The Obama administration is – brilliantly – punishing Russia for “hacking” the US election by censuring a few intelligence officers and forcing them to close a “luxurious 45-acre compound” in Maryland.[1]
In other words: “We shut down your summer vacation palace, nyuk nyuk!” Holy crap, that’s gonna teach ’em!!

“Closed Permanently” – someone at Google Maps has a sense of humor.
Of course, it’s going to cost the Russians some money (assuming they own the property, and that it’s not a loaner) and they’re going to have to find another love-shack on the Chesapeake Bay. This is not even a slap on the wrist – it’s bizzare – it’s like: “I am waving a wet noodle at your wrist and calling it a flogging!”
I’ve been waiting with bated breath* for the US administration’s retaliation for alleged Russian interference with the 2016 election. And, I’m sure none of you will be surprised that I am disappointed in pretty much every respect. First off, it’s politically weak. Secondly, it’s obviously weak: the US could have used the opportunity to re-engage with the topic of cyberwar standards and treaties among the superpowers (as China and Russia suggested back in 2011[2]) Then, the evidence is weak – I’ll get to that – and lastly, and most importantly, it doesn’t do anything to actually improve the situation. All the US does is sets up the doctrine that “we may retaliate at random if we feel like it” which is a terrible precedent and very poor leadership.
The US has a terrible leadership problem, when it comes to being the pot that calls the kettle “black.” As the world has seen, in the last 5 years, the US NSA and UK GCHQ have decided that their mission is to hack whatever they want. Here I’m not referring just to the Snowden leaks; the US and UK have been pretty unapologetic about (for example) spying on foreign heads of state, diplomatic talks, and corporate negotiations. As Barack Obama said when Angela Merkel complained about the NSA compromising her cell phone, “that’s how it’s done.” I’m surprised that the North Koreans, Russians and Chinese have bothered to say “we didn’t do it!” when accused of cyberattacks when they could just repeat Barack Obama’s Arkell V. Pressdram style response. The US’ inconsistency about complaining also shows poor leadership: when Israeli spies are caught, they are quietly imprisoned with a minimum of fanfare. Meanwhile, the most damaging espionage against US strategic interests remains home-grown: many americans seem willing to sell secrets for bargain-basement prices, or to give them away outright. The US’ efforts against wikileaks (which, nobody in Washington seems to have noticed, is headed by an Australian) are ineffective, yet the accusations against Russia were expanded to, of course, include wikileaks. Wikileaks is being treated as though it were a state.
Here’s what I think the US should have done:
- Begin discussions with China, Russia, and the EU regarding standardization of international cybercrime laws, including defining what actions by governments are illegal.
- Establish a standard of attribution for how the US will determine to its satisfaction that a cyberwar/cybercrime was state-sponsored. This should include the type of system and method descriptions and analysis that will be provided; it should also include third party assessment of attribution. Understanding that evidence for attribution will not usually be of the type that can be presented and challenged in a court of law, it is important to establish how the evidence that does exist is presented, and its quality and reliability.
- Establish a standard of retorsion** for how the US will retaliate for economic or political damage: what is the process whereby the US will assess the damage it has suffered and how will it respond.
- Establish government-sponsored hardened system configuration doctrines for certain critical processes, including political email, file-sharing, and messaging. This would be kept up-to-date including management of vulnerabilities, by the NSA with validation and input from non-government cybersecurity experts.*** The hardened system doctrine would be oriented to provide attribution in accordance with 2) above – i.e.: if there’s a cluster of such systems an attacker can know that they are being watched in various ways and that the results may be presented as evidence, since that evidence has already been established as publication-worthy.
The last point is a serious one: the best way to “hurt” a cyber-opponent is to improve your defenses. It keeps out the riff-raff but also raises their cost to break in, and raises the likelihood that they will be identified credibly if that happens.
What bothers me the most about the administration’s announcement regarding how they are “dealing with” the alleged Russian electoral manipulation: they’re not actually doing anything that will help the problem.
The FBI/Department of Homeland Security Joint Announcement is also pretty lame, and also doesn’t do anything that will help the problem. It’s more of the same finger-pointing as we’ve seen before:
- The alleged Russians used phishing attacks
- The alleged Russians used malware that alleged Russians have used before
- The alleged Russians used IP addresses that are common to other alleged Russians
I know I sound like a broken record but: pretty much every hacker uses phishing attacks, pretty much every hacker uses malware (and the stuff the alleged Russians allegedly used is fairly common malware) and pretty much every hacker uses proxies to access command/control nodes that are compromised systems (and they use the same ones because: why not?).
