94:
Government Spies
Government spies are everywhere
In your home and in your hair
Lurking in their secret lair
Counting dollars
They know everyone you know
They see everything you show
And everywhere you go
They slowly follows
Read the whole thing!
I disagree that “rich” and “powerful” are necessarily synonymous.
Rich people who lack power: Lottery winners; feckless heirs of families who have indicated that they will not work to protect the heir from the consequences of their more extreme shenanigans.
Powerful people who aren’t wealthy: Well, any that lack wealth will probably soon become wealthy. But they may be more interested in power (social and political influence) than in continually accumulating wealth. It’s at least possible for some religious person to have made a “vow” of poverty (not that they’ll ever be hungry or uncomfortable, given the followers eager to donate food and other goods and services) while nevertheless maintaining the social and political connections to influence policy in the ways that they prefer.
Owlmirror @ # 11: I disagree that “rich” and “powerful” are necessarily synonymous.
Consider the case of Jerry Falwell, Sr., who absolutely loved (getting close to) power, but neglected his financial opportunities to the point where a fellow hyperchristian gangster had to bail him out.
However, Jerry Junior has not failed to exploit the monetary opportunities his father neglected, and now has Liberty University raking in hundred$ of million$ each year while still cozying up to the political kakistocracy, so I have to doubt whether this sort of exception disproves the general pattern.
You’ve mentioned good tradecraft before and since prevention is clearly not within the realm of extant politics would you be willing to discuss further what it actually consists of?
alkaloid, not asking such questions so publicly?
My comments were flippant, trying to get a rise out of Marcus. But I’ll attempt to defend them….
Do lottery winners lack power? Or do they just not realize that they now have more power, commenusurate with their win, that enables them to do things they couldn’t do in the past? If I can now buy an island (or whatever), I’m now more powerful, no?
Feckless heirs indicating they will not use the power they have, isn’t a lack of power.
OK, so they choose not to use the financial value of their power, but they still have it. After all, they could take the rubes, I mean believers for all they’re worth. But OK, I’ll restate, power convertible into money, and for fun, assume it’s a transitive, if I’m rich, I can hire thugs to beat up my enemies, and if I have thugs I can steal my enemies money, relationship. So, power does equal wealth. ;)
D’oh! Not transitive, more an invertible function, a one-to-one bijection.
@7:
We don’t need to kill spooks, we just need to kill their budget.
State-sponsored spying is state-sponsored. Let’s see how much spying they can do without any money or government tools at their disposal.
@8:
Why was your Paypal account inactive in the first place?
@Jessie Harban: Because… I bought a base for model horse showing, they told me that was a suspicious thing to do and froze it. Then told me if I could not explain it it would be completely deleted.
.
Are you saying that if the bad guys can read half my life, then nobody should bother protecting the other half?
.
It is good to do an analysis on something but this seems like a clarion call for everyone everywhere just give up.
.
Does giving up sound like a good idea?
Owlmirror:
Money = power, full stop. Doesn’t much matter if someone doesn’t use it in the power sense, it’s still there. In the meantime, the rich and powerful are busy trying to rewrite the constitution.
multitool:
So, in fewer words, you don’t want to know. You’re also arguing in favor of ignorance, FFS.
The point of this is to inform and educate people. How, exactly, do you expect people to fight back if they don’t know what they are up against? All over the states, there are efforts being made, using these new tools, to track down anyone who has organized NoDAPL protests, in order to show up at their door, drag them out, arrest them, and charge them with felonies. Do you not fucking think this is going to have an affect on peoples’ ability to protest?
As a blogger who often rails against the current regime, I now need to be aware that a knock could come at my isolated door at anytime. FFS, this is massive, important news. How in the hell does being grounded in reality end up being tantamount with giving up? I’m not giving up, but I feel better being prepared, so at the very least, I won’t be taken unaware.
.
This seems like a good time to mention that there are alternate Internets out there, none of them owned or controlled by telecoms or governments:
http://www.motherjones.com/politics/2013/08/mesh-internet-privacy-nsa-isp
.