The DHS/DNI statement, for example, reads:[3]
The recent disclosures of alleged hacked e-mails on sites like DCLeaks.com and WikiLeaks and by the Guccifer 2.0 online persona are consistent with the methods and motivations of Russian-directed efforts. These thefts and disclosures are intended to interfere with the US election process. Such activity is not new to Moscow—the Russians have used similar tactics and techniques across Europe and Eurasia, for example, to influence public opinion there.
Note that WikiLeaks, at least, under the leadership of Julian Assange**** has overtly stated that it was anti-Clinton. So, by specifically mentioning WikiLeaks, the DHS is attempting to imply that they are part of the Russian operation – but that’s contradicted somewhat by WikiLeaks (per Assange) already saying it wanted to influence the election. I have a perfectly credible theory about Assange, namely that he’s an anti-government hipster who appears to hate some politicians slightly more than others – but his actions in that light are consistent: he has been doing whatever he can to hurt the establishment for a decade. I think Assange is a red herring, listed by DHS because the establishment hates WikiLeaks and the “Guccifer 2.0” persona used WikiLeaks as a vehicle for distributing information (rather than an establishment-controllable media outlet like The New York Times, presumably).
The DHS/DNI statement continues later:
Some states have also recently seen scanning and probing of their election-related systems, which in most cases originated from servers operated by a Russian company. However, we are not now in a position to attribute this activity to the Russian Government.
That’s a great big “What The Fuck?” Rephrased: “We don’t have any evidence at all that Russia was involved in probing election-related systems and we can’t attribute it but we’re going to report it anyway.” To my point 2) above, this is why the US should be establishing its practices of attribution: this kind of statement could be broken down into:
- Things we are willing to say and back up with evidence
- Things we are willing to say based on analysis of the evidence
- Things we are not willing to talk about because we lack analysis or evidence
Mixing the last item in with the first two flushes all credibility down the drain. Imagine if a prosecutor tried that kind of argument in a court of law.
That was the October statement from DHS/DNI. Now we have a more sober assessment. And, it’s crap. [4]
This activity by RIS is part of an ongoing campaign of cyber-enabled operations directed at the U.S. government and its citizens. These cyber operations have included spearphishing campaigns targeting government organizations, critical infrastructure entities, think tanks, universities, political organizations, and corporations leading to the theft of information. In foreign countries, RIS actors conducted damaging and/or disruptive cyber-attacks, including attacks on critical infrastructure networks. In some cases, RIS actors masqueraded as third parties, hiding behind false online personas designed to cause the victim to misattribute the source of the attack.
The claim is that RIS (Russian Intelligence Services) are hacking US organizations and are doing what intelligence services appear to do all the time – including hiding behind false online personas intended to encourage misattribution. In other words, they’re doing what the Chinese and the North Koreans and the NSA are doing.
The U.S. Government confirms that two different RIS actors participated in the intrusion into a U.S. political party. The first actor group, known as Advanced Persistent Threat ( APT ) 29, entered into the party’s systems in summer 2015, while the second, known as APT28, entered in spring 2016.
This bothers me a lot. When security analysts are identifying and naming a threat actor, what they’re trying to do is establish methods and timelines that argue that their actions are related. The existence of a threat actor, however, is a construct in the security analyst’s mind – it’s an arbitrary grouping – especially if the grouping includes things like command/control IP addresses and tools. Let’s say that the difference between APT29 and APT28 is that they used different command/control IP addresses – that doesn’t mean they’re actually different! It just means that some analyst somewhere said, “let’s treat these as two different groups.” Unless we know the criteria by which the analysis was clustered, we can’t make a meaningful assessment of any of this analysis. For example, Bill Cheswick once established to his confidence that an attacker was a student because their activity levels varied with spring break and summer vacation. That’s an interesting and provocative bit of analysis but it is not sufficient to say with high confidence that the attacker is a college student – it could be that the attacker has decided to simulate a college student; that’d be easy. A big problem with any of this analysis is that if the attacker knows the criteria that the analysts will be using, it’s ridiculously easy to manipulate the analysts by simulating the criteria.
This picture from the report needs some translation:
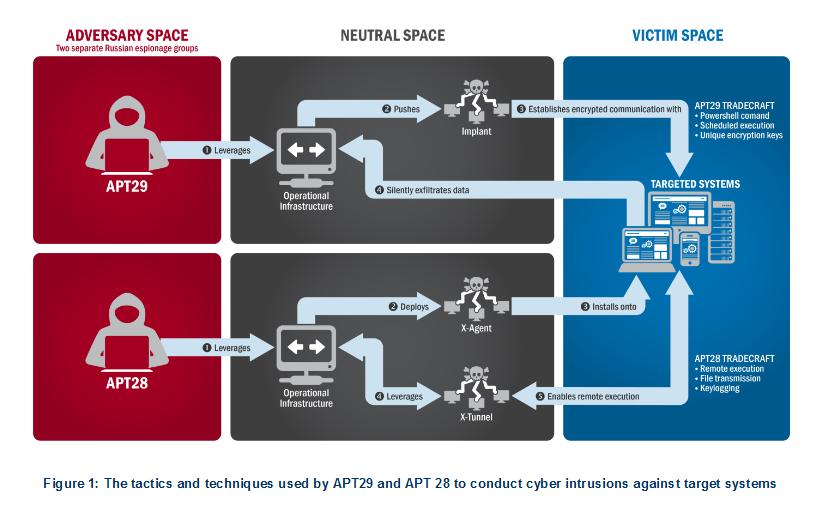
It says: “We think there were two groups of hackers. They used the internet (Neutral Space) and both attacked targeted systems using slightly different techniques that are common to all hackers.” It’s a pretty illustration but it conveys no useful information except that it appears that the criteria used by analysts to decide APT29 and APT28 are different is that they use different tools, became active at different times, and there was technological overlap between their methods. They don’t explicitly say the last piece but it’s important: if I can access your files using Method A, I’m not also likely to access your files using Method B because I already accessed your files with Method A and that worked perfectly fine.
Both groups have historically targeted government organizations, think tanks, universities, and corporations around the world. APT29 has been observed crafting targeted spearphishing campaigns leveraging web links to a malicious dropper; once executed, the code delivers Remote Access Tools (RATs) and evades detection using a range of techniques. APT28 is known for leveraging domains that closely mimic those of targeted organizations and tricking potential victims into entering legitimate credentials. APT28 actors relied heavily on shortened URLs in their spearphishing email campaigns. Once APT28 and APT29 have access to victims, both groups exfiltrate and analyze information to gain intelligence value. These groups use this information to craft highly targeted spearphishing campaigns. These actors set up operational infrastructure to obfuscate their source infrastructure, host domains and malware for targeting organizations, establish command and control nodes, and harvest credentials and other valuable information from their targets.In summer 2015, a APT29 spearphishing campaign directed emails containing a malicious link to over 1,000 recipients, including multiple U.S. Government victims.
That’s it?
- They used spearphishing, like every other hacker ever.
- They broadly targeted 1,000 targets, like every other hacker ever.
- They used URL encoding, like every other hacker ever (it helps hook the phish).
- They exfiltrate information, like every other hacker ever.
- They use the exfiltrated information and credentials to further craft targeted spearphishing attacks, like every other hacker ever.
- They establish command/control nodes, like every other hacker ever.
- They obfuscate their source infrastructure, like every other hacker ever. (I assume this means that they’re accessing their command/control nodes through one or more proxies, like every other hacker ever.)
The main difference appears to be that APT28 likes to phish people to a site that drops malware on their machines, while APT29 likes to phish people to a site that looks like someplace they normally go, to harvest their login/passwords. Some hackers prefer the latter, others the former, and some do both.
In the course of that campaign, APT29 successfully compromised a U.S. political party. At least one targeted individual activated links to malware hosted on operational infrastructure of opened attachments containing malware. APT29 delivered malware to the political party’s systems, established persistence, escalated privileges, enumerated active directory accounts, and exfiltrated email from several accounts through encrypted connections back through operational infrastructure.
Like every other hacker ever! This is how it’s been done since about 2002 or so: you carpet-bomb a link to a malware dropper, and you get a few gomers, then you see what you’ve caught and exploit the most exciting ones. So someone sent someone at a US political party some malware, and they opened it, and some hacker did like every other hacker ever. I’m still waiting to see how and why this is Russians. In fact, the methods described are the exact same methods that the Chinese that hacked OPM North Koreans that hacked Sony kid down the street uses. How do they know this was Russians and not North Koreans?
I really need to emphasize that this is standard operating procedure. The penetration testers that I know use exactly the same techniques, as do the hackers.
This time, the spearphishing email tricked recipients into changing their passwords through a fake webmail domain hosted on APT28 operational infrastructure. Using the harvested credentials, APT28 was able to gain access and steal content, likely leading to the exfiltration of information from multiple senior party members. The U.S. Government assesses that information was leaked to the press and publicly disclosed.