See their beautiful growing maps here:
https://guifi.net/ca/node/2413/view/map
http://www.pittmesh.net/
https://nycmesh.net/map/
http://www.athenswireless.net/
http://map.sudomesh.org/
https://www.freifunk-karte.de/
.
ETC.
Caine, you’ve got me totally, totally wrong.
.
Of course I want to know everything that is going on. I never argue for ignorance.
.
But the most important information to know, more important than any of this is, what are we going to do about it?
.
If the answer is ‘die’, then all the knowledge in the world will have no value inside my decomposing skull.
.
I at least attempted to show a way to fight back in my previous post (full of links, awaiting moderation).
I just realized maybe I’m not appreciating that the OP is actually news to a lot of people.
.
I work in IT, so while Marcus did a great job of filling in the details, none of it added to what I could already guess back in 2005. I gotta be more mellow about this. Yes we are in deep shit. Appreciate that I am terrified too.
.
After we’re all done being shocked, we need to bring activism to technology in a big way, and in a hurry.
multitool@#24:
I’m not appreciating that the OP is actually news to a lot of people
I think that’s right, and it’s deliberate. The way that the media make it a Big! Scandal! when the government catches itself cheating on its own rules – that allows them to appear to do something, when necessary, but really nothing happens. I believe they are becoming emboldened especially after Bush discovered that they could outright break the law in a huge number of ways (surveillance, torture, offensive cyberwar) and publicly exonerate themelves afterwards – I think they went “holy crap! we don’t even have to pretend to care anymore!” Look at what happened to Kiriakou, Binney, Klein: “ha, the public doesn’t care, they bought our story about ‘metadata’ let’s pull the other one.” And they did buy the story about metadata. And most Americans believe that China and Russia are the worldwide aggressors in ‘cyberwar’ in spite of the US obviously engaging in it, funding it, and controlling the well-heads of most of the technology that much of the world embeds.
none of it added to what I could already guess back in 2005
That was around the time I think most of us saw it coming. Yes. The pieces were there all along but, honestly, most of us thought that there were people of good intent who would come forward out of those agencies and stop this from happening. That was a really dumb bit of thinking: we should have realized that the people who are hired into those agencies are heavily pre-screened to be authoritarian followers.
we need to bring activism to technology in a big way, and in a hurry.
There are some minor efforts but many of the ones I see have already been deeply compromised before they will even get off the ground. Eventually, we’re going to need a full-on cyberinsurgency with the intent to smash it all so that it can no longer be owned by a single entity.
multitool@#22:
This seems like a good time to mention that there are alternate Internets out there, none of them owned or controlled by telecoms or governments:
True. But they’re going to run on compromised platforms, compiled with compromised compilers and linking compromised encryption, tunnelling over compromised networks. Any alternative networks will be owned from the day they become a threat. We can now, for example, be fairly sure that the NSA at least has a large number of compromised TOR egress points and probably a large enough number of inner nodes that they can map back traffic using traffic analysis. That’s just an example: when an alternative appears, it gets compromises built into the foundation. It now appears, to me, that the FBI (at least) was working hard to compromise the bitcoin infrastructure before it could develop into an uncontrollable alternative to money. Such a thing will not be allowed. Private networks will not be allowed, either, unless they are point-to-point person-to-person.
multitool@#19:
Are you saying that if the bad guys can read half my life, then nobody should bother protecting the other half?
.
It is good to do an analysis on something but this seems like a clarion call for everyone everywhere just give up.
.
Does giving up sound like a good idea?
It’s important to understand what you’re up against, and to be able to respond appropriately. One of the messages I would say I am carrying forward is: stop expecting the government to play by its own rules Those are just there as window-dressing for suckers.