Sending someone to a fake webmail domain hosted on a compromised server is standard hacking operating procedure.
Next comes some incredibly sloppy work: (still from [4])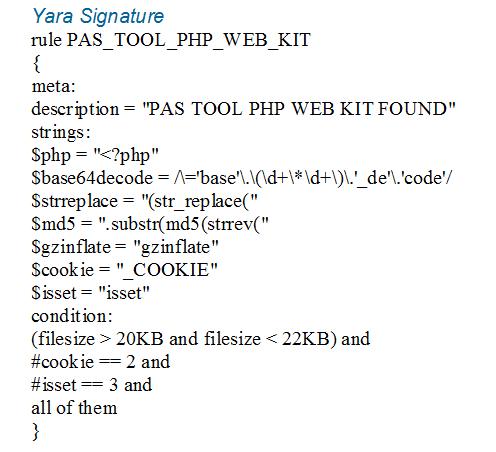
A YARA signature is an abstract matching rule that can be converted to run in a log, file, or network analysis tool to detect patterns that are “Indicators Of Compromise” (IOCs) This Yara signature identifies that a system has the “PAS TOOL PHP WEB KIT” if the system being examined contains a PHP file of a certain size that contains a set of patterns. In other words, you’re to run this and see if you have that particular web backdoor installed on your machine.
I’ve encountered this sort of web backdoor several times while doing incident responses. The last one, by the way, had Romanian comments, Romanian variable names, and the IP address from which it was being controlled was in Romania. The activity was during late afternoon/late night time windows in Romania. I’m still not willing to say that it was a Romanian doing it.
Anyhow, this particular web kit uses gzinflate and some typical strings. I’m glad that the intelligence community isn’t claiming that this was written by the same people who hacked Sony because they’re both using gzinflate (like tons of other web software!) That, by the way, was part of the high quality attribution that led the FBI to conclude that it was North Koreans that were hacking Sony: North Koreans apparently like to use a certain drive-wiping program. Guess what? So does pretty much every hacker ever, who wants a command-line drive-wiper.
The rest of the Joint Analysis Report is some “SECURITY 101” stuff about how not to get owned. That’s it. I still don’t see a single damn thing in the report that argues conclusively that the attacks were from Russia, let alone sponsored by the Russian Government. The best argument in the report is that: Russia appears to have benefitted from having the US look stupid. Guess what? The list of countries, individuals, and hackers that benefit from having the US look stupid would take several trainloads of paper to print out.
Here’s what is going to happen: next election, the deluge. Because the US still hasn’t done anything to improve the situation and now everyone can see how terribly weak the security is, on the systems that are used by the rulers of the US. That’s why the strategy the US has been pursuing is so damaging: let the NSA off the leash to hack the world, but don’t improve our own security at all. It’s the Department of Glass Houses telling the Department of Stone Throwing to go throw rocks at everyone they want to, and assuming there’s going to be no blowback.
 I actually like seeing the US political system revealed for the cynical sham that it is. That doesn’t mean that I hacked anyone. It also doesn’t mean I influenced the election. At all. Because my popular vote didn’t matter. Maybe next election I’ll come off the bench and fuck with some oligarchs. What’ll the government do, take away the Saudi’s summer house?
I actually like seeing the US political system revealed for the cynical sham that it is. That doesn’t mean that I hacked anyone. It also doesn’t mean I influenced the election. At all. Because my popular vote didn’t matter. Maybe next election I’ll come off the bench and fuck with some oligarchs. What’ll the government do, take away the Saudi’s summer house?
What would an attribution look like that satisfied me? It’s complicated but there’s no way of getting around it without disclosing some intelligence information. Not much, just a bit. It would look like this:
“On this date at this time, we monitored a connection that originated in the network cloud belonging to Runet’s fixed IP range. We have observed that address engaged in multiple hacking attacks in the past; that fixed address appears to be a Linux system named whatever.runet.ru and (information about the system) During the particular attack we are describing, a connection via SSH went to a staging server in Amsterdam, which then launched a VPN proxy connection to a host in Dallas, Texas (information about the system) that appears to be a compromised home computer. The attackers made the mistake of using the same staging system and compromised system and we were able to execute search warrants or secure cooperation from the administrators of those machines, from which we recorded additional traces. The attacker then sent a phishing email to the target, which led them to a malware dropper on the staging server (details of dropper) (copy of phishing email). The malware dropper compromised the end user’s system, and the user’s exchange email was exfiltrated in a .ZIP file that was emailed to the staging server (system log lines) The contents of the emails collected were posted on Wikileaks on dd/mm/yy and exactly match the files collected. Following that, we executed a compromise against the linux server whatever.runet.ru using an unpatched system vulnerability, and collected a mirror of its hard drive. On that drive we found (copy of email) emails from the user who compromised the systems, the files that were collected, a tools archive of hacking tools, and emails from them to one name_withheld, who is an intelligence officer working for military intelligence.”
Dropping a load of detail like that would be pretty convincing: establish multiple points of view, a command authority linking it to an agent of a government, etc. It would require disclosing that the NSA monitors communications all over the place and has backdoored systems all over the place – which we already know, but they want to pretend isn’t the case. That’s the problem: it’s really hard to attribute a complaint that someone is hacking you when the way you attribute it is by hacking them first. But if you think about it, the only way that the US intelligence community could plausibly attribute the Sony attacks to North Korea would be with a statement like: “North Korea has 4 internet links and we so thoroughly own them that we have every packet that goes back and forth. So, here’s a reconstructed stream of a system on a North Korean military network attacking Sony.”
Tell us as much about “Guccifer 2.0” as we now know about hacker-turned-FBI-informant Hector Monsegur, AKA “Sabu.”
Here’s the big problem: the Russians know this and so does the US. The US and Israel were very careful hiding the tracks of Stuxnet, which we now know is the tip of a nasty iceberg attributable to “The Equation Group” which actually is implicated in developing tools for some US agency that is actually using them to penetrate foreign systems. If you look at the deconstruction of how the Equation Group’s code-trees evolve (stuxnet, duqu, etc) you can see a good example of the kind of attribution that the US intelligence community could and ought to be providing as evidence against the Russians – if they had that quality of evidence. I don’t think they’re doing it, because they actually don’t have any evidence that’s worth a hill of politician’s promises.
So here’s another bit for you: since I said earlier what I think the US should have done, I’ll say what I’d do if I were the Russians. I’d compromise the fuck out of as much of the NSA’s expensive custom-built malware as possible. I’d have intelligence officers feeding code samples of Equation Group code to every antivirus vendor that’s not headquartered in the US. I’d be dropping solid evidence linking the NSA to all the stuff Snowden told about, proving that it’s real. I wouldn’t be dropping it to the US lapdog media, I’d be giving it to the Germans, the French, the Chinese, and – actually – the Russian IT security people, too. Want to bet the Germans would find out they’ve been being spied on? Want to bet the Brazilians would wonder if their politics are being messed with? And, eventually – you know it’d happen – someone would sell the key to some of the deeply embedded trojan horses that NSA has apparently put in certain hard drives and in some systems. And I’d publish the keys, the code, and evidence of its origin. Because you know whose infrastructure is most exposed? Yep: The Department of Glass Houses. It’s the response from Arkell V Pressdram.

(* A lie.)
(** Retorsion (from French: rétorsion, from Latin: retortus, influenced by Late Latin, 1585–95, torsi, a twisting, wringing), a phrase used in international law, is an act perpetrated by one nation upon another in retaliation for a similar act perpetrated by the other nation.)
(*** I’ll note that this has already been done; it’s just ignored by important people, who later regret it. They’d need to dust off some of the work DISA and NIST and NSA have already done and bless it as a “how to” for organizations that are afraid of international espionage. They’d also have to resist the temptation to let CIA and NSA backdoor it.)
(**** It is deliberately difficult to tell how much Assange controls WikiLeaks. But as its spokesperson he has some control over WikiLeaks’ political impact.)
[1] Washington Post: The Luxurious 45-acre Compound in Maryland is being shut down for alleged Russian espionage
[2] Arms Control Association: China and Russia submit Cyber Proposal (The US’ response was that China and Russia were trying to control open and unfettered access to the Internet and that their proposal was an attempt to derail the US and Great Britain from establishing their view of how it should be done. Which is probably true. But, that doesn’t mean the US and Great Britain are the only players in cyberspace!)