If you don’t decide to give up, then it’s going to be important that we level up well past the point where we are now. Using ‘Signal’ instead of instant messenger does not equal secure communications: it equals +1 for attempting to use better comms security in Xkeyscore – you have flagged yourself as more threatening, more worthy of sending someone by to plant a bug in your computer. That’s another point that the CIA trove clearly illustrates: they have a huge arsenal of targetable access techniques – that’s what they do when you come up on the ‘radar screen’ The radar screen is huge and the attack surfaces are huge. This is not a simple matter of a bunch of analysts looking for people going to the ISIS website or saying “Allah Akbar”
Jessie Harban@#17:
We don’t need to kill spooks, we just need to kill their budget.
State-sponsored spying is state-sponsored. Let’s see how much spying they can do without any money or government tools at their disposal.
I wish I had your faith in the system. Remember the big “military budget downturn” and how that cut back the pentagon’s ability to engage in wars? Yeah. The police state has already gotten at least half of its budget onto the black books where it’s unauditable. So how do you cut that back? Especially when you have a congress that’s also in the pocket of the police state? Remember how the only upset Nancy Pelosi showed about Snowden’s fact-dump was when she discovered that the CIA also spied on the congressional staffers that were investigating them, and deleted evidence retroactively? If that’s the kind of push we have on our side, we are thoroughly fucked.
And what if everyone uses Signal, even for grocery lists? Does that help the NSA too?
I am still not hearing any strategy, only one long declaration of defeat.
alkaloid@#13:
You’ve mentioned good tradecraft before and since prevention is clearly not within the realm of extant politics would you be willing to discuss further what it actually consists of?
“Tradecraft” is spook for spook-skills. Good tradecraft is when you’re able to operate in secret, by defeating or mitigating (or sending false redirects) against whoever’s watching you. The state of the art of tradecraft in the 80s was using a one-time pad and a dead drop (e.g.: Robert Hanssen’s coke can drop) tradecraft always evolves to match your opponents’ capabilities, which means you have to threat-model pretty seriously and have a very realistic view of their capabilities versus your own. Another aspect of having good tradecraft is the consistency and professionalism with which you use it – if you’re using really good techniques but get sloppy or lazy, then your method may be good but you’re sloppy and it doesn’t matter.
In the internet era, having good tradecraft would probably entail going off the web entirely, for many types of things. And, probably, continuing to carry on a suitable cover of uninteresting use and chatter because someone who doesn’t use the web is going to stick out like a sore thumb, at a certain point. I’d say that an organization that planned to communicate securely over the internet would have to have set up their methods in person, in advance, and not do any in-band signalling – which is why the retro-scope scares me: suppose 10 of us set up a conspiracy by walking through a certain place over the course of a month, and trading one-time pads through a dead drop – if they realized that happened then figuring out when the dead drops happened would be enough to tell you the membership of the conspiracy.
There’s always going to be a technique for defeating any security, as there is probably a technique for securing against any attack – it’s just a matter of raising the target or the attackers’ costs unacceptably for them. That’s why I’m so unhappy about this: we see before us ample evidence that they are willing to raise the cost to near-infinite by making it possible to compromise everything. And that’s how hard they are willing to play against their own civilians.
multitool@#28:
And what if everyone uses Signal, even for grocery lists? Does that help the NSA too?
It doesn’t make a damn bit of difference, because they already can detect grocery lists and once the communication layer is bypassed, it’s pretty much irrelevant how one grocery list or another was wrapped. There was discussion back in the day of getting everyone using PGP (because the assumption at that time was that PGP couldn’t be broken) – that would not have helped at all because PGP actually could be broken, at that time.
I am still not hearing any strategy, only one long declaration of defeat.
I didn’t realize it was incumbent on me to offer a solution for an extremely difficult social problem, namely that our society has become a self-perpetuating trap for us. As my next act, will you expect me to defeat capitalism? Or perhaps come up with the final killer strategy that makes everyone acknowledge that gender and racial discrimination are bad? I guess that’s probably the best description of my feelings for the last decade or so: I see the trap and I know how it works, but I did not help build it and I don’t think warning people worked very well.