BBC: London Hosts Cyberspace Security Conference (“Foreign Secretary William Hague convened the London Conference on Cyberspace, and urged a “global co-ordinated response” on policy.” – as long as it’s not from the Russians or the Chinese)
Letters of Note: Arkell V Pressdram
Newsweek: Israel Won’t Stop Spying on the US
Bloomberg: Russia’s “Grizzly Steppe” Cyberattacks Started Slowly, US Says
[4]OODA Loop: DHS-FBI Joint Analysis Report on GRIZZLY STEPPE Russian Malicious Cyber Activity [PDF]

It’s hard to see anything to this other than:
(a) Obama creating drama to spite Trump, and
(b) The Dem Establishment creating a diversion from their own massive failures during the election
polishsalami@#1:
The national security state is very concerned about how its data is leaking and how insecure its systems are. It makes it hard to build the great big nest of secrets that they depend on to protect them from public scrutiny. None of this is actually about Russia – I think it’s a play to get more funding (which will be wasted) for cybersecurity.
ADDENDUM:
Apparently some of the russians sanctioned are cybercriminals. Because, uh, something something interfere with US elections
http://www.foxnews.com/world/2016/12/30/two-russian-criminals-hit-with-us-sanctions-are-on-fbi-most-wanted-list.html
In other words: generalized revenge rage-flail.
… the Russians have used similar tactics and techniques across Europe and Eurasia…
So categorically precise, these persons!
… Assange … has been doing whatever he can to hurt the establishment for a decade.
When’s the last time WL uncorked a bottle of Republican farts?
… we are not now in a position to attribute this activity to the Russian Government.
Didn’t these same people just claim they *know* Putin put in his input?
Figure 1…
Ooh, really bad baddies – skulls&crossboneses and hoodies!
filesize > 20KB and filesize < 22KB…
Jesus Christ and his Mariachi Band! You can really hide from a malware scan by stirring in a couple of kilobytes of monkeypuzzle code or ascii-dump?
… Stuxnet, which we now know is the tip of a nasty iceberg attributable to “The Equation Group” …
Got any linkology to share on this?
Pierce R. Butler@#4:
Got any linkology to share on this?
I’m not sure if there’s anyplace that pulls that whole story together into a coherent thread. I should do a posting on it, but I’ve avoided attempting doing so because it’s so complicated and it’s easy to get a fact awry. It’s hard to know what the facts are, really.
Briefly: the US Government has pretty much acknowledged that it was behind Stuxnet.
http://arstechnica.com/tech-policy/2012/06/confirmed-us-israel-created-stuxnet-lost-control-of-it/
I predicted that almost a year beforehand, because the US is one of the few places that has Pakistani RP-1 style centrifuges to test against (they got them from Libya when Ghaddafi shut down their nuke program, and have been sitting in Oak Ridge ever since…)
But it’s more complicated. Because Stuxnet appears to be a code branch from a line of malware with various other branches: flame, duqu and gauss.
http://www.nytimes.com/2012/05/31/technology/researchers-link-flame-virus-to-stuxnet-and-duqu.html
https://www.concise-courses.com/stuxnet-flame-gauss-duqu/
This presentation is pretty good (from RSA conference)
https://www.rsaconference.com/writable/presentations/file_upload/br-208_bencsath.pdf
slide 15 is a good example of how to analyze this stuff…
Then you have Snowden’s dump of stuff, which included slides that talk about TAO tools (tailored access operations – i.e.: hacking) and those tools crop up, by name and purpose, in the shadow brokers’ dump of NSA code. Shadow brokers situation is not fully understood yet (by anyone!) but it may be that someone hacked NSA compulsive data-hoarder Harold Martin
http://www.nytimes.com/2016/10/20/us/harold-martin-nsa.html?_r=0
That is based on some interesting reasoning: the tools in the shadow brokers dump are specifically dated to the same time as the copies Martin had; they’re not the latest versions which argues that the shadow brokers don’t have access to the actual NSA systems and may be working from second-hand stolen archives.
So, you have flame/duqu/stuxnet/gauss which appear to be branches developed by the same state actors, who are widely attributed to the US or Israel. And you have the shadow brokers dump which includes stuff that was developed by the so-called “equation group” because of some code signatures that appear in multiple places. And shadow brokers call them “equation group” too, clearly they are reading the same news as the rest of us.
Then it all sort of comes to a point at the end: equation group (per Kaspersky labs) appear to be the developers of stuxnet, also:
http://blog.cybersecuritylaw.us/wp-content/uploads/2015/02/Equation-Group-Kaspersky-Report.pdf
If that’s correct then that’d mean the US and Israel have been engaged in a joint operation that is huge.
It’s going to get trickier in the future of course since post shadow-brokers leaks now there will be random malware authors lifting codebits from equation group or trying to make their code look more like equation group’s.
I can’t tie all the pieces together but the deconstruction of the components of the various trees of malware is significant to me. As a programmer, I know that code structures don’t just happen organically – all the code I’ve written in my career contains bits of old routines and techniques that are self-similar and my overall structures look similar. It’s like how John Fogerty music all sounds like John Fogerty Music not Stevie Ray Vaughn. So when I see the analysis of malware components and the pieces are there like that, I accept that the code is from a common repository. I assume there is a group of people developing a common framework then plugging components into tailored malware (that’s basically what Snowden says the NSA says it’s doing, too) It looks similar because it’s common components being reused. When I talk about solid attribution, this is the kind of thing I’m looking for: detailed analysis of the code and modules – not “it came from Russia, hurr hurr” Look, for example, at the Kaspersky report, page 4: that’s a very detailed and unusual use of a hashing algorithm that is repeated in several pieces of malware. That’s how to attribute code! The Kaspersky report (page 5) has a nice illustration of how all the bits fit together.
Schneier also has some measured views on the equation group/shadow brokers situation:
https://www.schneier.com/blog/archives/2016/08/major_nsaequati.html
Comparing the level of technical detail and the overall analysis between what the security community is doing with stuxnet and equation group code, to the US government’s attribution on election manipulation ought to be really instructive. If I may plug some of my other work in other blogs, I did a piece on attribution here:
https://fabiusmaximus.com/2011/10/21/30004/
which I may revisit here if it’s interesting.
If you think this would be worth a full post I’ll do it someday, but it’s going to have to be heavily larded with “could be” and “may be” and “we don’t know” I hate the level of artificial certainty we hear from the US government and I’d encourage anyone who looks into this matter to compare the measured skepticism and analysis of the security community with the FBI’s “proof by vigorous assertion” and “believe us, we’re the FBI that’s why.”
Pierce R. Butler@#4:
Didn’t these same people just claim they *know* Putin put in his input?
That’s based on the observation that Putin is a control freak, like the rulers of the US, and none of his minions would presume to do something like that without his approval. Therefore, he must know what happened and must have ordered it.
You know, like how the CIA did the Bay of Pigs invasion.
Just kidding.
From NYT: http://www.nytimes.com/2012/06/01/world/middleeast/obama-ordered-wave-of-cyberattacks-against-iran.html
So, yeah, control freaks gotta control freak. Therefore, PUTIN DID IT!
PS – the leaker who blew that little secret: slap on the wrist.
http://foreignpolicy.com/2016/10/17/obamas-general-pleads-guilty-to-leaking-stuxnet-operation/
If you think this would be worth a full post I’ll do it someday…
Just following the links given here now will provide hours o’ fun for the whole family already, thanks…
Hey Marcus,
…
The problem with the entire line of reasoning among cyber folks is that we see all the issues through our own lens. I don’t believe answers lie in that direction.
…
Attribution through purely digital means isn’t something that is going to be resolved to the satisfaction of our community barring vast and (at least for a long time) unlikely changes to the tech we use. The level of nested “yes, but”s to resolve before we would all be comfortable saying “yeah, that really was Bob” based on purely digital information is fractal in scope. Is there a digital record of video showing Bob at the keyboard of that machine at that time? Can we see Bob’s fingers hitting the appropriate keys? And how do we know that video is real, anyway?
…
For cases like this it isn’t all about Bob *getting* the information, anyway. If Bob is a government agent then he’s just doing what spies have always done, gather gather as much as he can get until his gatherer is sore. How Bob’s *boss* uses that information is what determines whether it is garden variety espionage or ultimately an act of aggression.
…
As usual, you and many among our merry band make a lot of good granular points (international norms, enunciated national responses, making systems suck less…), but we stereotypically miss the points that matter most:
…
1. We’ll all be shouting at our nursing home workers long before digital-only attribution isn’t a philosophical debate.
…
2. Geopolitically, it isn’t about how the spies (hack the server, steal the briefcase, copy the scroll) get the information, it’s about what nations do with it.
The political and legal ramifications of this are going to be felt for a long time. We now have the full force and authority of the Executive Branch of the USG being wielded based upon some pretty weak attribution.
My fear with this is the precedent that it will establish for the Trump administration. Want to deport some people? Just dig up some of that cyber attribution stuff! Want to strip someone of their citizenship? I think there has been some attributable cyber activity from that guy’s IP address!
I also question anyone’s ability to keep Obama’s electronic systems and communications safe from now on. Vlad has a long memory, and will surely retaliate at some point. That would definitely be the ultimate cyber challenge in the next few years!