So, what do ‘we’ do? I actually do think seriously about this, and my answer is that we should probably go on the offense. It’s the only way to cause disproportionate damage and to make the expenses of the police state go asymmetrical. That would amount to engaging in a generalized free-form cyberinsurgency aimed at making computers as unsafe and useless for goverment (and by extension the police state) as it has already, albeit quietly made them for us. It would mean that the cyberinsurgency should be backdooring systems so that they can be caused to fail and leak traumatically if they are used against ‘us’ (loosely defined). It would mean that people in the resistance should be getting jobs in government IT with the specific goal of eventually blowing those systems away in apparent accidents. It would look like: “let 10,000 F-35s bloom!” every government-related and corporatist computer system should experience similar failure rates, delays, and cost knock-ons. Every database should be rife with errors. Every piece of malware should be able to be flagged to reveal itself at an embarrassing moment. Everything should be so irritatingly unreliable and useless that the police state cannot depend on it. They should, in other words, have the same problems with their infrastructure as we do: it was built by a ruthless enemy who doesn’t respect their agenda. Because that’s what we’re dealing with.
How do ‘we’ get there? I’m not sure. I’m at the end of my career, really. If I had a “do over” I’d have taken that job I was offered around 9/11 and would have embedded myself in their data collection flows so that I would now be in a position to compromise them. But as a strategist let me advise you: any time you catch yourself thinking of moves you should have done in the past, you’re wishing you had time-travel, which probably means you’re losing your current engagement at a strategic level.
Andrew Molitor@#7:
And I’m pretty sure a president who shoots spooks is, in practice, a pretty bad idea.
Well, their Vice President would be sworn in pretty quickly after the accident.
Brian English@#1:
You’ve done an Euthrypthro and used synonyms. Rich is powerful is rich.
Well, I’d say that money and power are different things but are often interchangeable. In other contexts I have said “money is a portable form of power” but I don’t think that’s really true – a rich person can find they have no power at all, when a dictator marches in and nationalizes the banks. Then, the rich discover that the exchange-rate between power and wealth can fluctuate very quickly.
So, yes, I’d say they’re related but they are very far from the same.
Now, if you want me to precisely define these things, I will hoist the surrender-flag: I can’t define something as nebulous as “power” in a way I can defend against verbal nihilism. Roughly, I’d say “power” is when opportunity, will, and ability intersect – to have the “power” to do something you must have the opportunity and the will, even if you otherwise have the ability. That definition embeds a difference between ‘arbitrary power’ and ‘constrained power’ – both of which are instances of the occurrence of power. “power” is really complicated in Marcus-land; there are many forms and situations and the term “power” is a broad umbrella used as a placeholder to point toward a lot of them.
polishsalami@#2:
the US Deep State (which I’m told doesn’t exist, btw)
I’m inclined to not believe that the “deep state” exists in the form of a self-recognizing thing. There are processes that people could point toward and honestly say “that’s part of the deep state!” and probably be right. But those things wouldn’t agree that they are part of anything they recognized as a “deep state”
Do you want another helping of waffle with that?
Really, I don’t have an answer I’m comfortable with, about many of these things. In Marcus-land, I call them “emergent conspiracies” – it’s what happens when a bunch of people in positions to make things happen (to a greater or lesser degree) begin pushing in a direction that they want, and cooperating on the edge of their domains. To them, it looks like “I’m just pursuing my beliefs!” and they’re working along with fellow travellers who are pursuing similar beliefs. When you step back, though, their actions appear to be coordinated and intentional – which they are – because they’re pushing toward the same goals. To give you an example of an emergent conspiracy: suppose you had a president who was hated by some and loved by others, who died in an assassination that was obvious, easy, and it was embarrassing as hell (and traumatic!) for those who were supposed to be defending that president. Those people’s actions would orient toward explaining and understanding how it was not their fault, which would result in a search for it being other people’s fault. Eventually, it looks like there is a great big cover-up going on because everyone is trying to shelter their role in the event. It’s a variation of the “nothing ought to be ascribed to malice that can be explained by incompetence” with the added layer thrown in that there are competing agendas at play, crystallizing people’s reactions to the event.