Aaron T@#9:
My fear with this is the precedent that it will establish for the Trump administration. Want to deport some people? Just dig up some of that cyber attribution stuff! Want to strip someone of their citizenship? I think there has been some attributable cyber activity from that guy’s IP address!
That’s exactly why I am concerned about this stuff. It amounts to McCarthy’s “little list” – you can declare anyone to be a hacker, and then retaliate without further evidence. In the case of the Russians that were censured: apparently some of them are electronic crimes fraudsters and not spies at all. The Obama administration took advantage of the opportunity provided by the “Russia spies” to seize assets belonging to fraudsters and bypassed the pesky international legal system in the process.
I also question anyone’s ability to keep Obama’s electronic systems and communications safe from now on. Vlad has a long memory, and will surely retaliate at some point. That would definitely be the ultimate cyber challenge in the next few years!
I expect to see NSA begin leaking like a sieve, along with lots of professional deconstruction of Equation Group’s tools to reliably attribute Equation Group to NSA. The easy/obvious counter-attack to the US accusations is to document US hypocrisy. The Chinese, being the strategic masters that they are, will sit by patiently and watch, then make whoever looks least bad coming out of it look worse.
Chris Blask@#8:
The problem with the entire line of reasoning among cyber folks is that we see all the issues through our own lens. I don’t believe answers lie in that direction.
Heya Chris! Nice to hear from you! Hope you are well, etc…
Yes, I agree. But we can only do what we can do in our respective domain. As a security practitioner I can’t do much to influence the US’ foreign policy (or the Russian’s, either!) So, we all contribute in our way. My way is by pointing out that our foreign policy is not best served by using cybersecurity in this particular way, and that if we’re going to continue to make this sort of decision, our systems need to be a hell of a lot better, to survive the inevitable blow-back.
ADDENDUM:
The Intercept has a good review of the Kaspersky report I referenced above, which technically connects “Equation Group” to NSA.
https://theintercept.com/2015/02/17/nsa-kaspersky-equation-group-malware/
I find Kaspersky’s analysis to be credible (and a lot better than the US government has been providing regarding “Russian” and “North Korean” hackers!) which would mean that the NSA’s been conclusively attributed as engaged in the same sort of attacks as the “Russian hackers” only much, much, larger scale)
It’s sad that every time someone asks me for an example of what good technical attribution work looks like this week, I’ve had to point them to Kaspersky’s Stuxnet and Equation Group work. There really is not any good work from the US side since Mandiant’s APT stuff years ago.
Regarding the Chinese patience play, it will be interesting to see if their domestic affairs and trade leaders will let the cyber folks be patient. If Trump blows up the magic China-to-Walmart economic boom, there may be a limited fuse on their ability to wait out the Russians. If they become actors in the mix, it will be interesting to see how many Chinese cyber operatives learn how to use Cyrillic keyboards.
Point #4 seems like it should be credible but in practice wouldn’t be. Too many of the three letter acronym crowd have been pushing for blatantly ridiculous nonsense in the public sphere, like removing encryption. And as tempting as it is to think so, I don’t believe any of them are really that dumb or incompetent.
But once you rule out irrational thought processes, the only way I can think of to reach the conclusion that you should push back on encryption is that you’ve already cynically weighed the potential for others taking advantage of this and found it acceptable. Which would make break-ins like this an acceptable risk. And while only targets the acronym crowd want to actually protect would be mandated to use this, unless they hide it away (and good luck with that) it’s going to get used elsewhere, increasing the perceived benefits to watering it down to the above way of thinking.
I know there are competent and reliable people working in these agencies but there are also people demonstrably willing to sell us all down the river to forward their own agendas. It erodes their credibility when they try to do something serious and useful like this would be.
lanir@#14:
I know there are competent and reliable people working in these agencies but there are also people demonstrably willing to sell us all down the river to forward their own agendas. It erodes their credibility when they try to do something serious and useful like this would be.
I agree with your whole comment. Including about point #4: the three letter agencies are basically lazy – they want the easiest possible path to accomplish what they want to accomplish (and laws or propriety be damned) Eroding everyone’s encryption is simply one step in a long target analysis for them. But what you’re saying (and I agree with it) is that they’re siding against the state, in that they’d rather see it compromised for their convenience than protected for others’ inconvenience. That also matches current events so I am inclined to think that’s what’s going on.
The big problem is that the people in those agencies who are willing to sell everyone down the river are the bosses. There are some good people down in the trenches, but they’re “just following orders” and those orders are often illegal, frequently corrupt, and generally unwise.