I do not believe the police state is a conspiracy; there is no “deep state” however there are lots and lots of people in position to change things, who take a nationalist and authoritarian view. If they are presented with an opportunity to help push against the damn liberals, or political correctness, or the evil muslims, or the fiendish flouridators – whatever it is – they will nudge the table a bit in the direction of more authority and nationalism. And when they do that, others in similar positions say “wait a minute… this opens up my freedom of action a bit..” and the push becomes a series of little nudges all going in the same broad direction. That’s why, when someone like John Yoo swears up and down that they didn’t mean to encourage torture, they may actually be telling the truth: they may just be dumbasses who were asked a leading question by someone who searched around until they found the right dumbass who gave the desired answer. And the people asking the question weren’t part of some big conspiracy: they were people who were Trying To Get Things Done and looking for a way around a particular road-block. The emergent behavior of a lot of people Trying To Get Things Done in an authoritarian and nationalist way is the kind of disorganized, weird, proto-fascism we are seeing in the US today. It’s like a super-saturated solution, waiting for a crystal to start forming. But it’s not a conspiracy. It’s more like a bunch of swords, ready and sharp, wishing some strong hand would come wield them.
(cool song, BTW. The plaintive tone matches the tone in my head when I think of this stuff!)
Saying that money is synonymous with power strikes me as being similar to saying that sex is synonymous with gender. Just as the latter relies on some kind of gender essentialism to reject the point that there are plenty of individuals where there is a mismatch, so too does the former rely on some kind of sociopolitical or class essentialism, and ignores the fact that there are mismatches.
I am not arguing that there is no strong correlation between money and power; just as there is a strong correlation between sex and gender. I am only arguing that words have meaning and thinking that the two sets of words are completely synonymous is a mistake in both cases.
Incidentally, I was reading this post on abortion rights in Poland, and noticed that the very idea of “gender” is, supposedly, a new and suspiciously foreign concept, and there is a certain moral panic over the very idea of gender nonconformity. Yet I cannot help but think that it’s an example of “fish have no word for water” sort of thing…
Owlmirror@#34:
I am not arguing that there is no strong correlation between money and power; just as there is a strong correlation between sex and gender. I am only arguing that words have meaning and thinking that the two sets of words are completely synonymous is a mistake in both cases.
I agree with you; my problem comes if someone asks me “what is the meaning of that word” and then I fall off a cliff because I know I am talking to one of Sextus Empiricus’ spiritual descendants and they are going to run me around in circles and reveal me for the ignoramus I already know myself to be. Most “essentialisms” depend on defining something circularly (in my experience) and if you pick at the definition the whole thing usually comes to pieces. The collective human experience regarding gender is an example of that, and the reaction of the reactionaries is true to form. Have you noticed that the reaction to attacking pretty much any essentialism seems to be a circular maneuver, claiming first privilege-by-tradition, then privilege-by-exclusionary-definition, and finally privilege-by-external-political-force. (I’m being sloppy by not trying to define those terms, please forgive me)
“gender” is, supposedly, a new and suspiciously foreign concept, and there is a certain moral panic over the very idea of gender nonconformity
Foreign: bad (I would argue that’s a variant of privilege-by-tradition) (does all privilege defense depend on exceptionalism?) Conformity: good
That’s a great article, thanks for sharing it!
I could file that under Aristotelian ‘the exception proves the rule’ if I were so inclined.
Nah, I was just having a bit of fun. Money is certainly convertible into power, but as you say, sometimes all the money in the world won’t help you. But it mostly is convertible IMO.
Marcus:
.
Sorry, man. I’m not trying to be obnoxious, it just comes naturally. :(
.
Anyway all is clear now.
I think physics wins here, but any definition of power should meet the needs of the people using it. Power is the rate at which you do work.
I’ve often thought of powers like physical power, social power, power of the average citizen, financial power, governmental power, power if inheritance, how fast can you get things done?
If society collapses shiny metal, digits on hard drives, or paper will be of no value. You will get things done slowly.